📸 Screenshot Gallery (36 images)
Click any thumbnail for full-size view with lightbox navigation.
Click any thumbnail for full-size view with lightbox navigation.
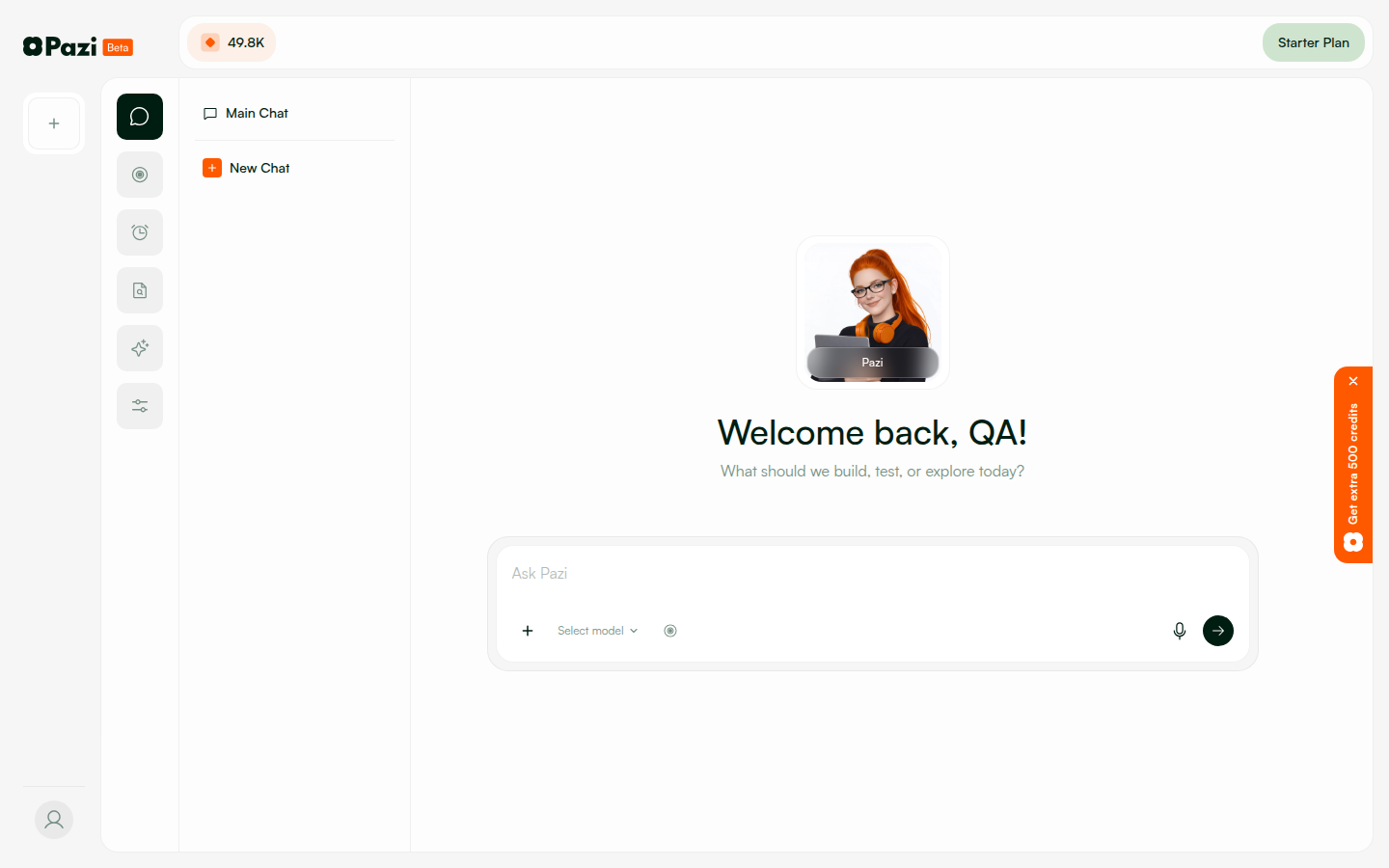
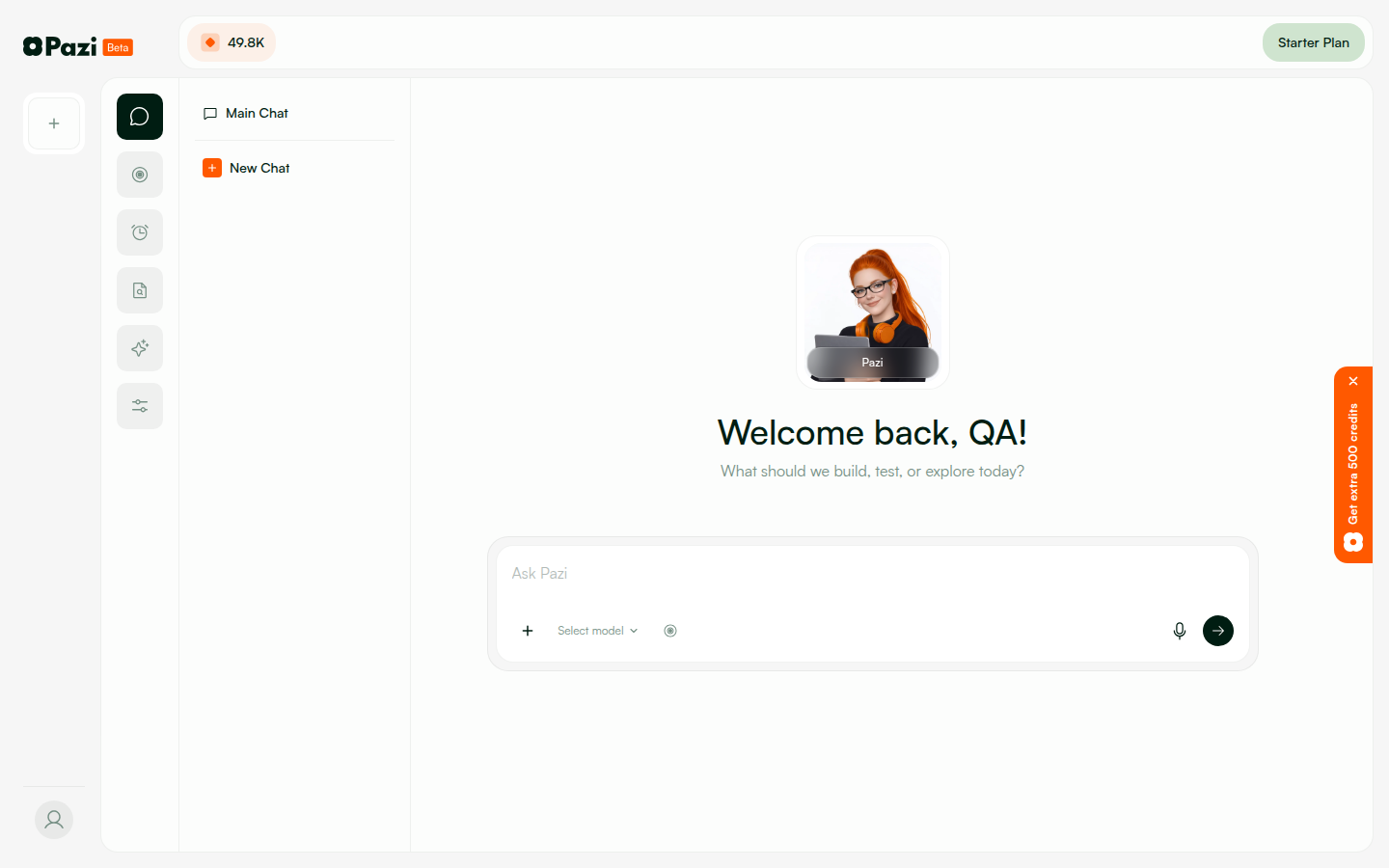
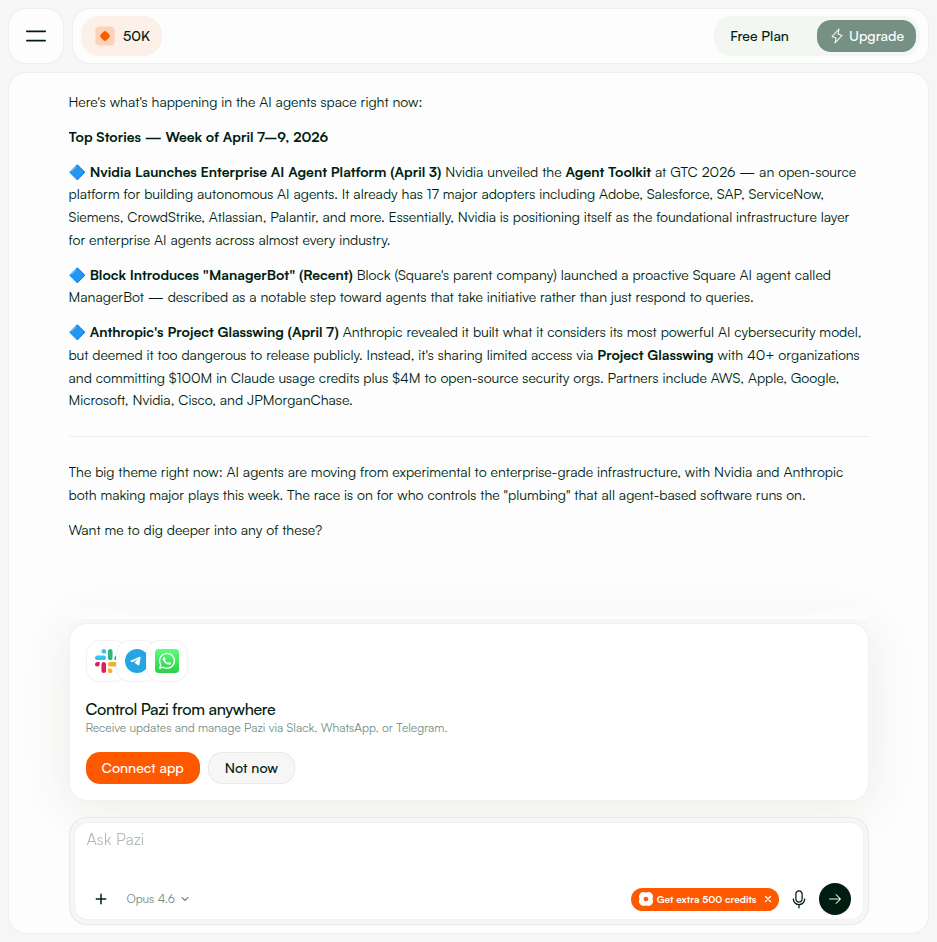
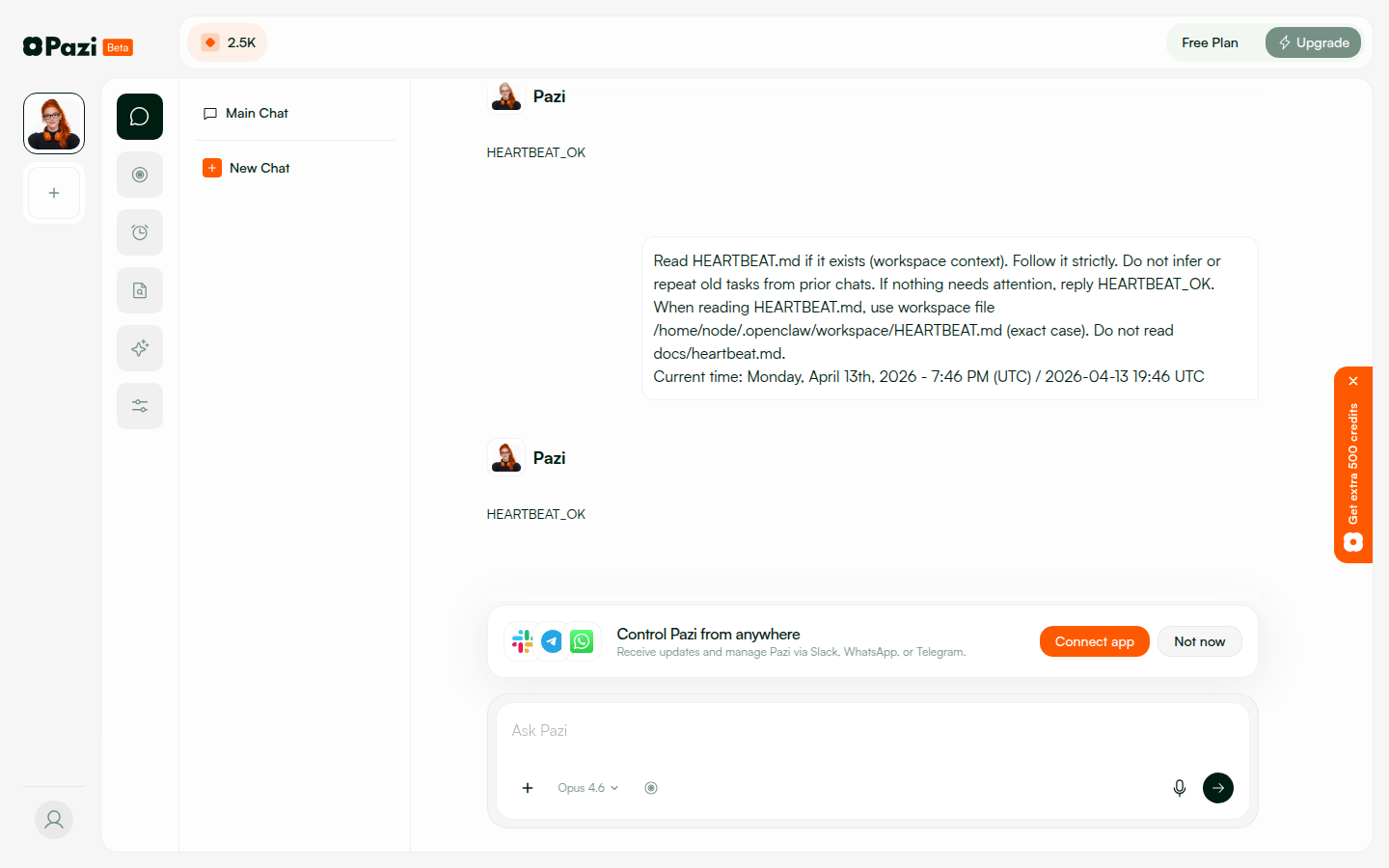
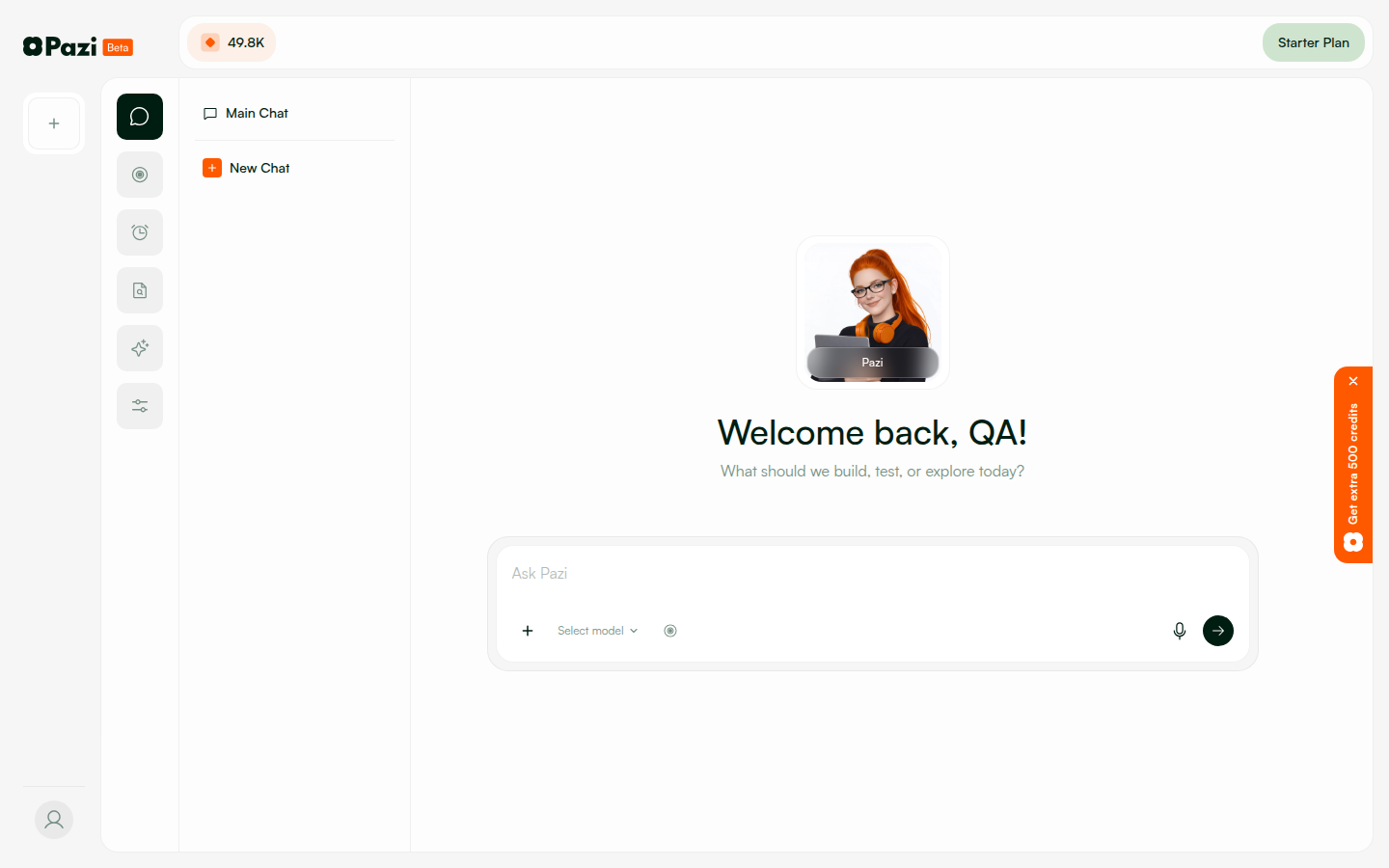
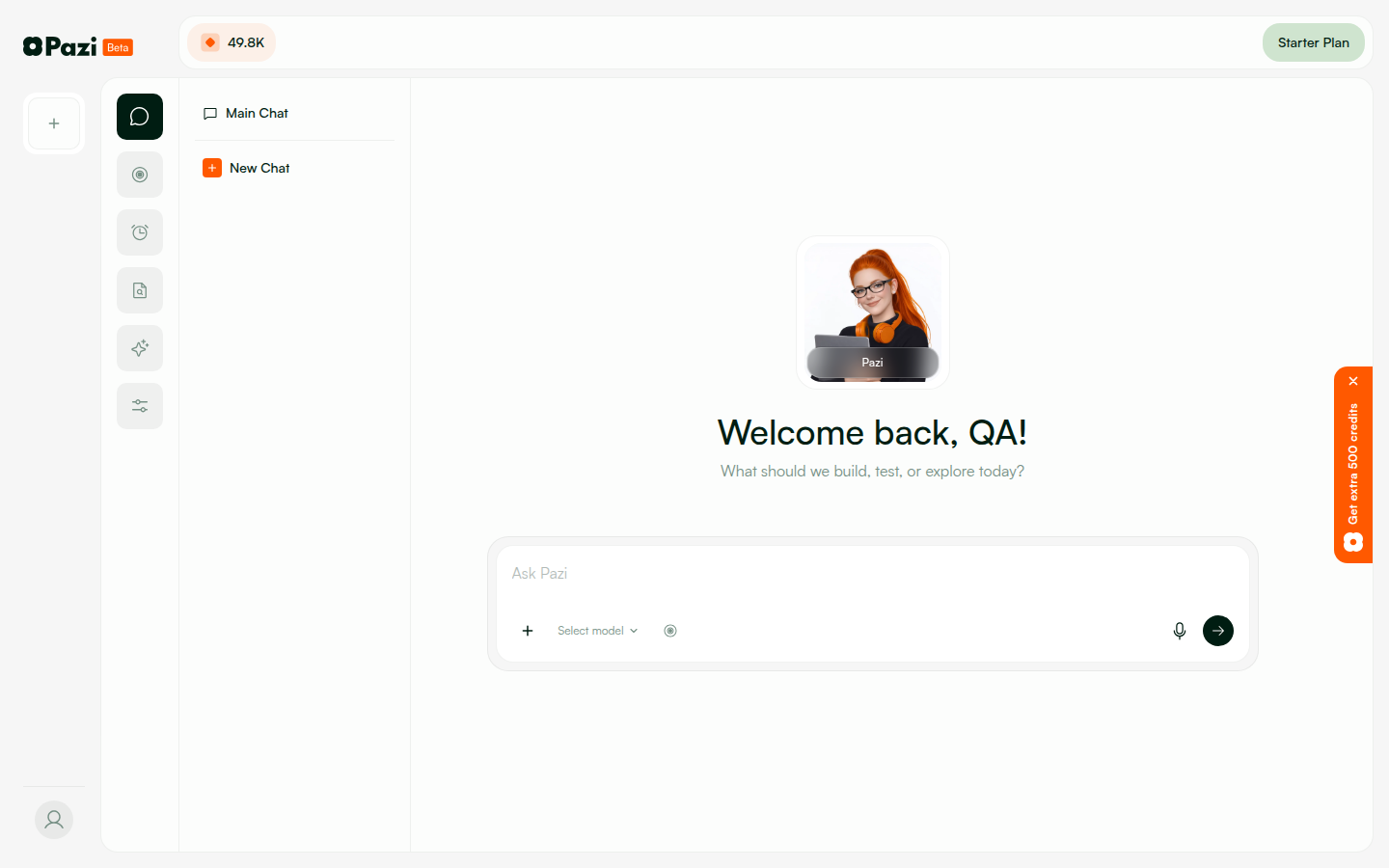
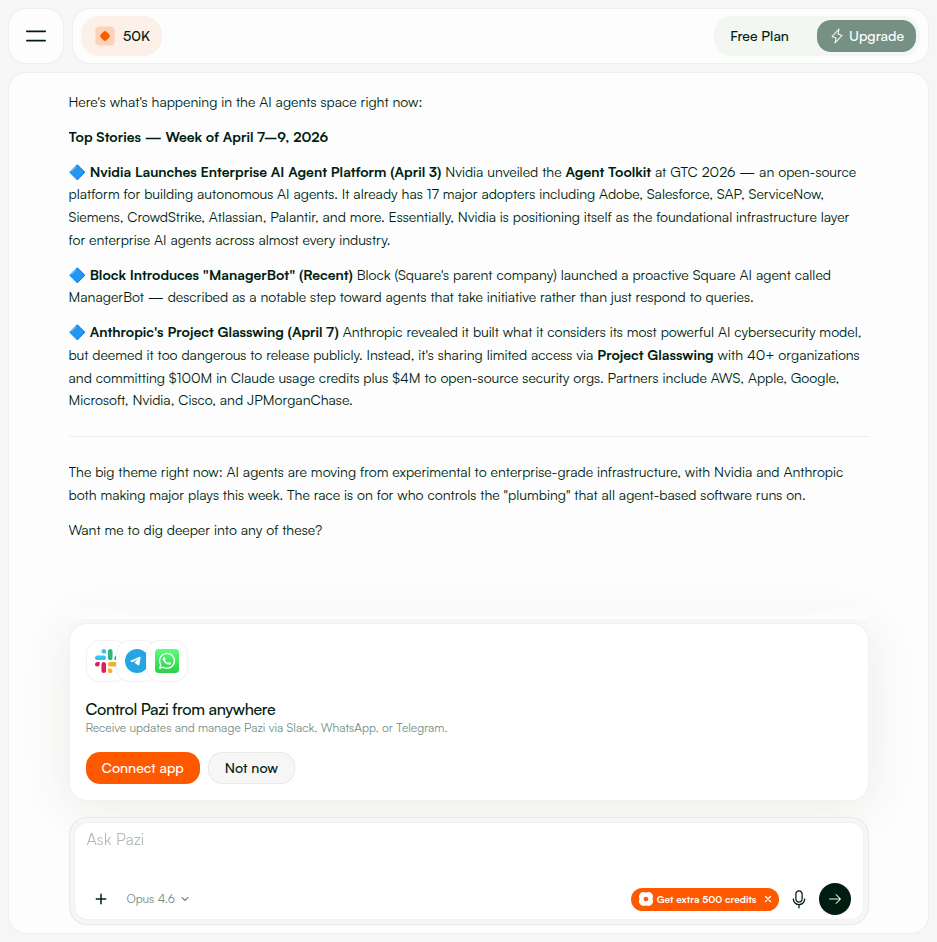
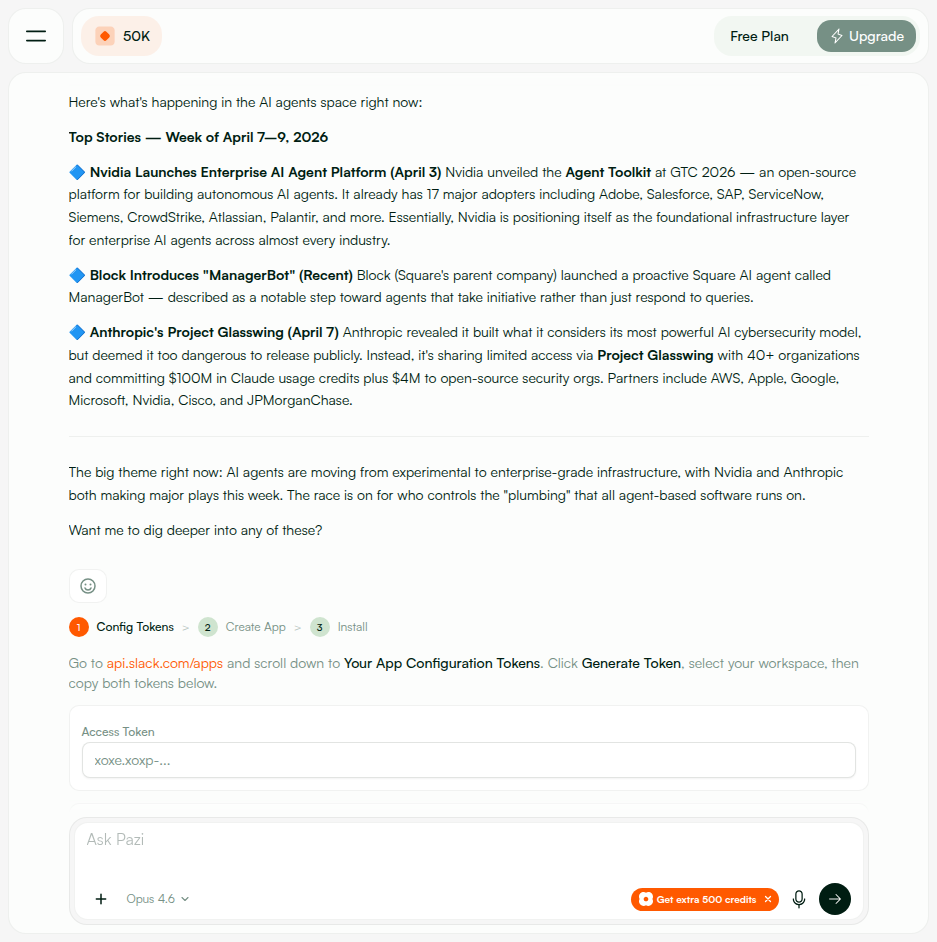
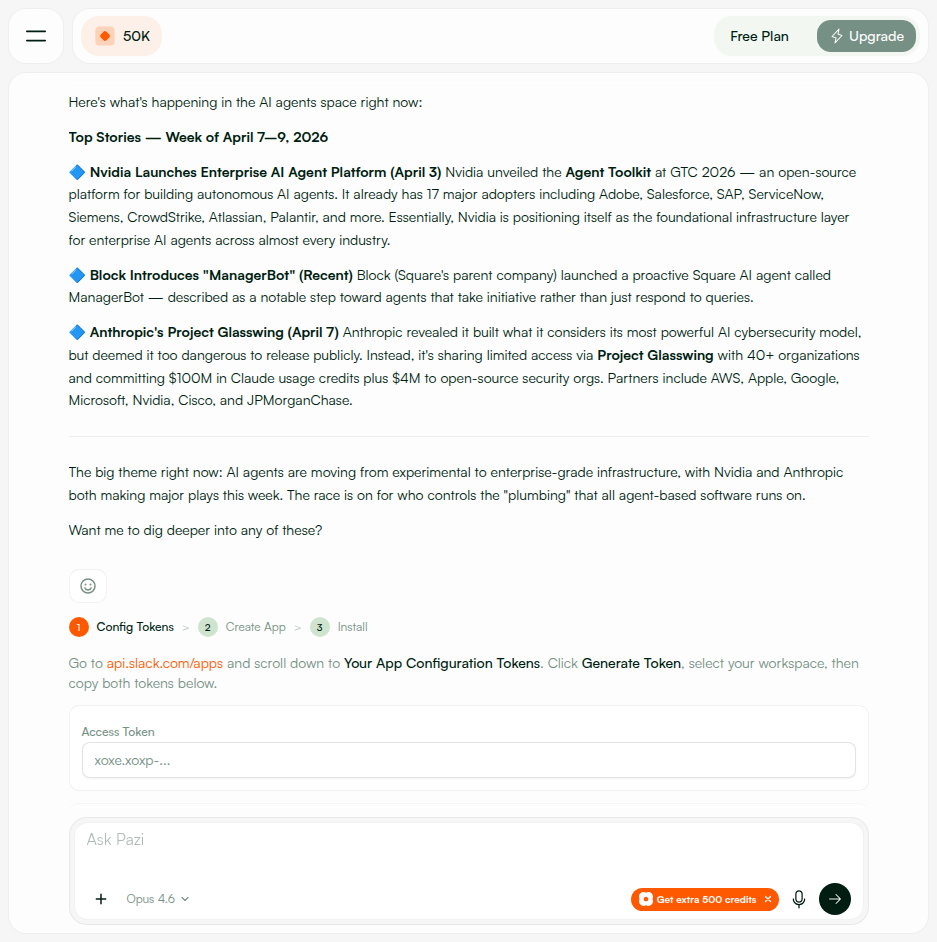
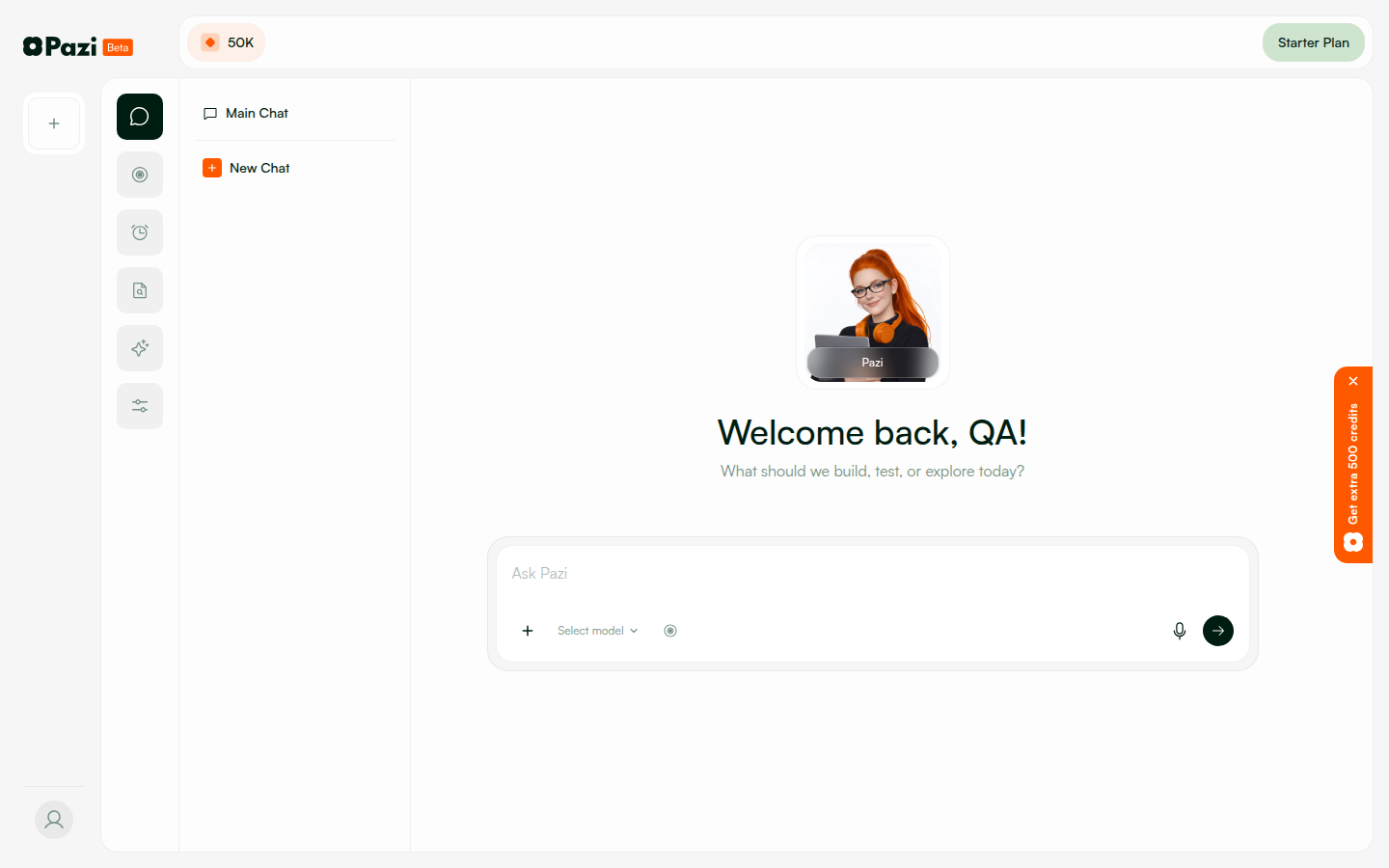
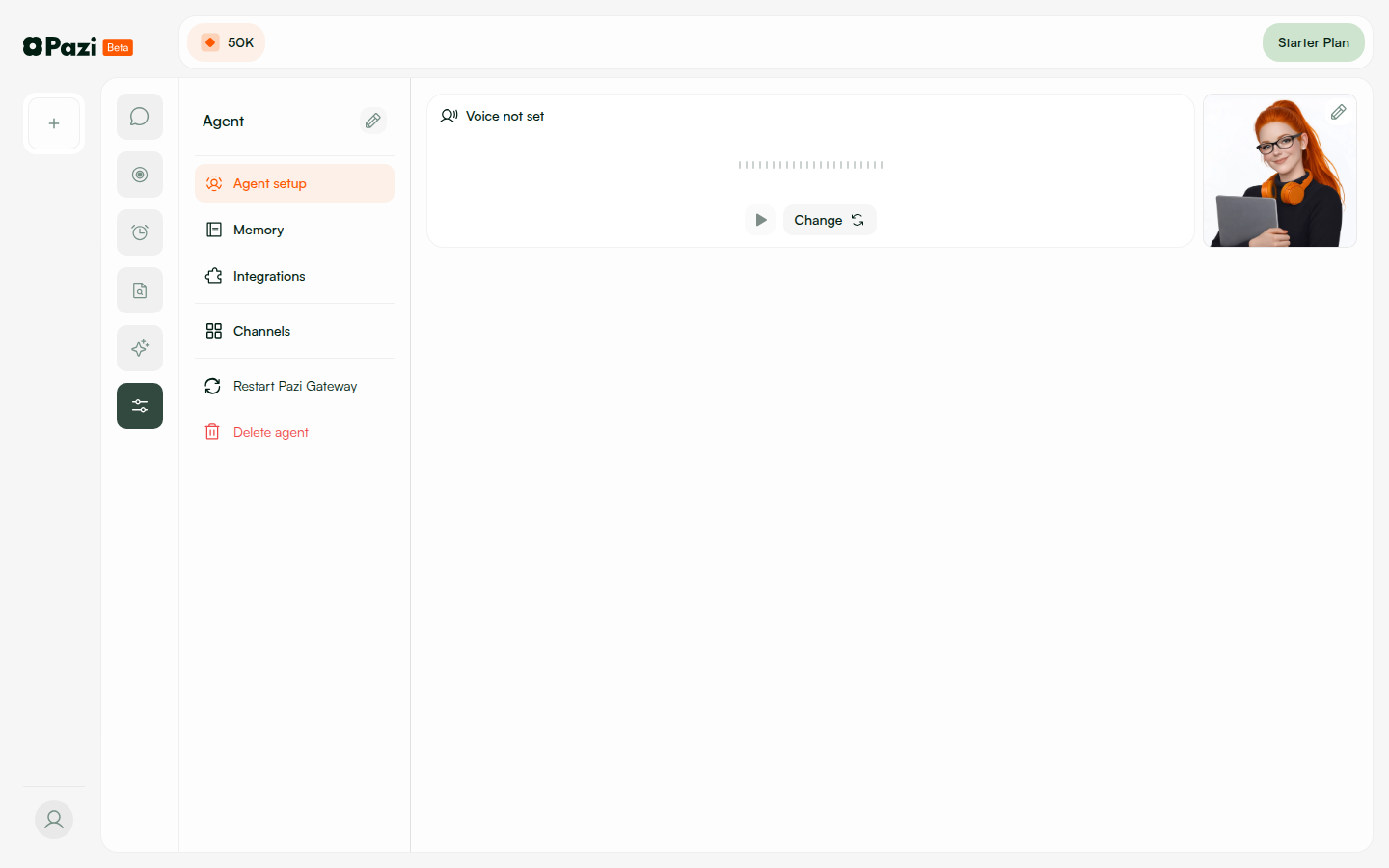
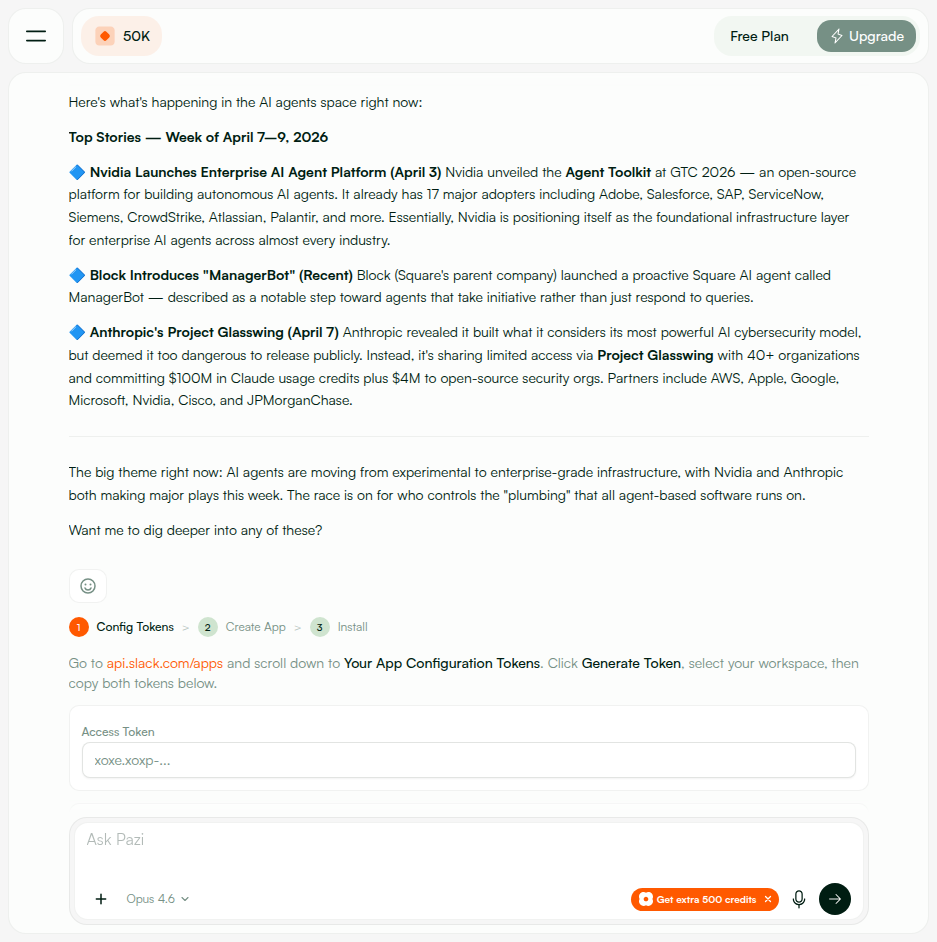
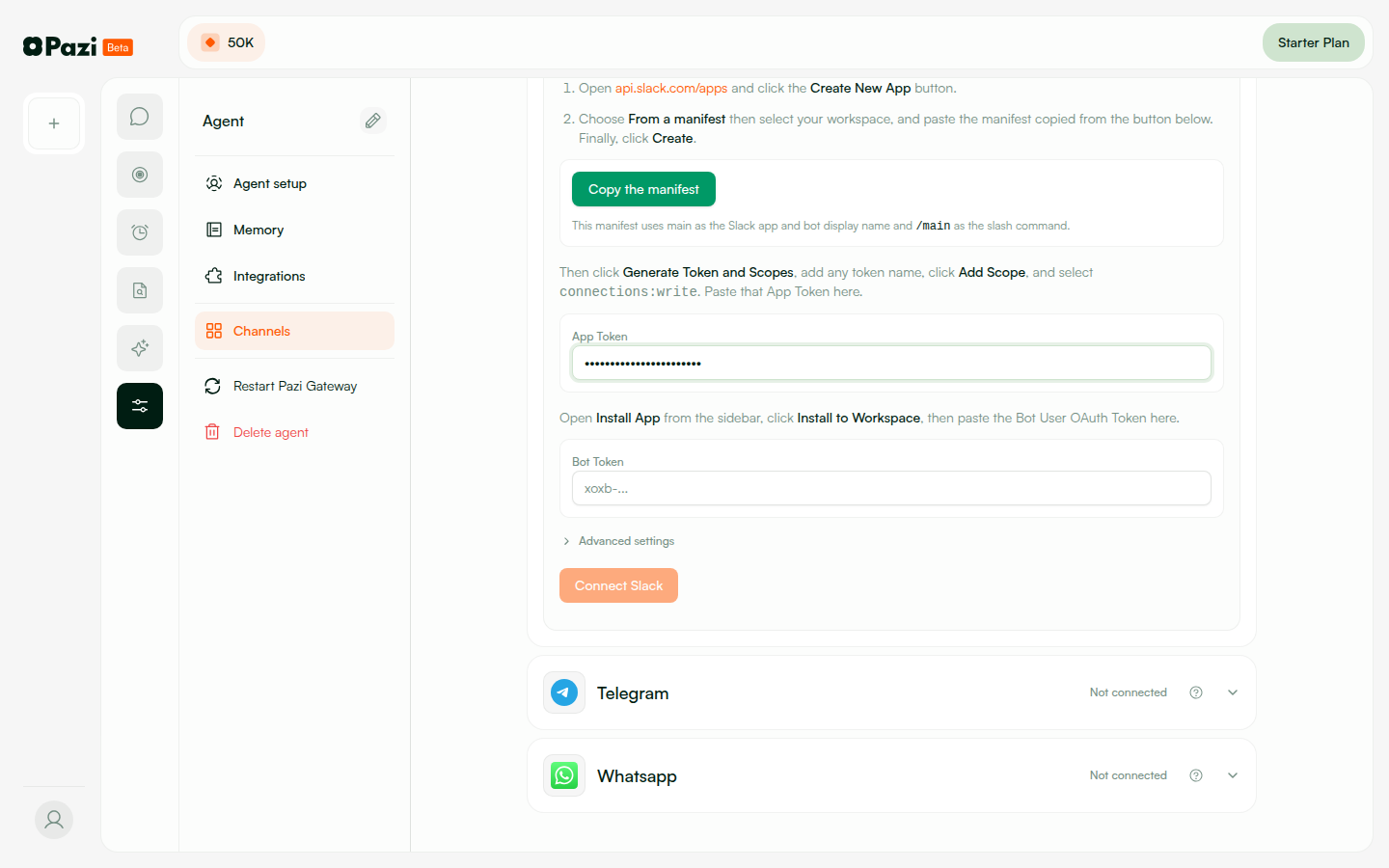
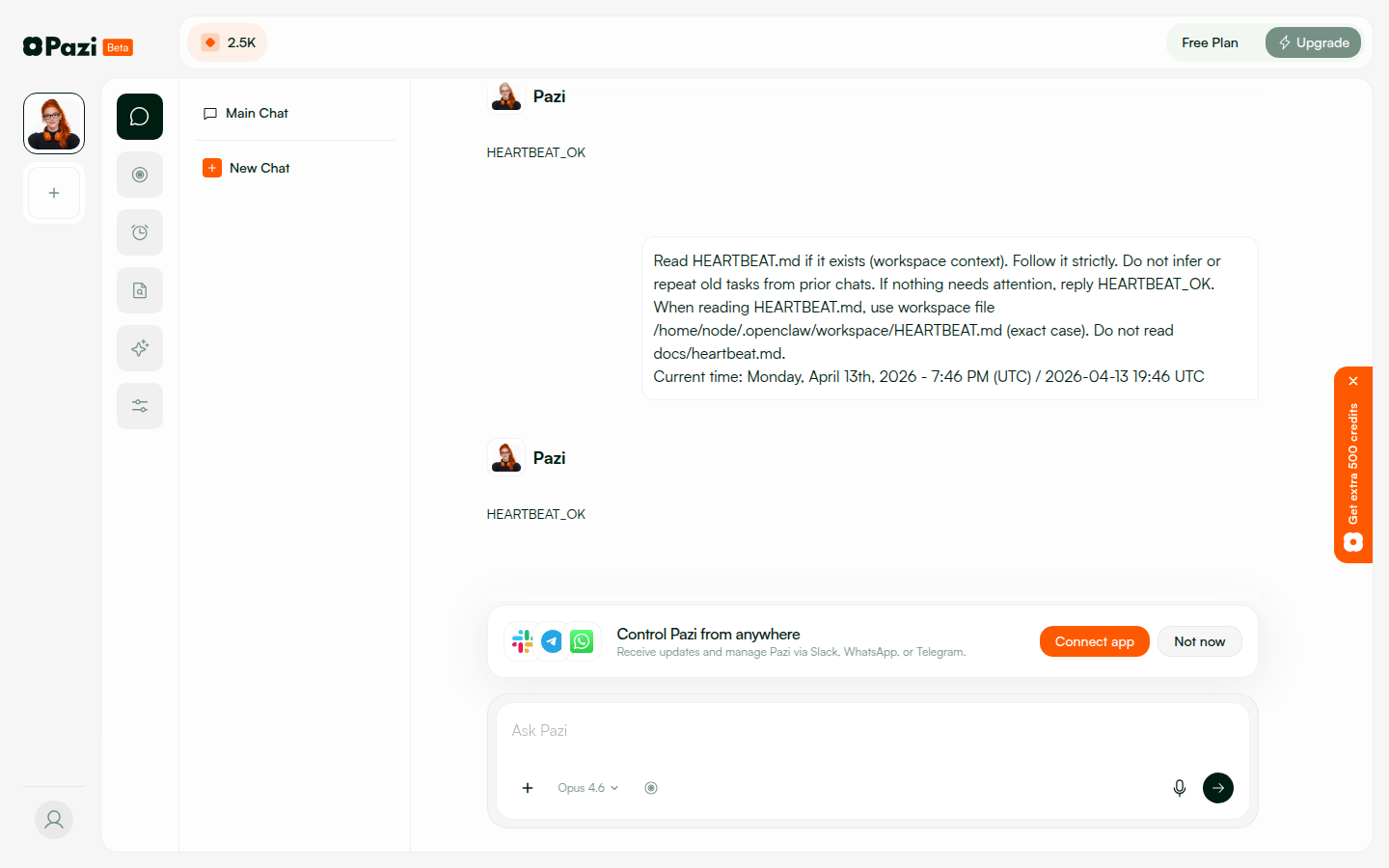
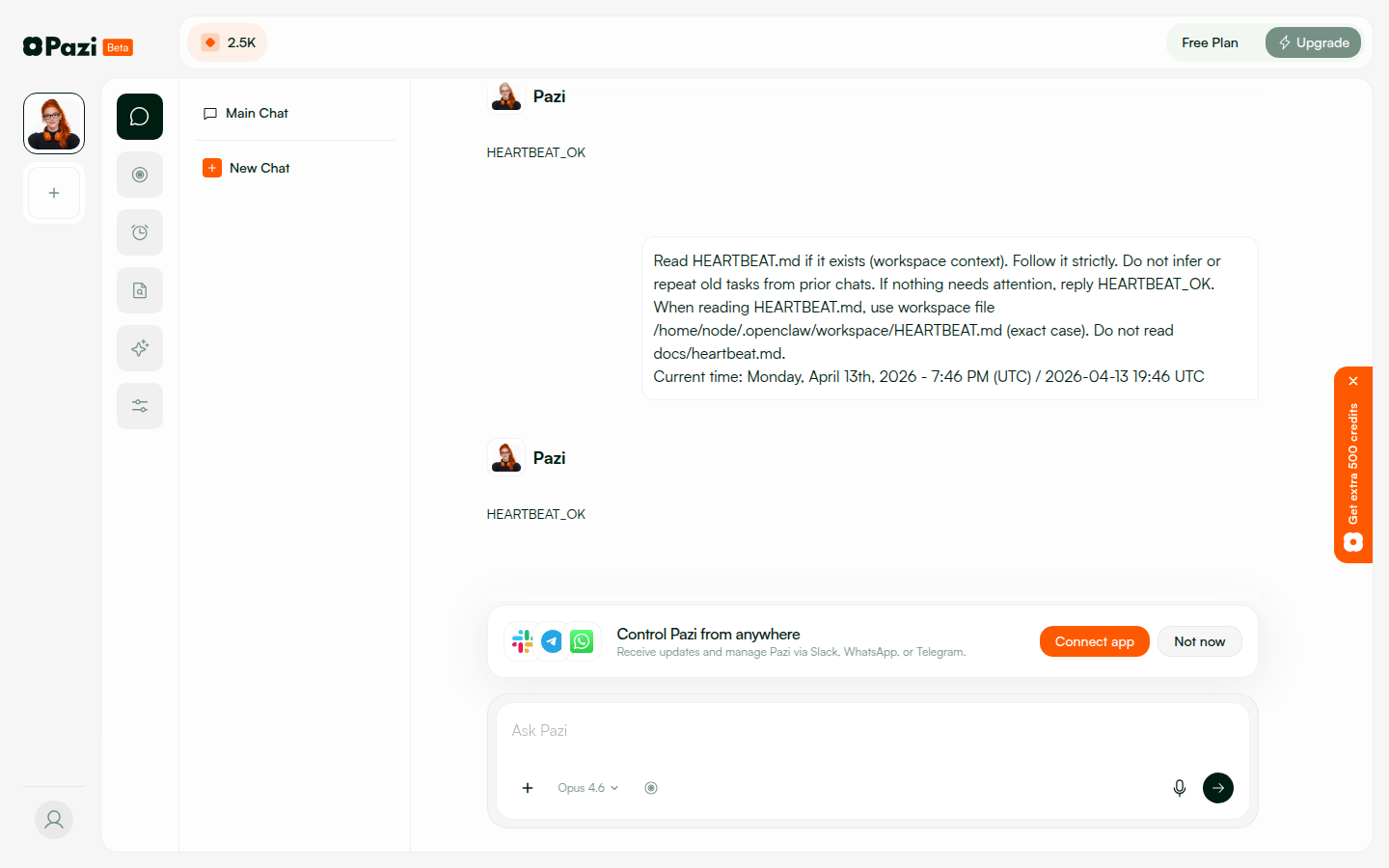
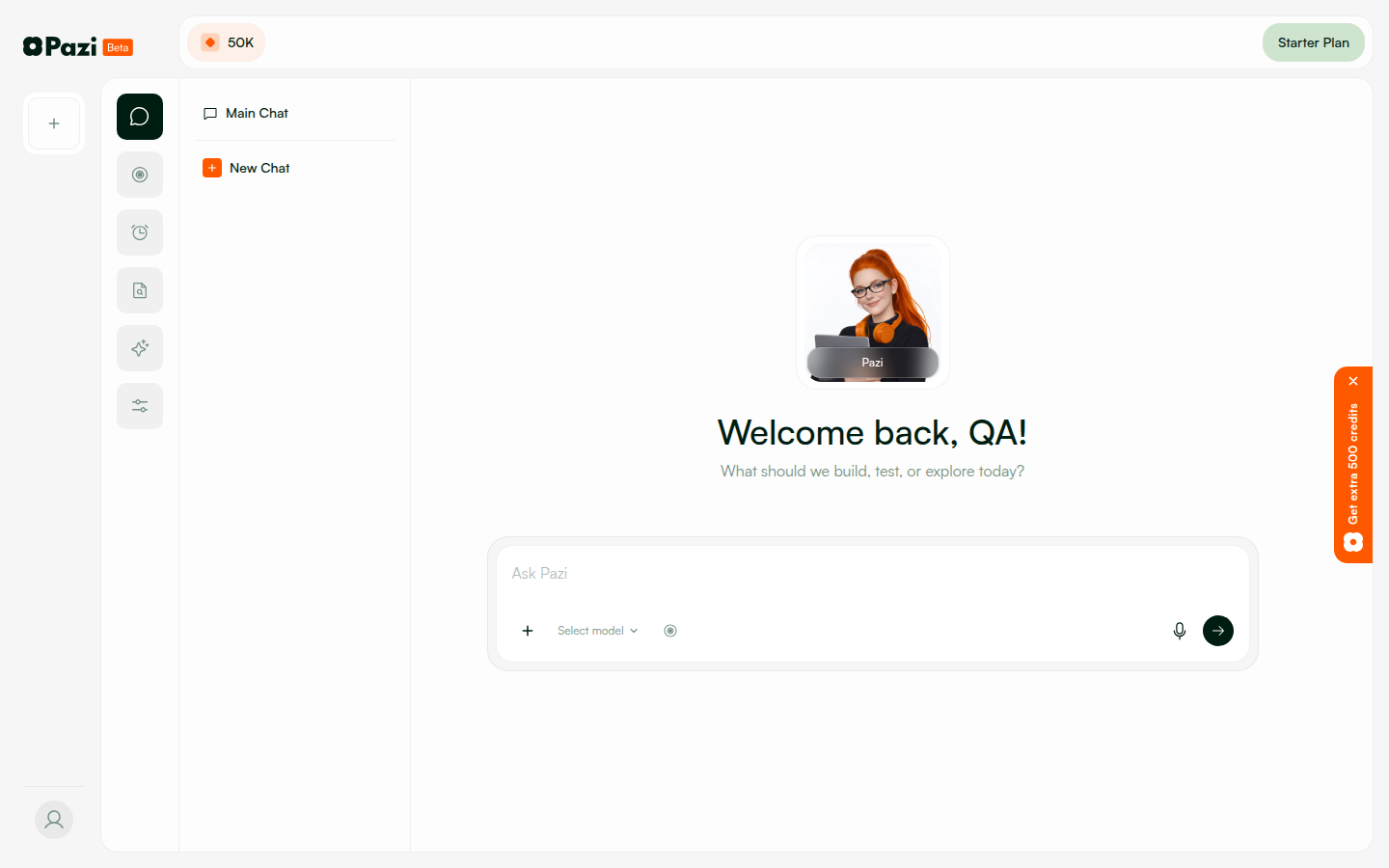
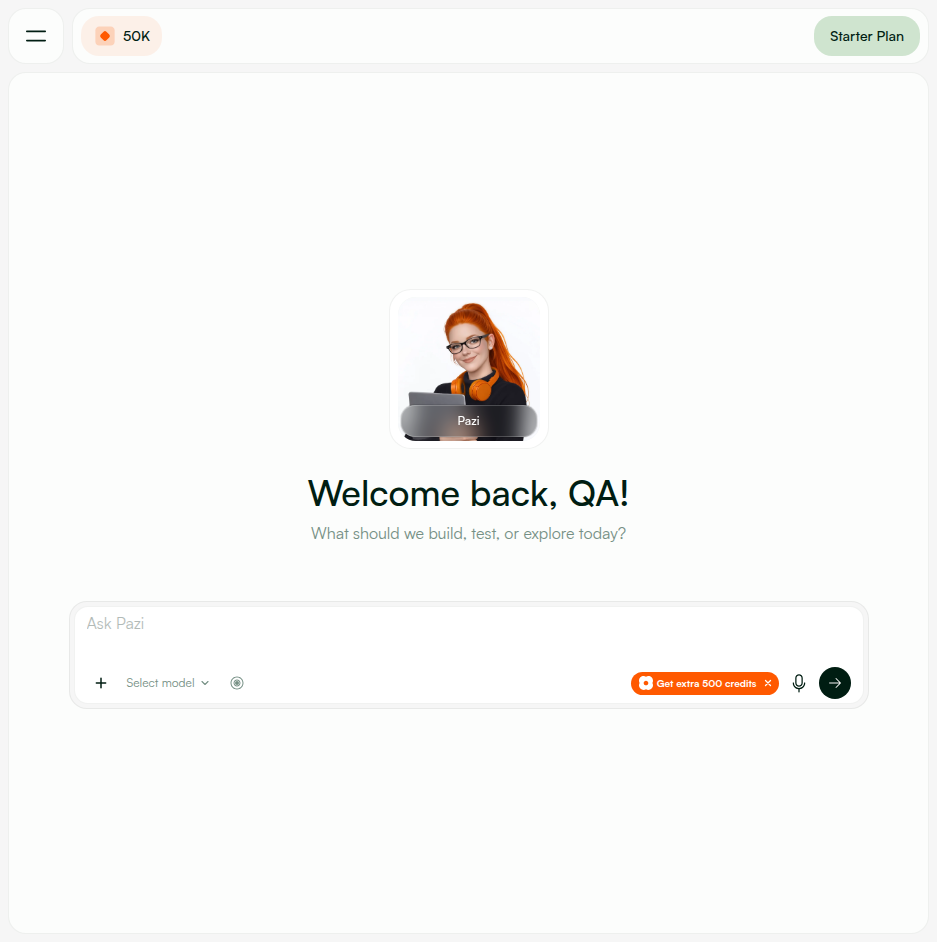
| API Image | qa-pazi/api:pr-533-v11 — Up 8+ hours (healthy) |
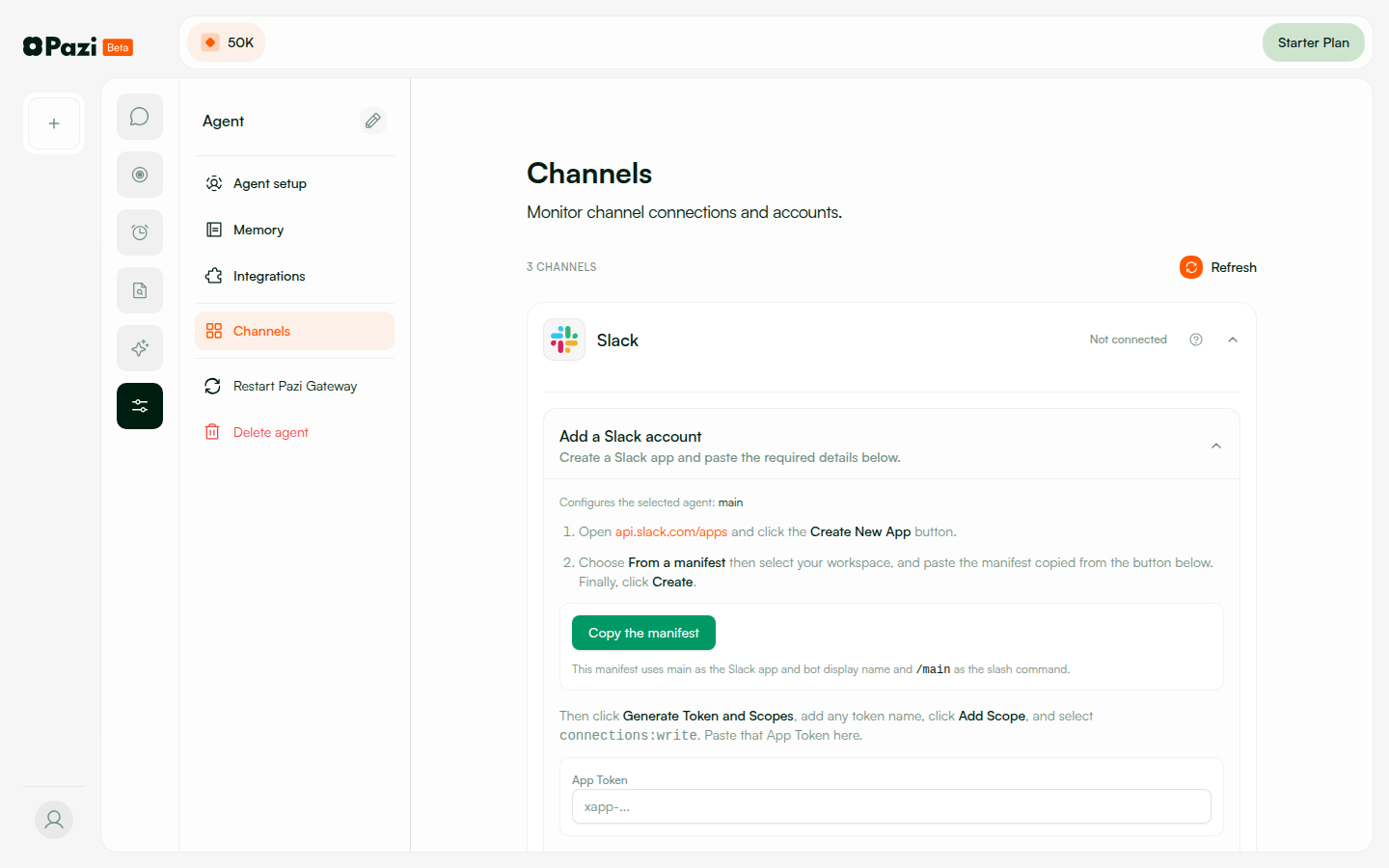
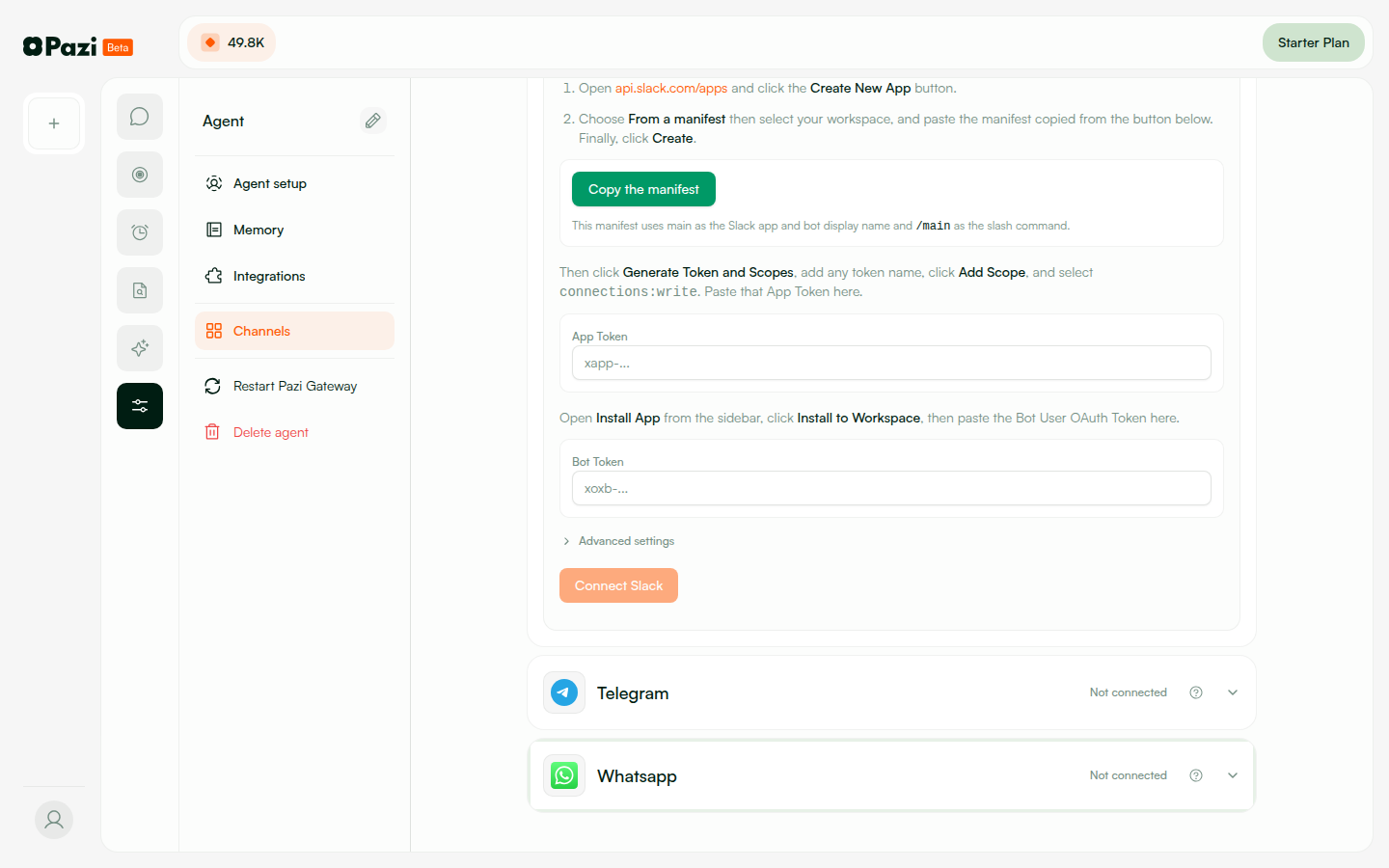
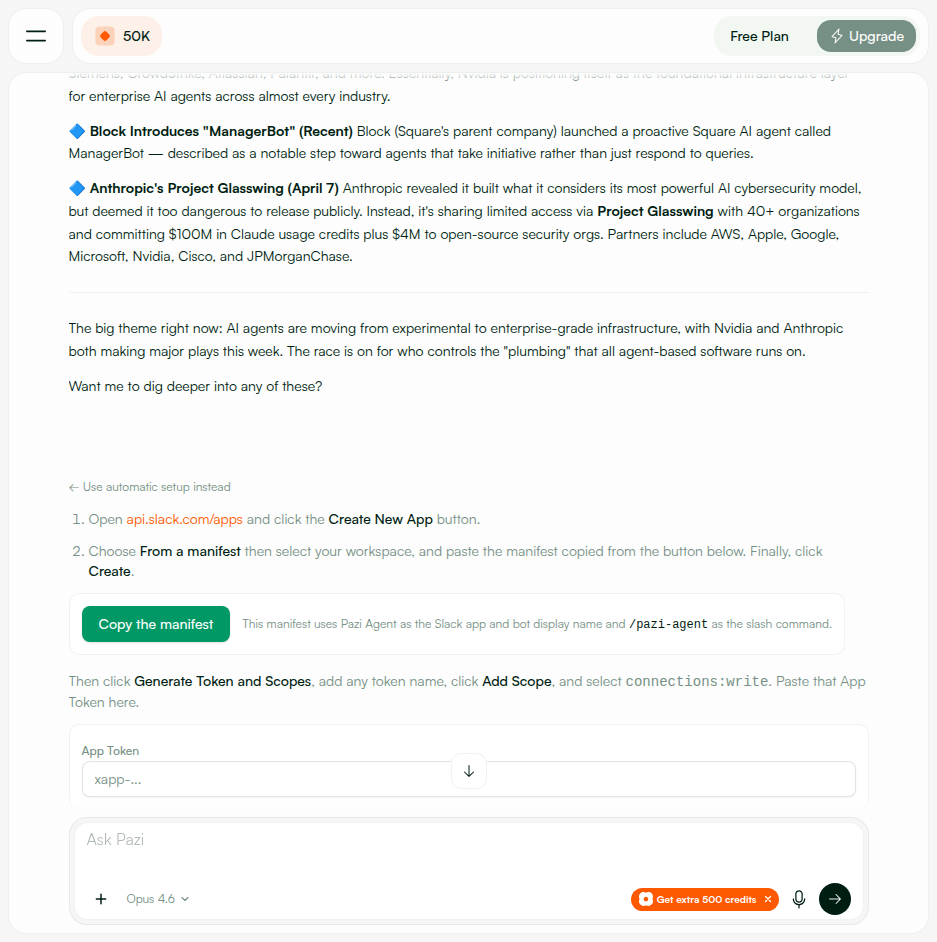
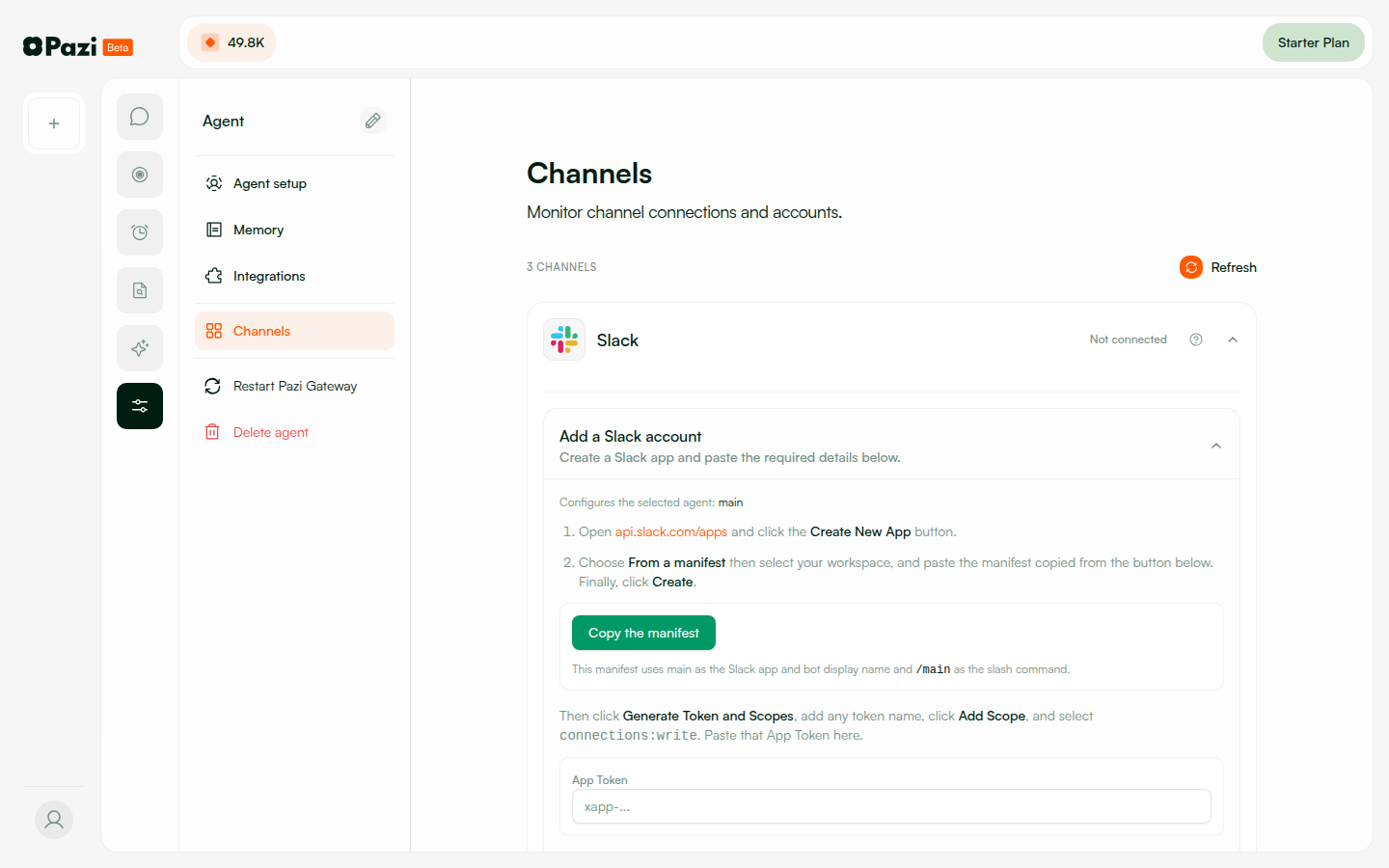
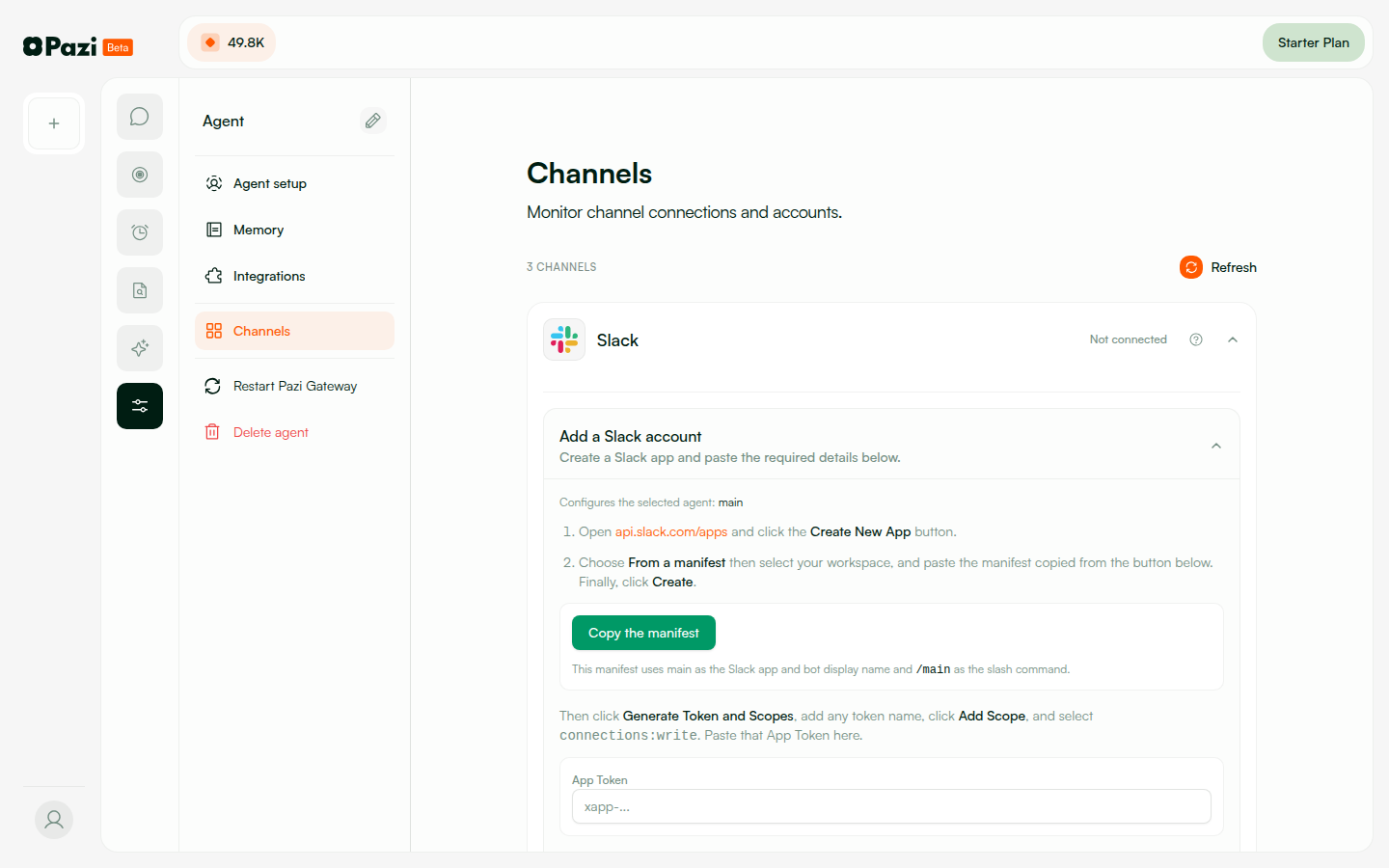
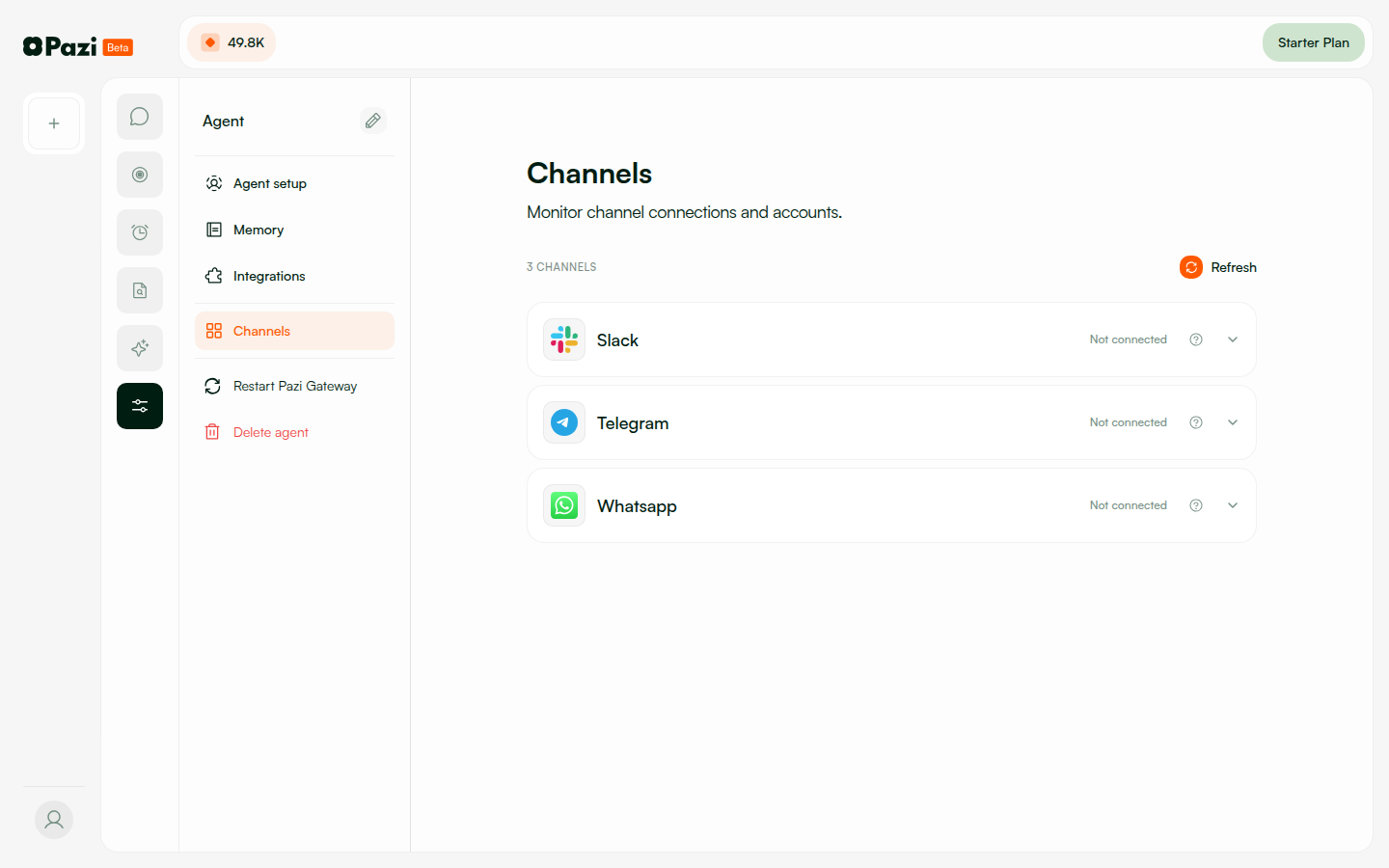
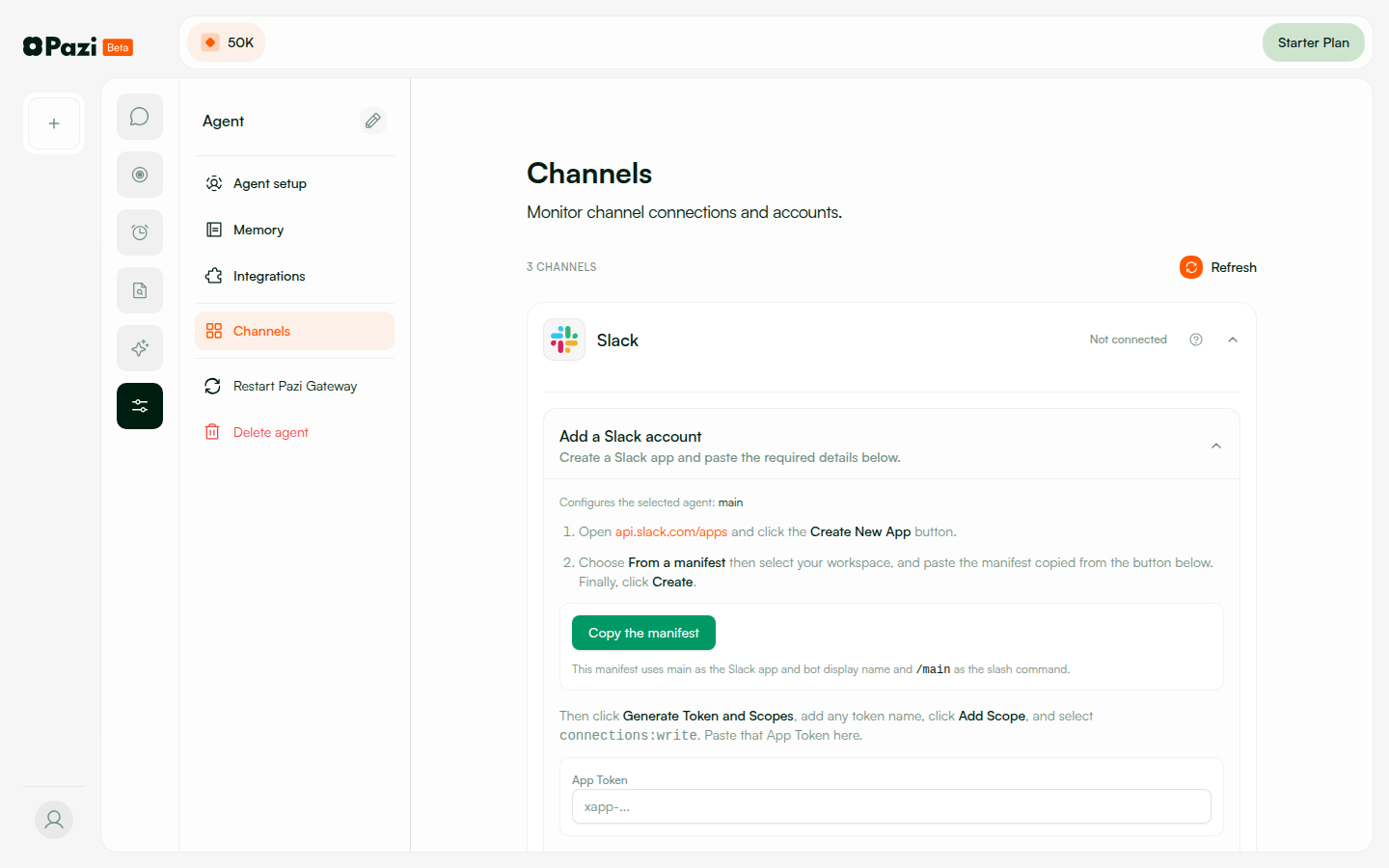
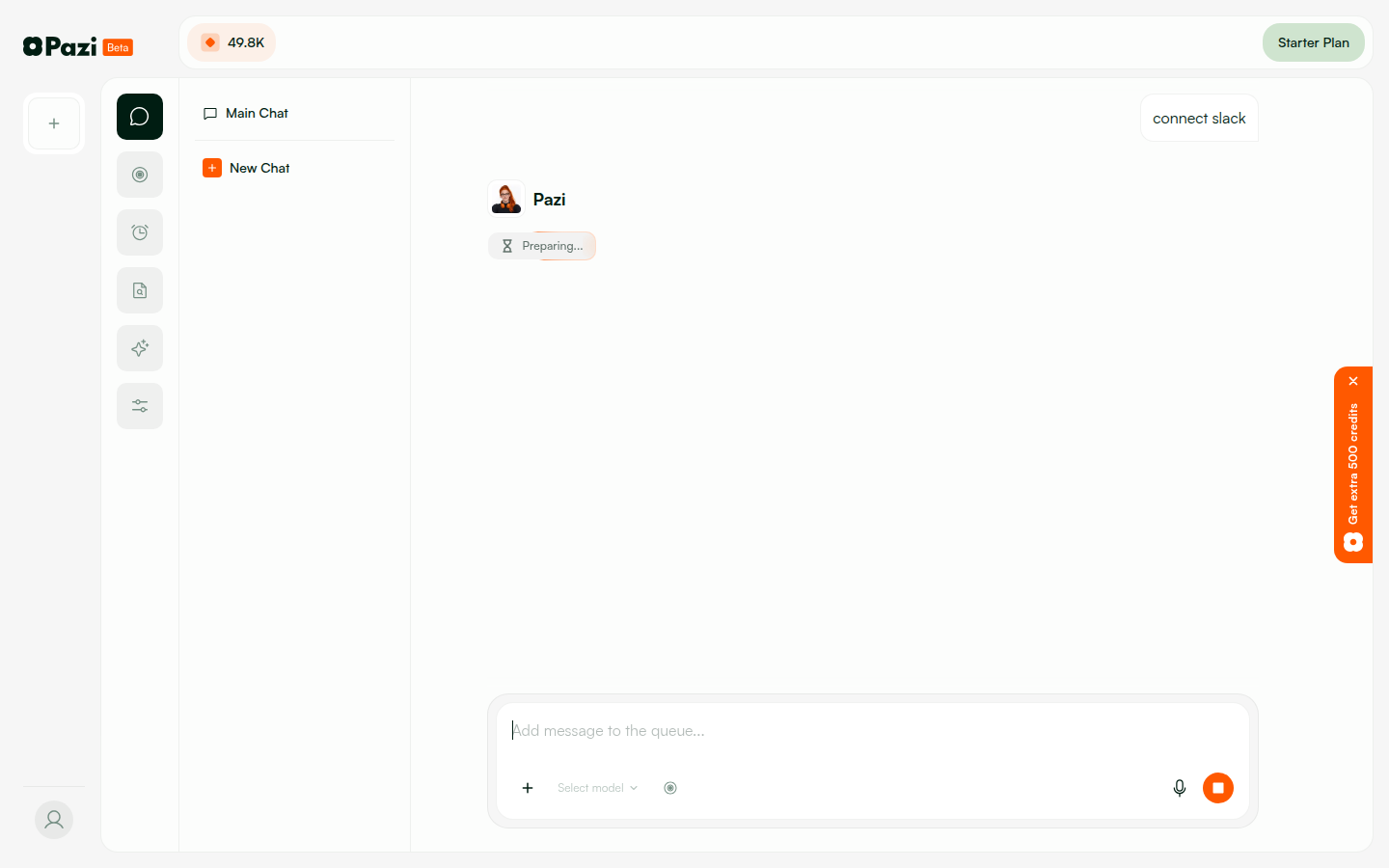
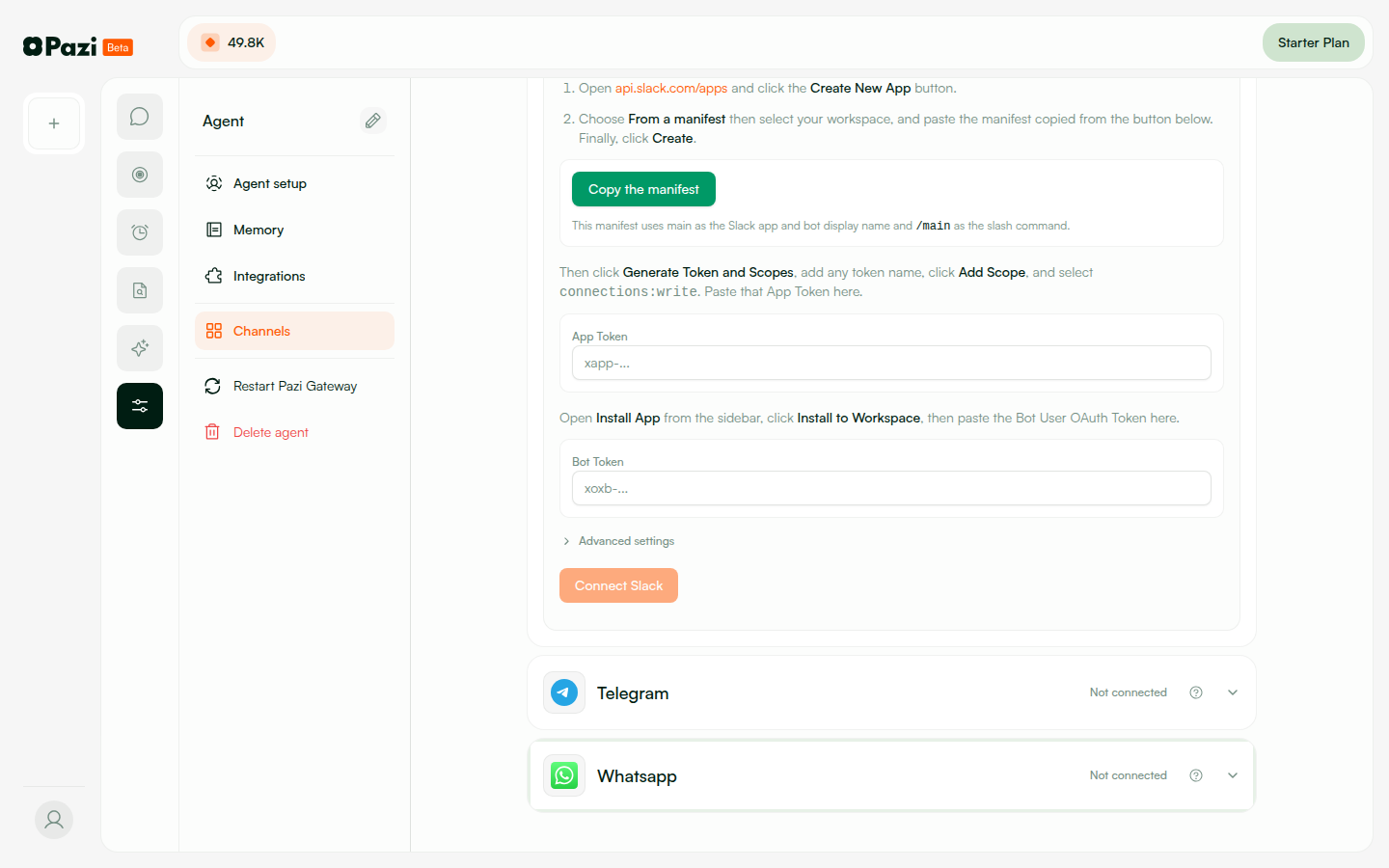
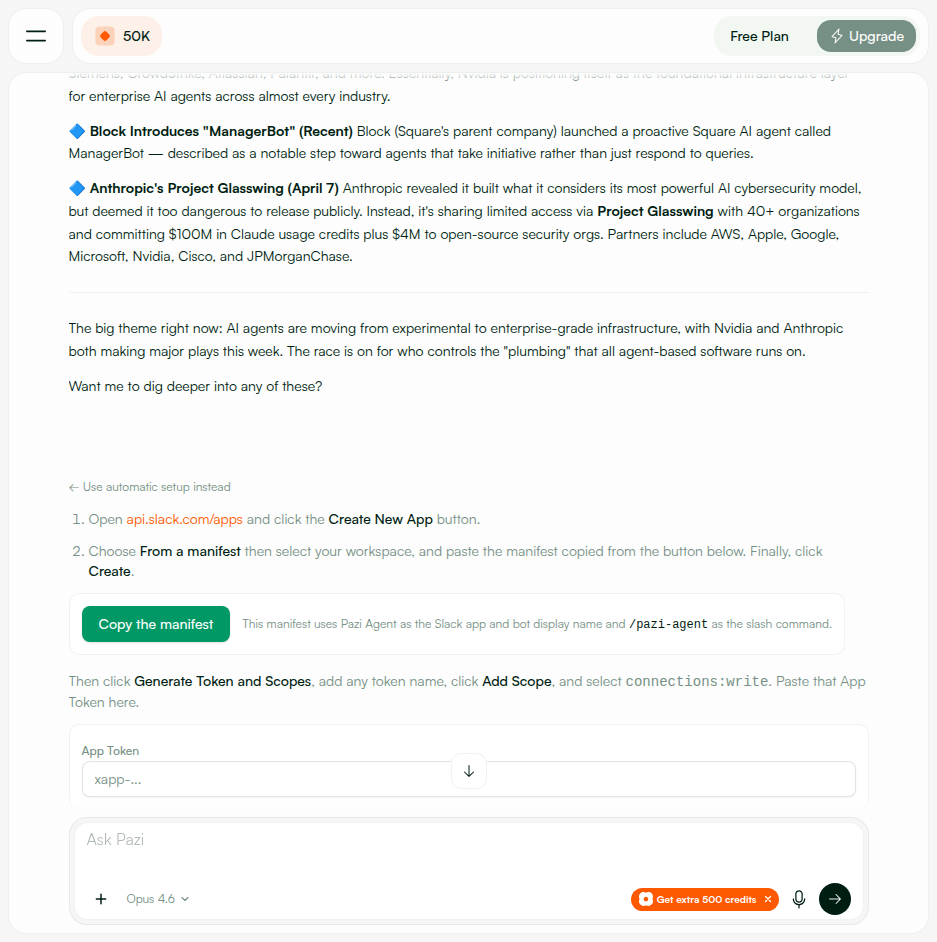
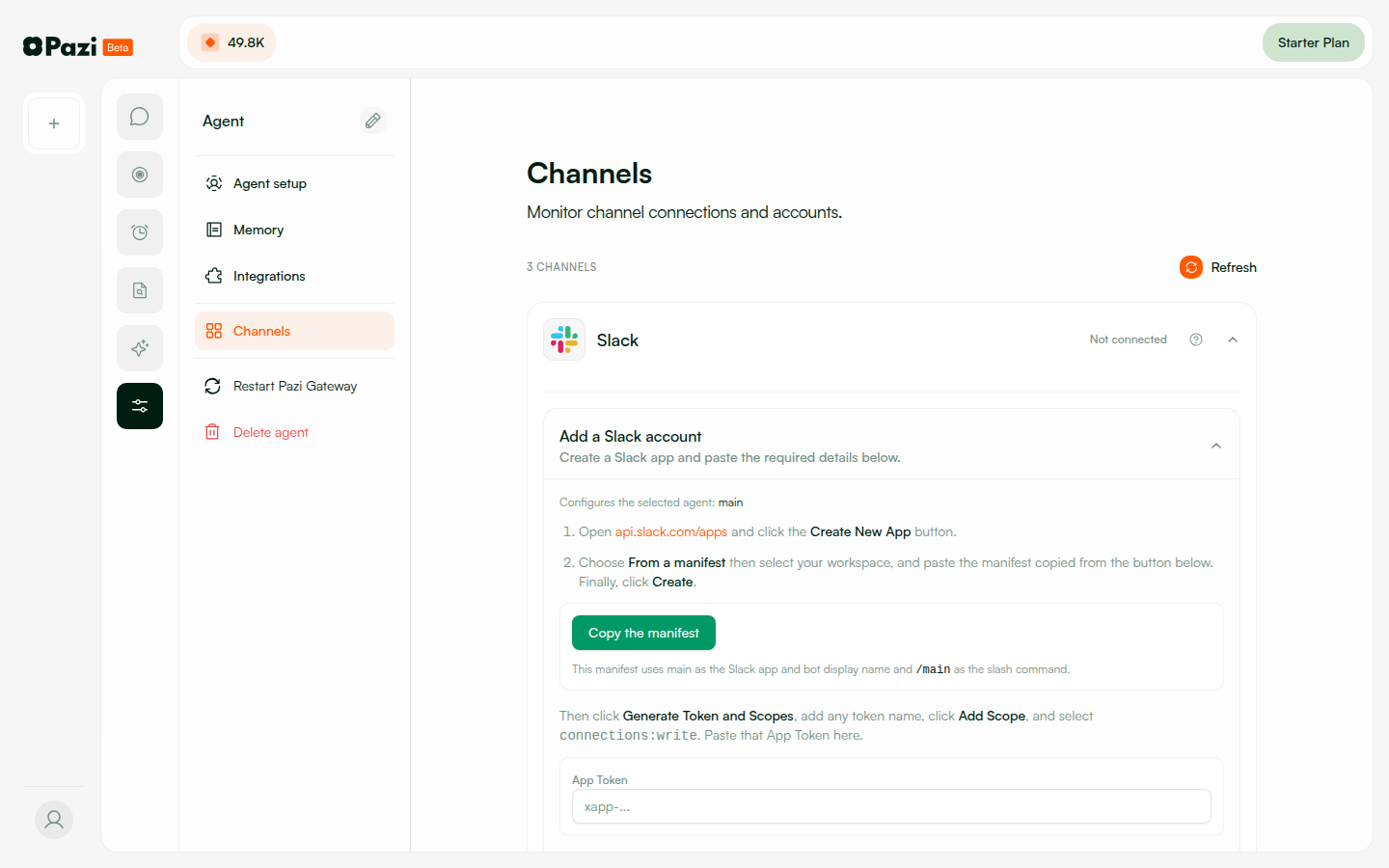
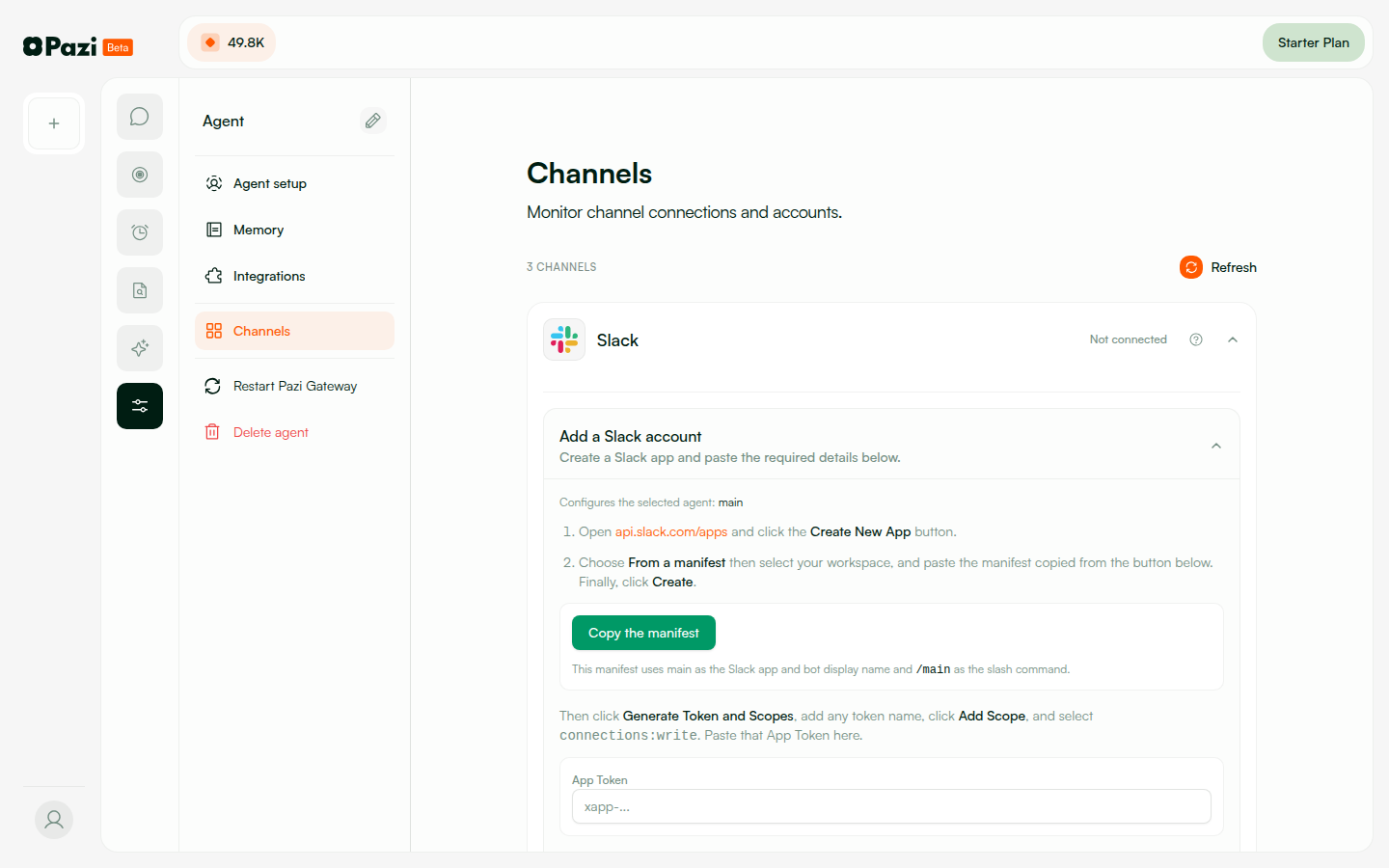
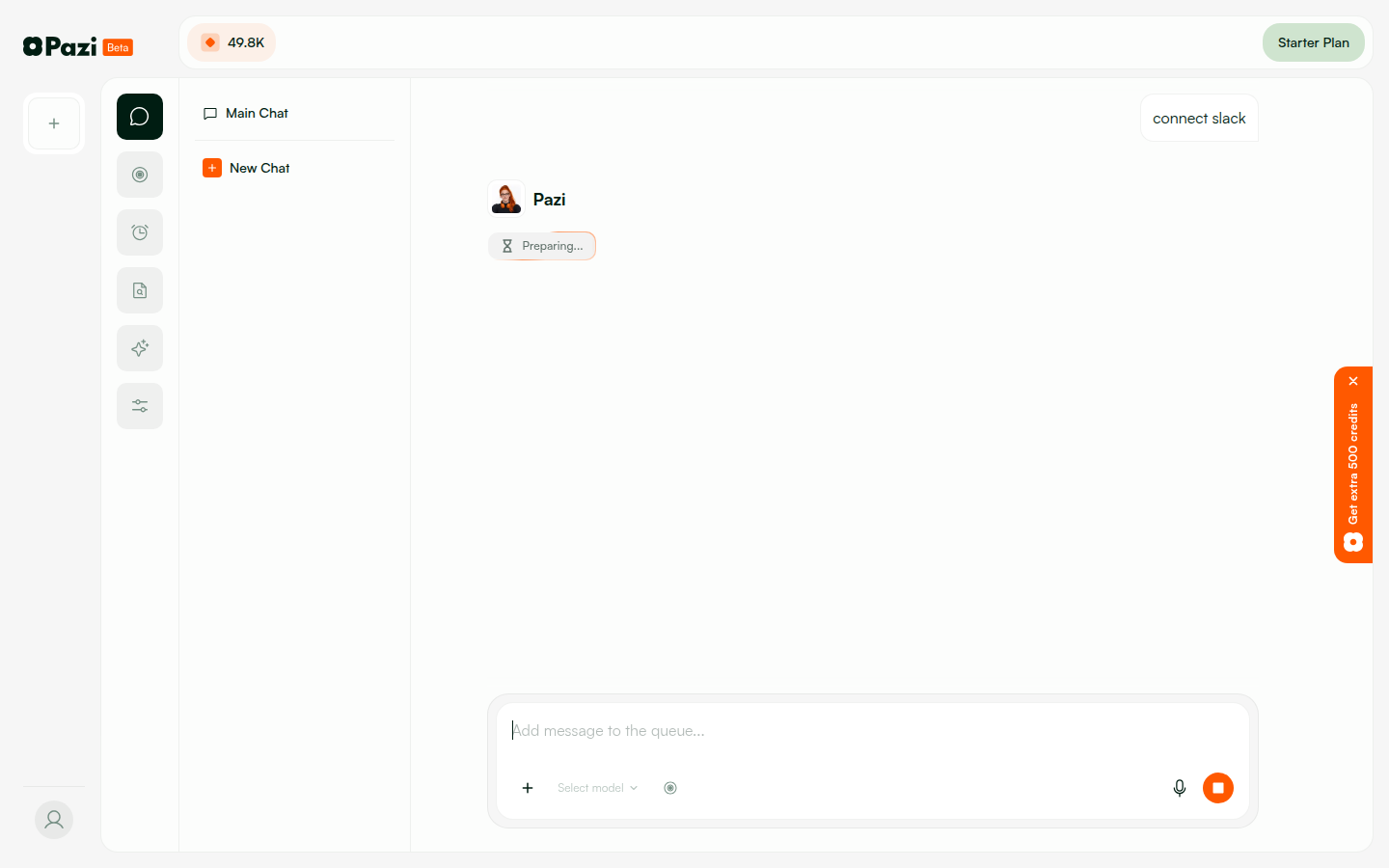
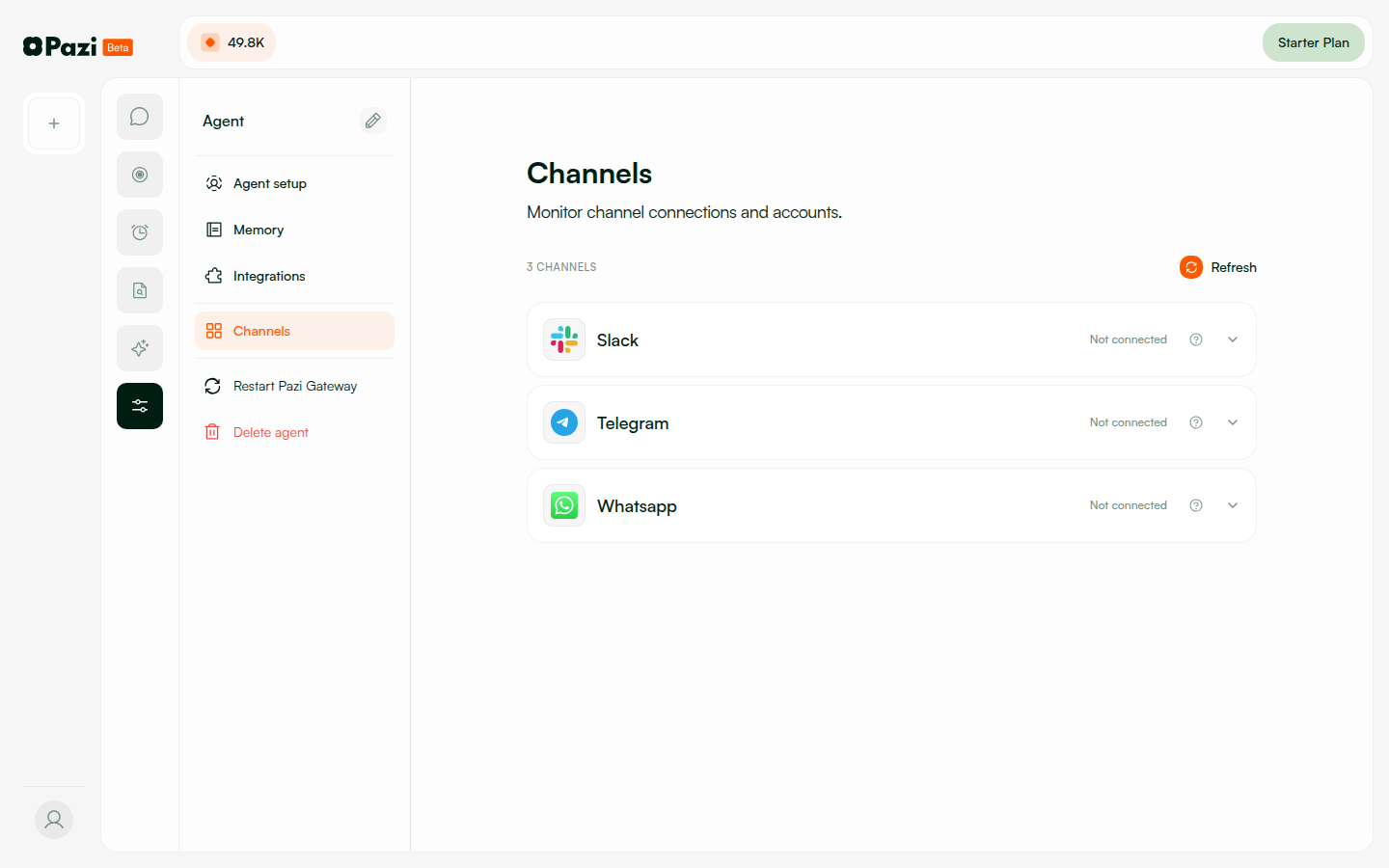
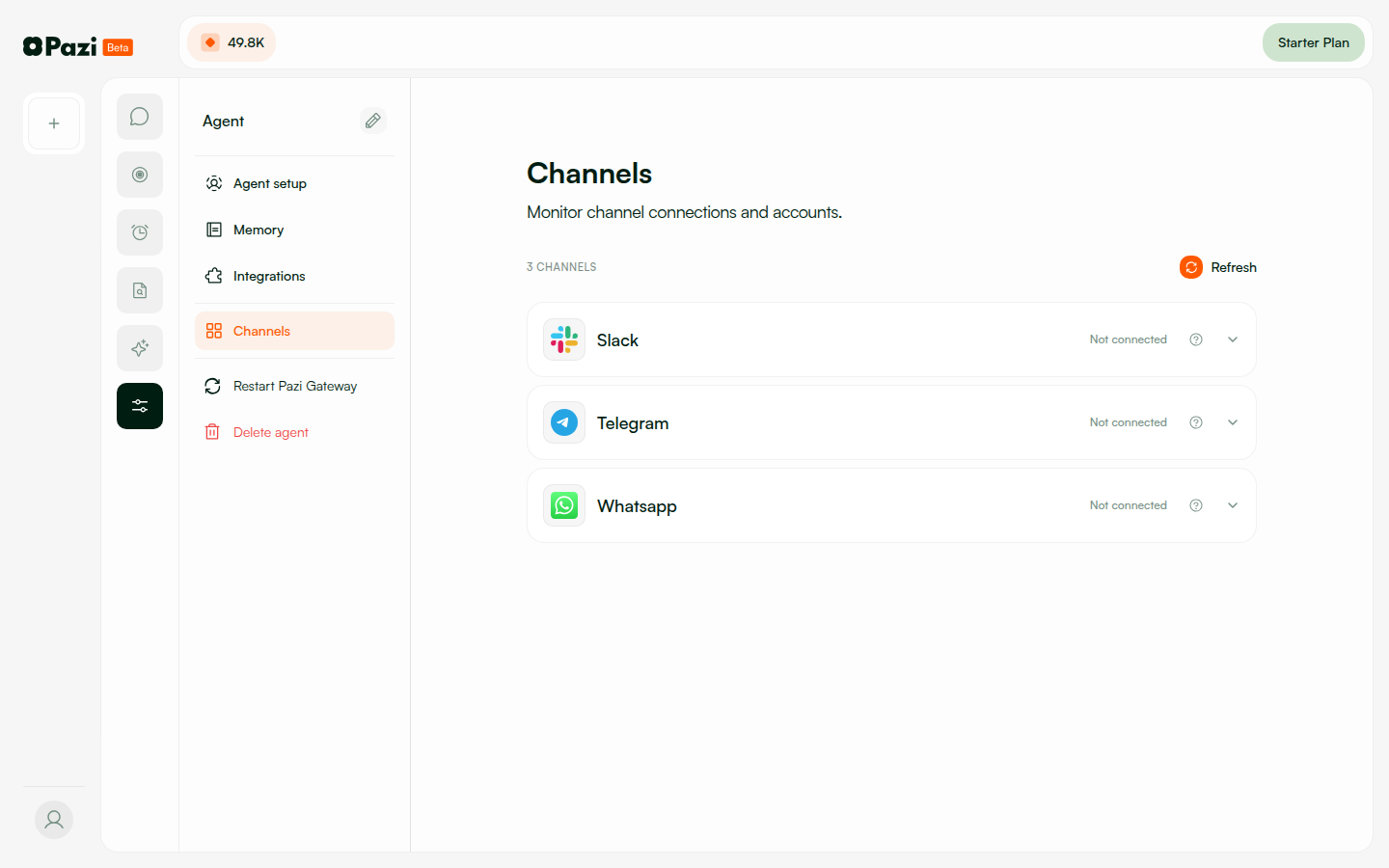
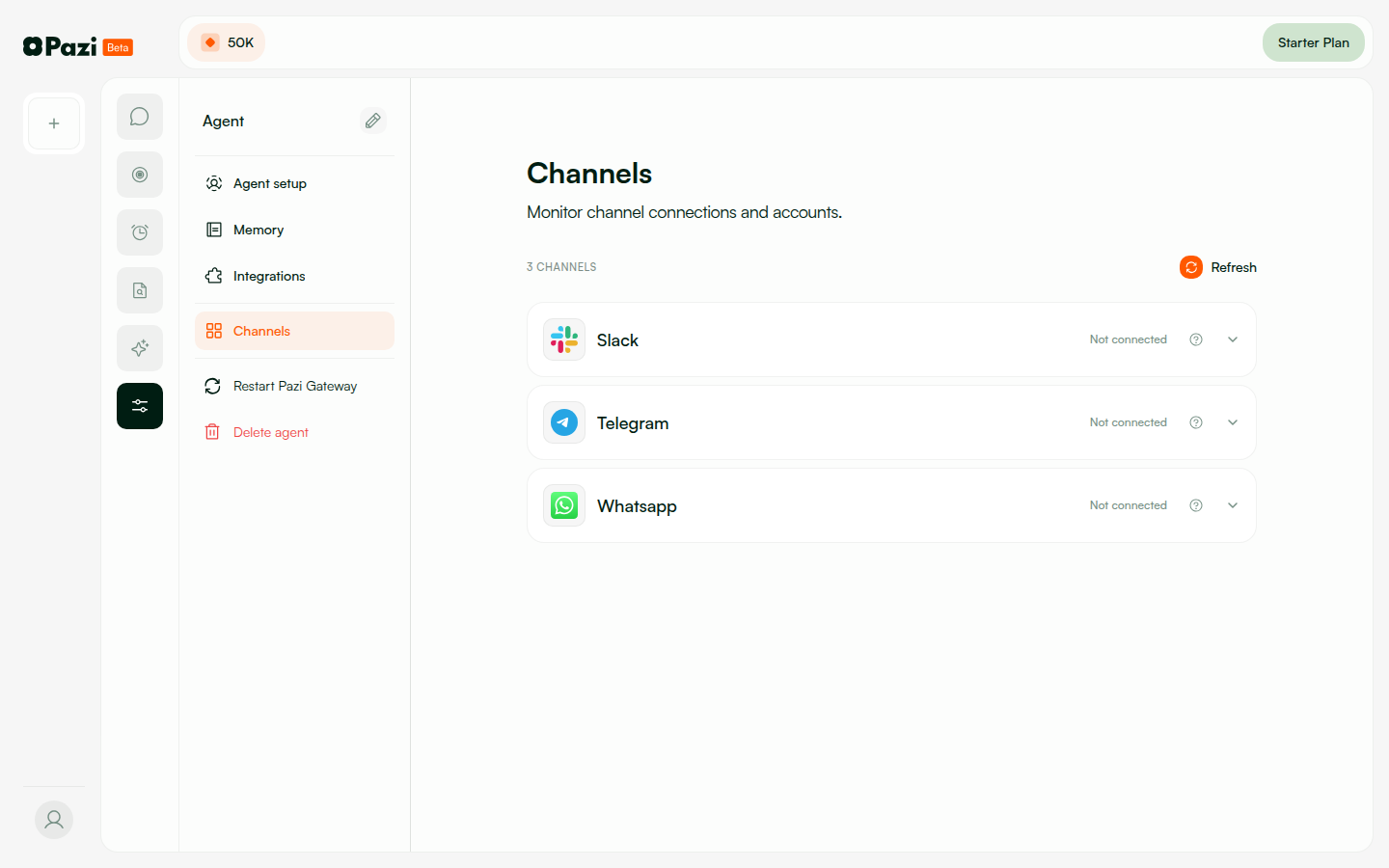
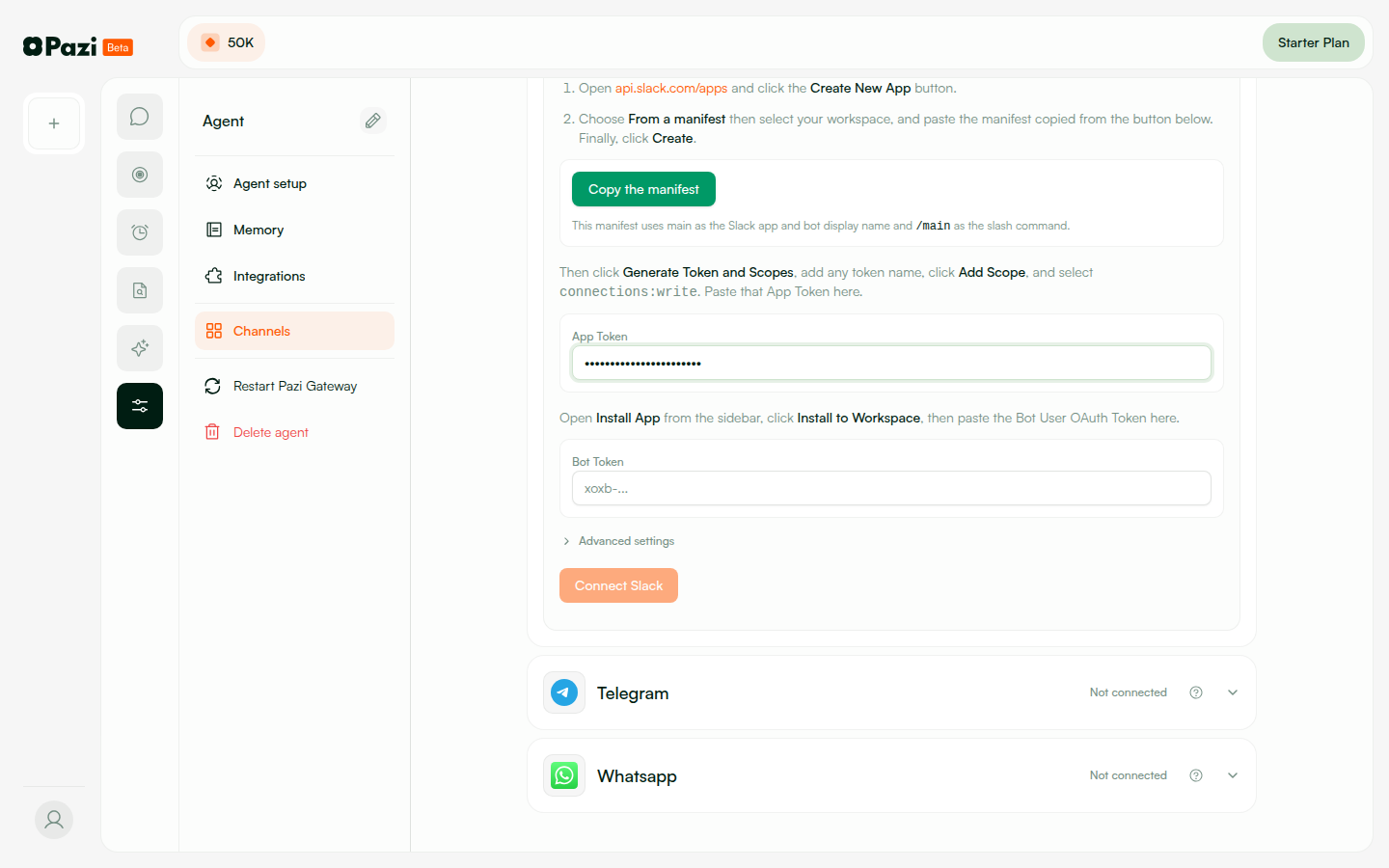
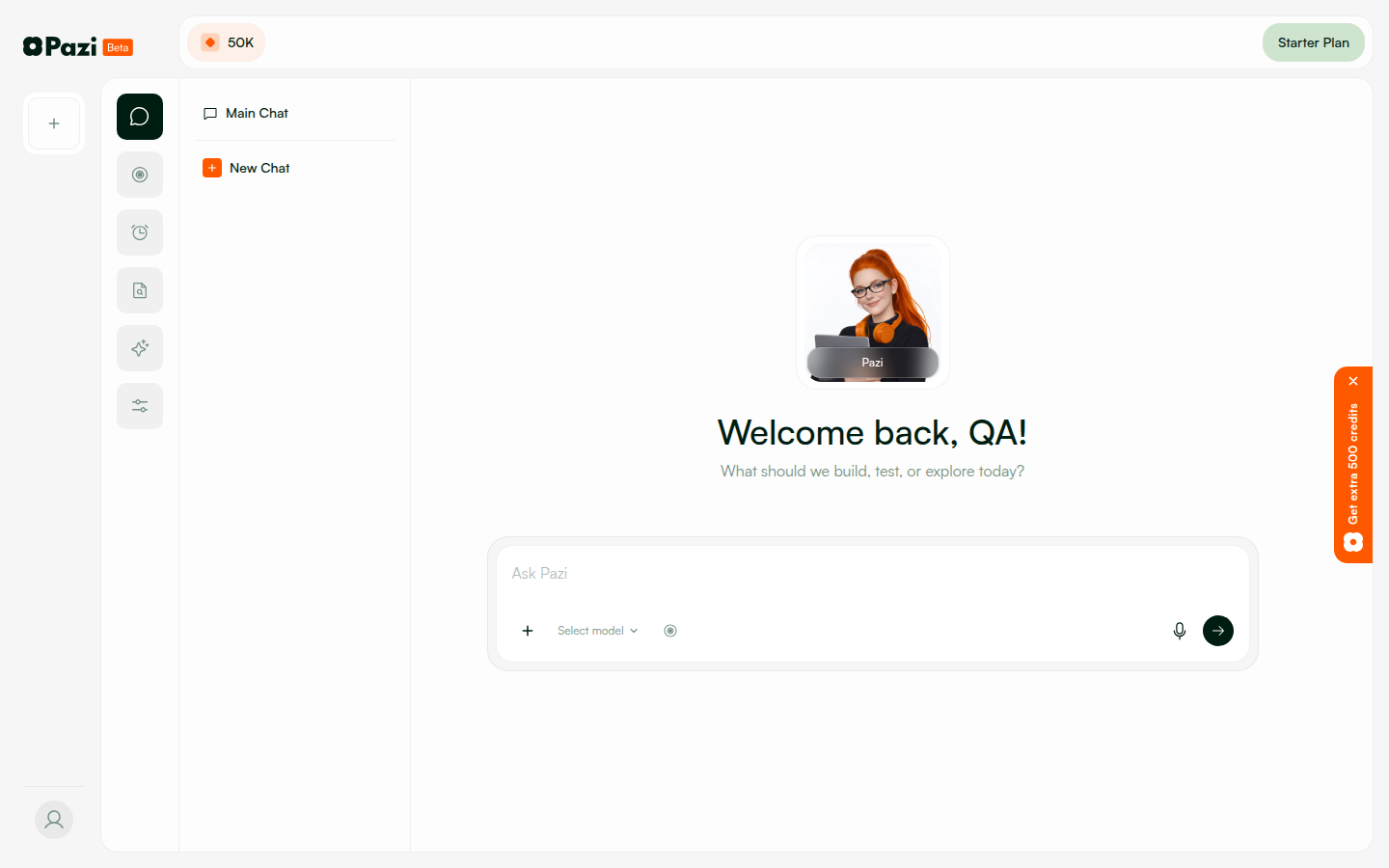
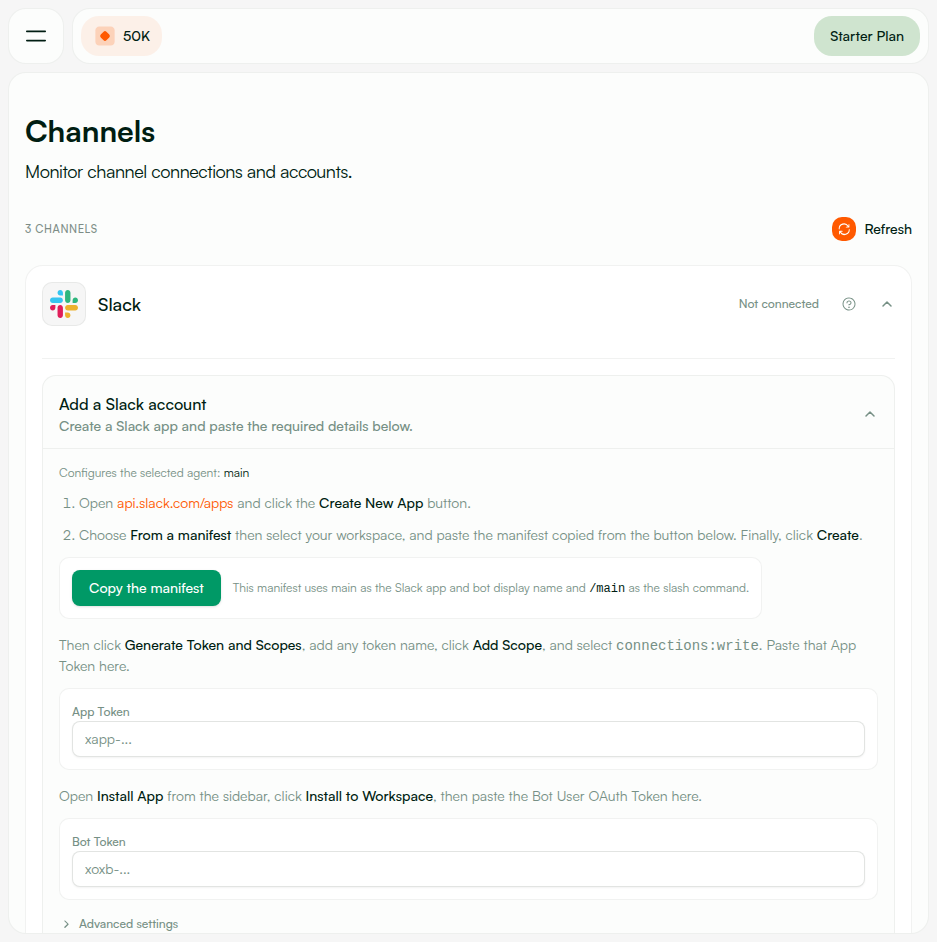
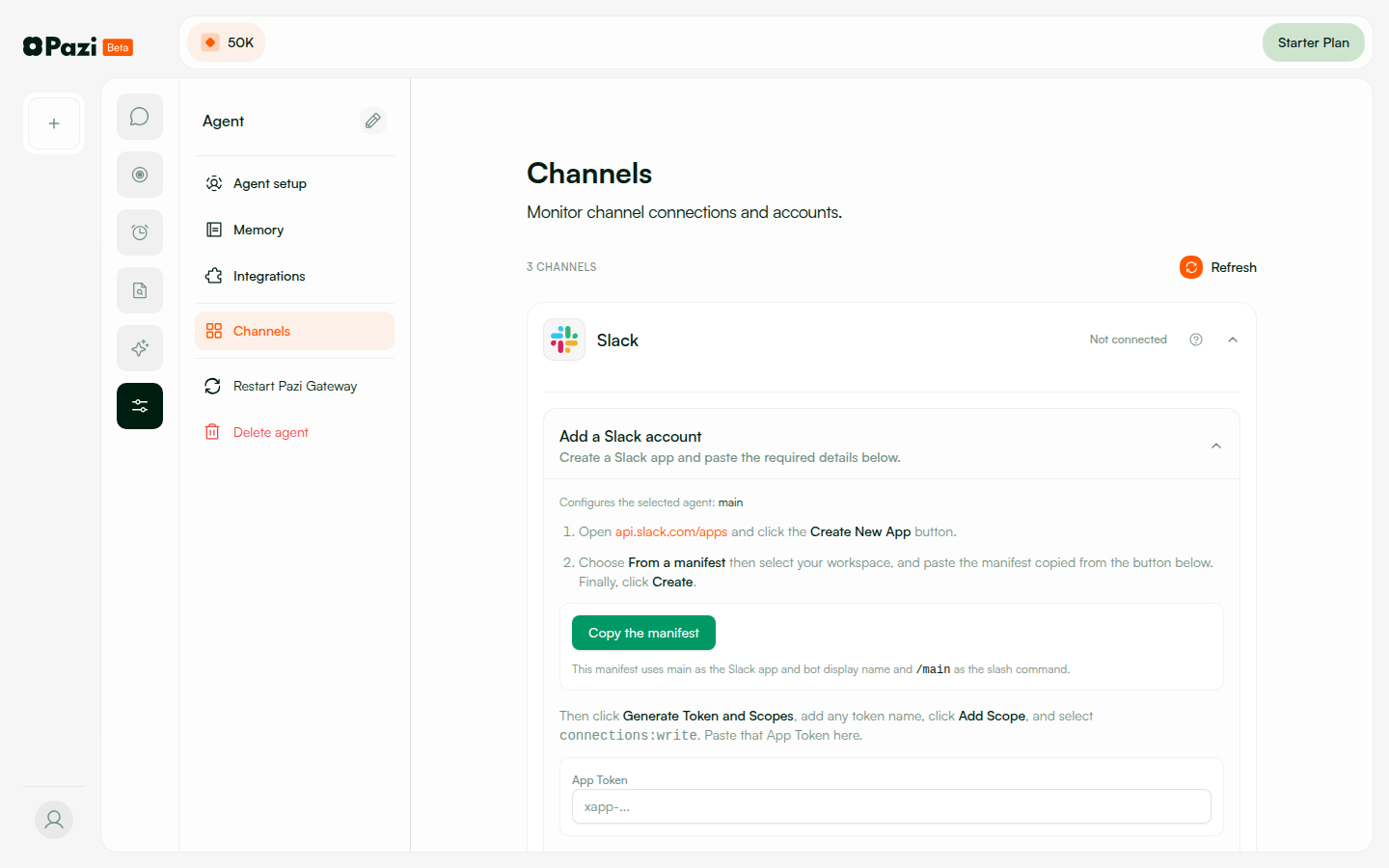
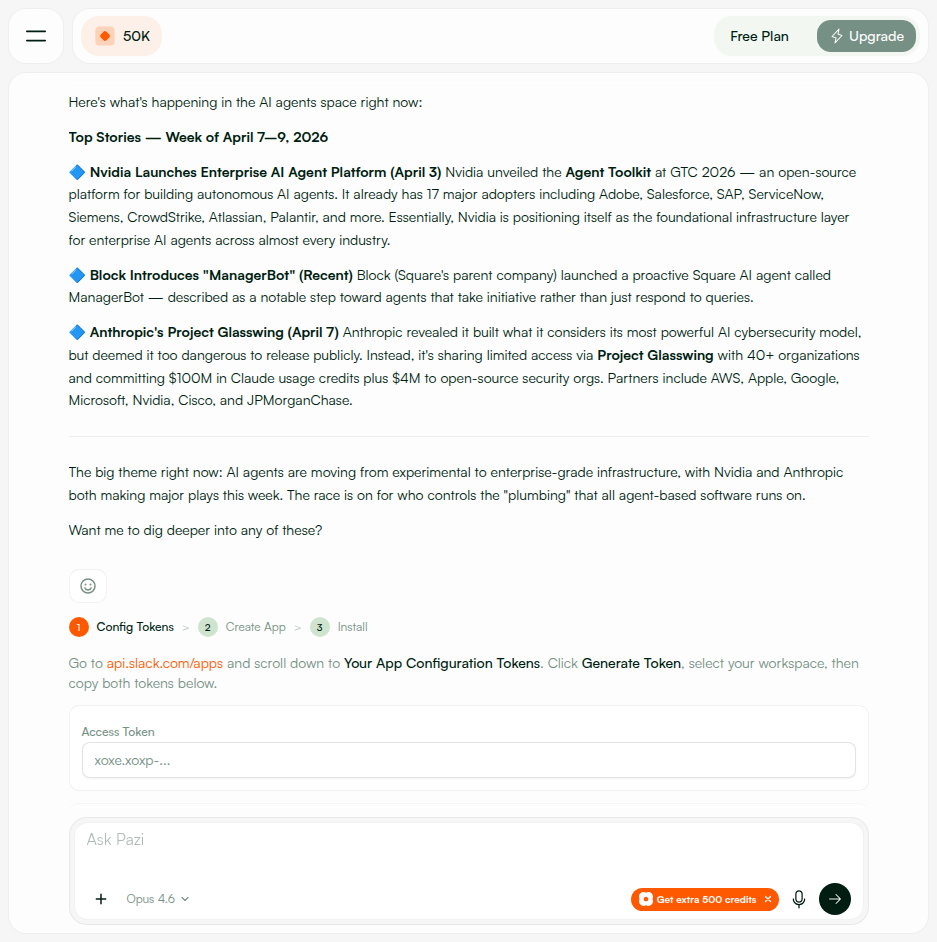
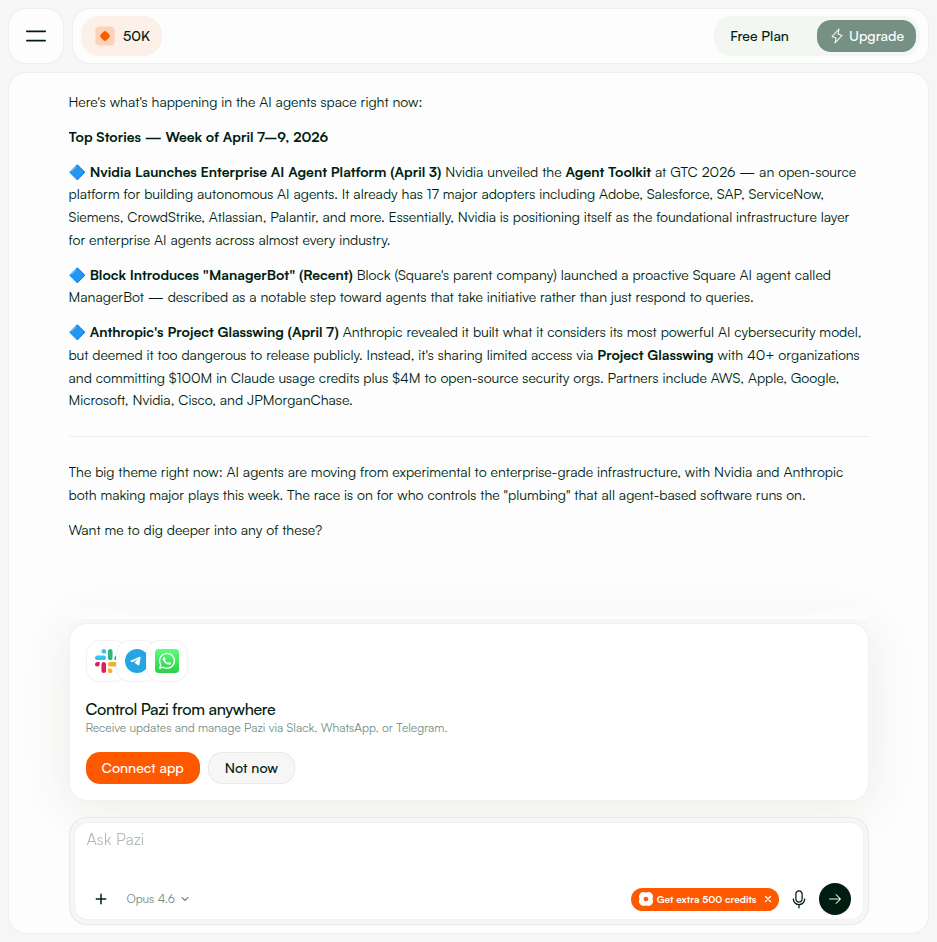
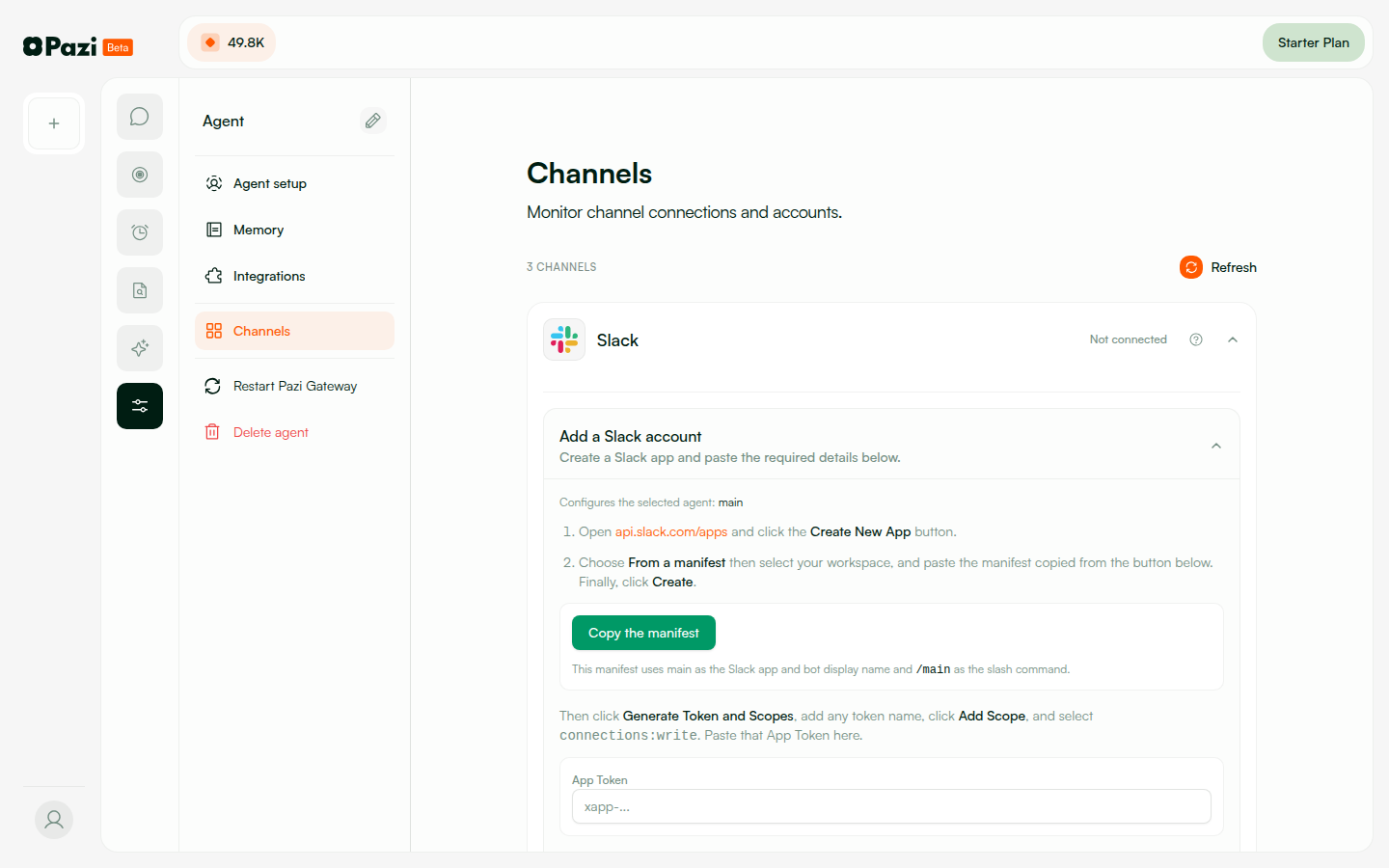
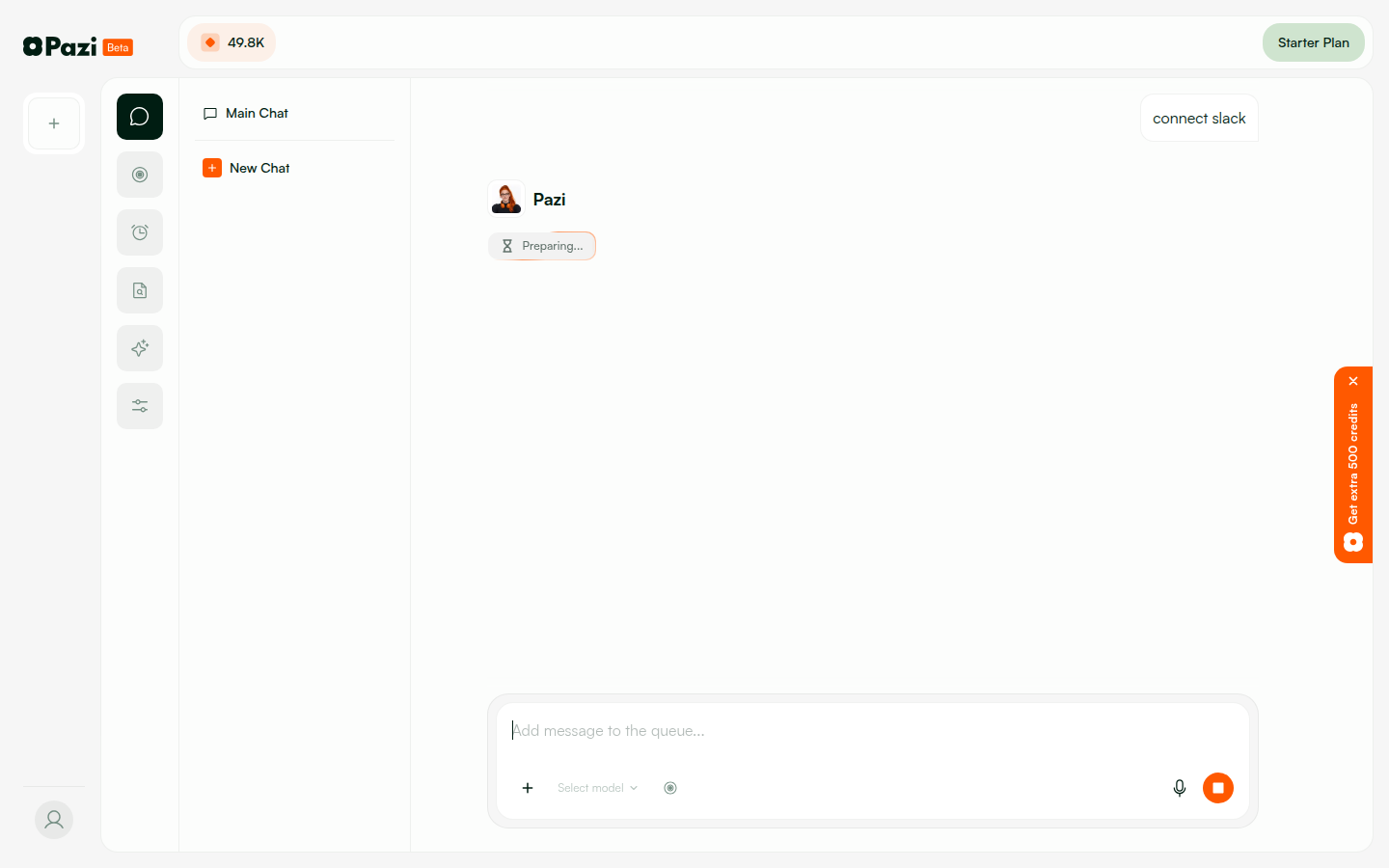
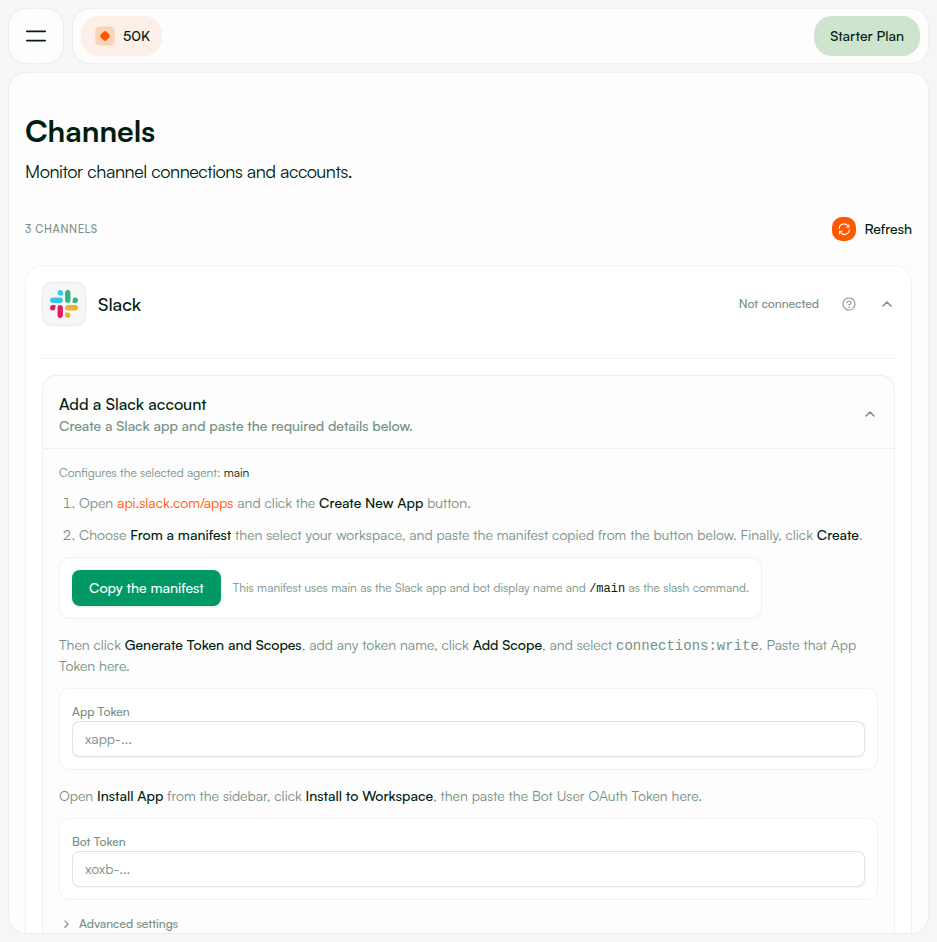
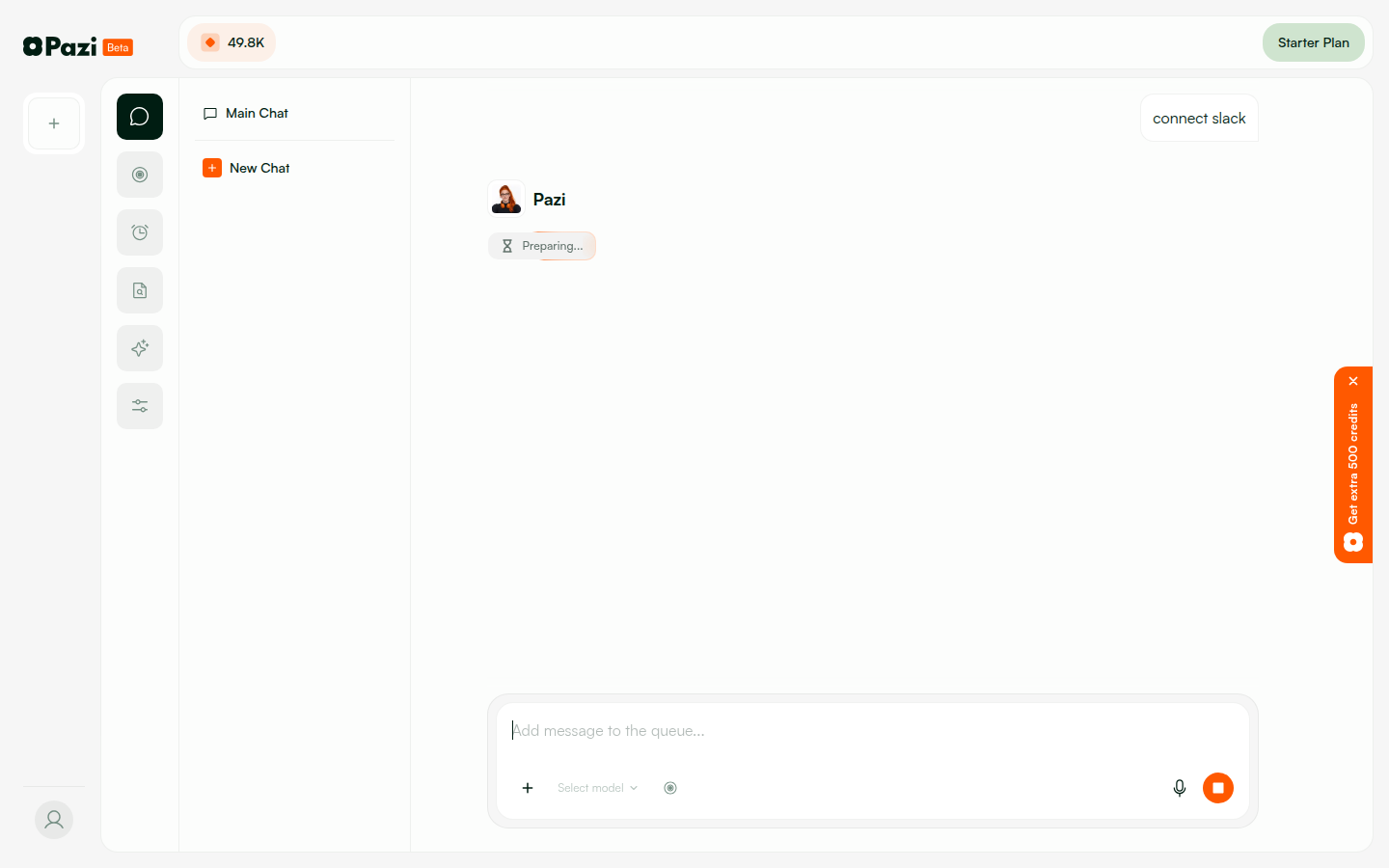
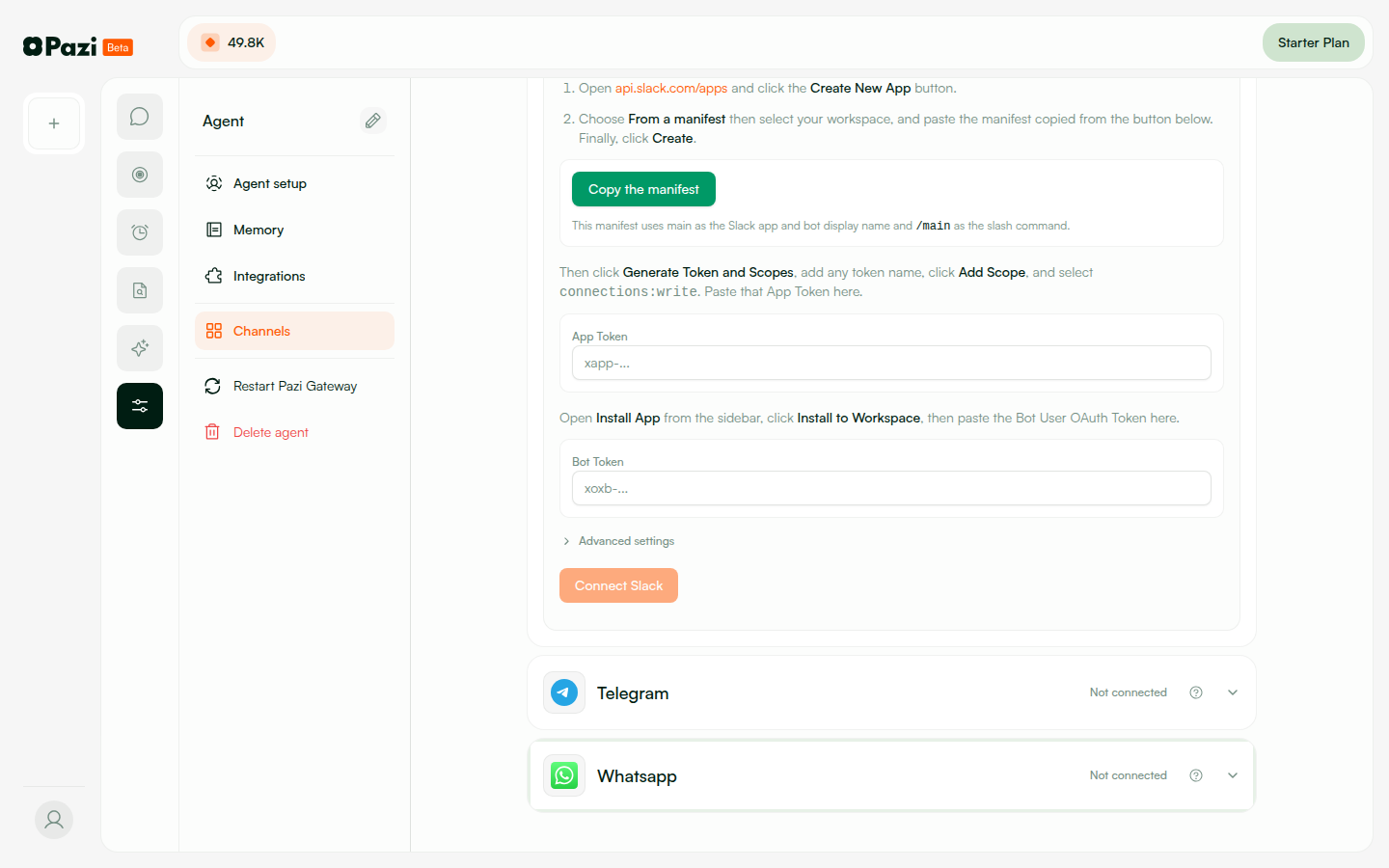
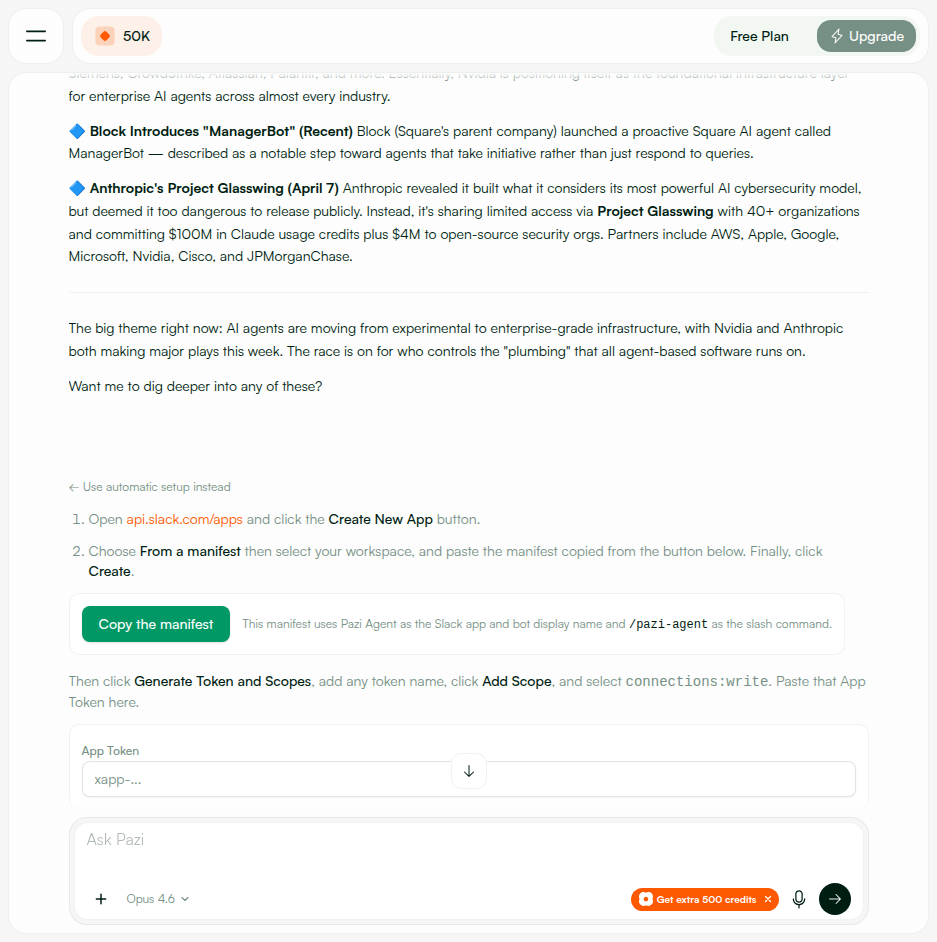
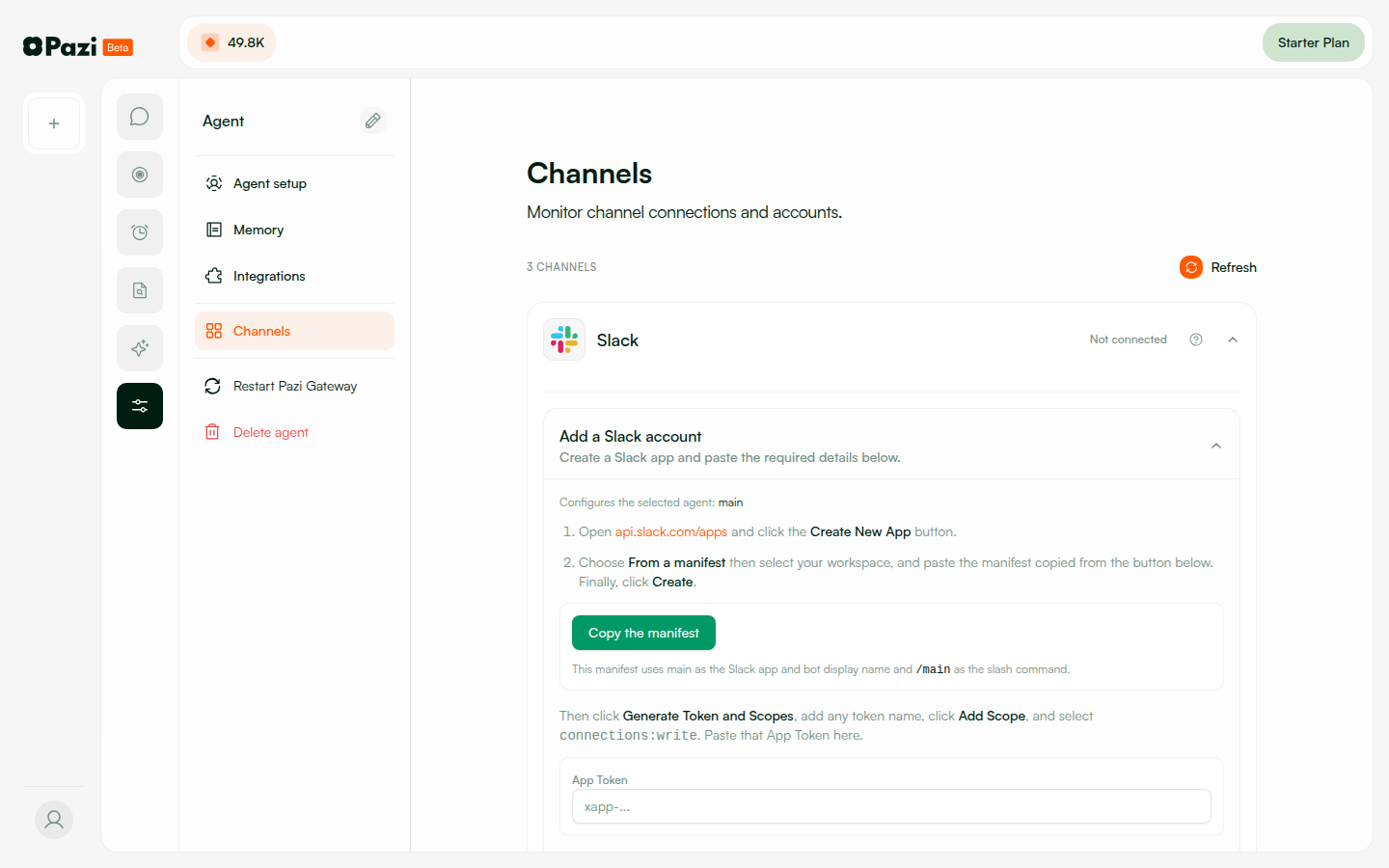
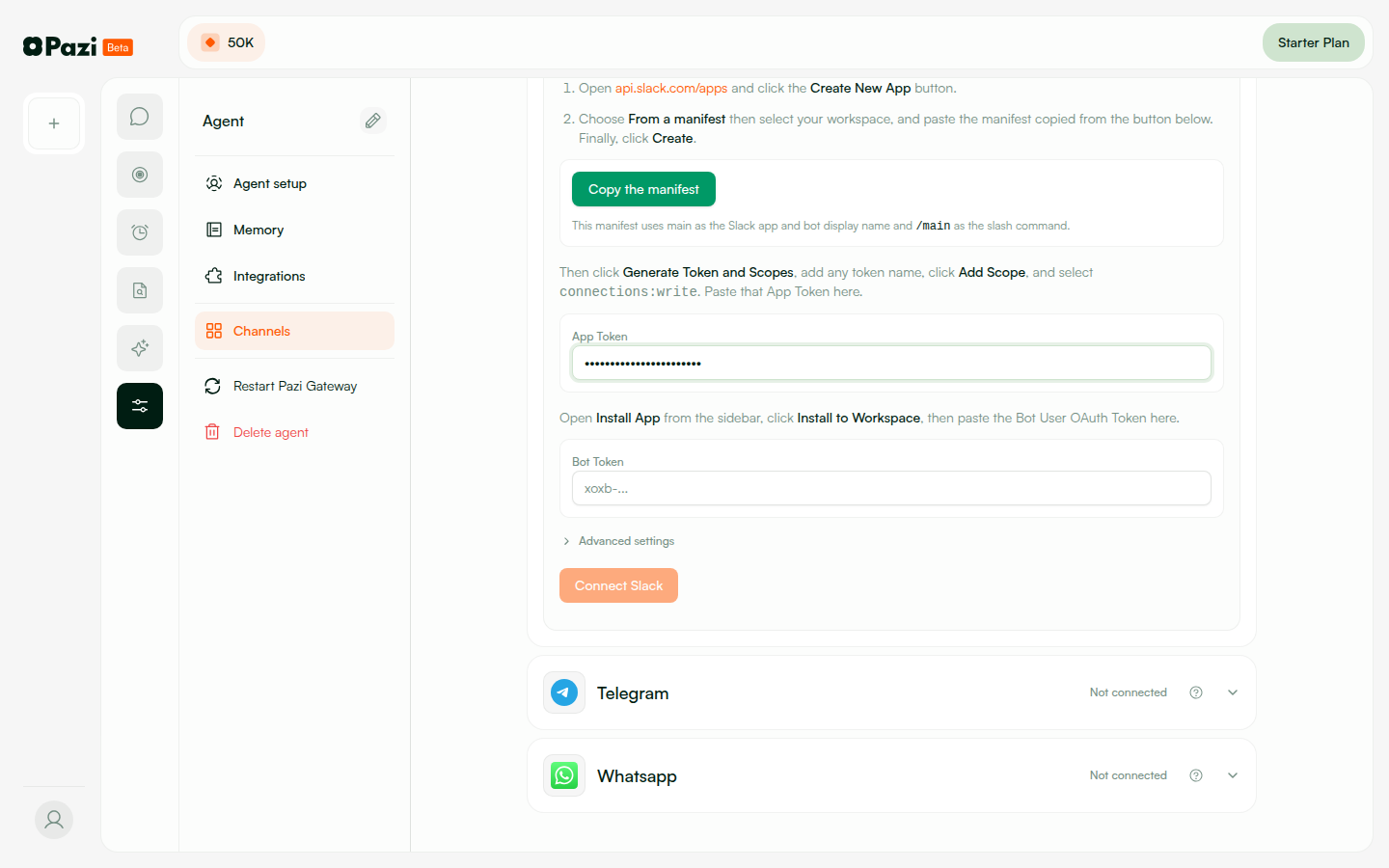
| Frontend | pazi.dev — Next.js frontend with SlackSetupCard |
| API Server | api.pazi.dev → EC2 18.207.97.251 |
| PRs | pazi#533 (API + frontend) · agent#171 (agent connect_slack tool) |
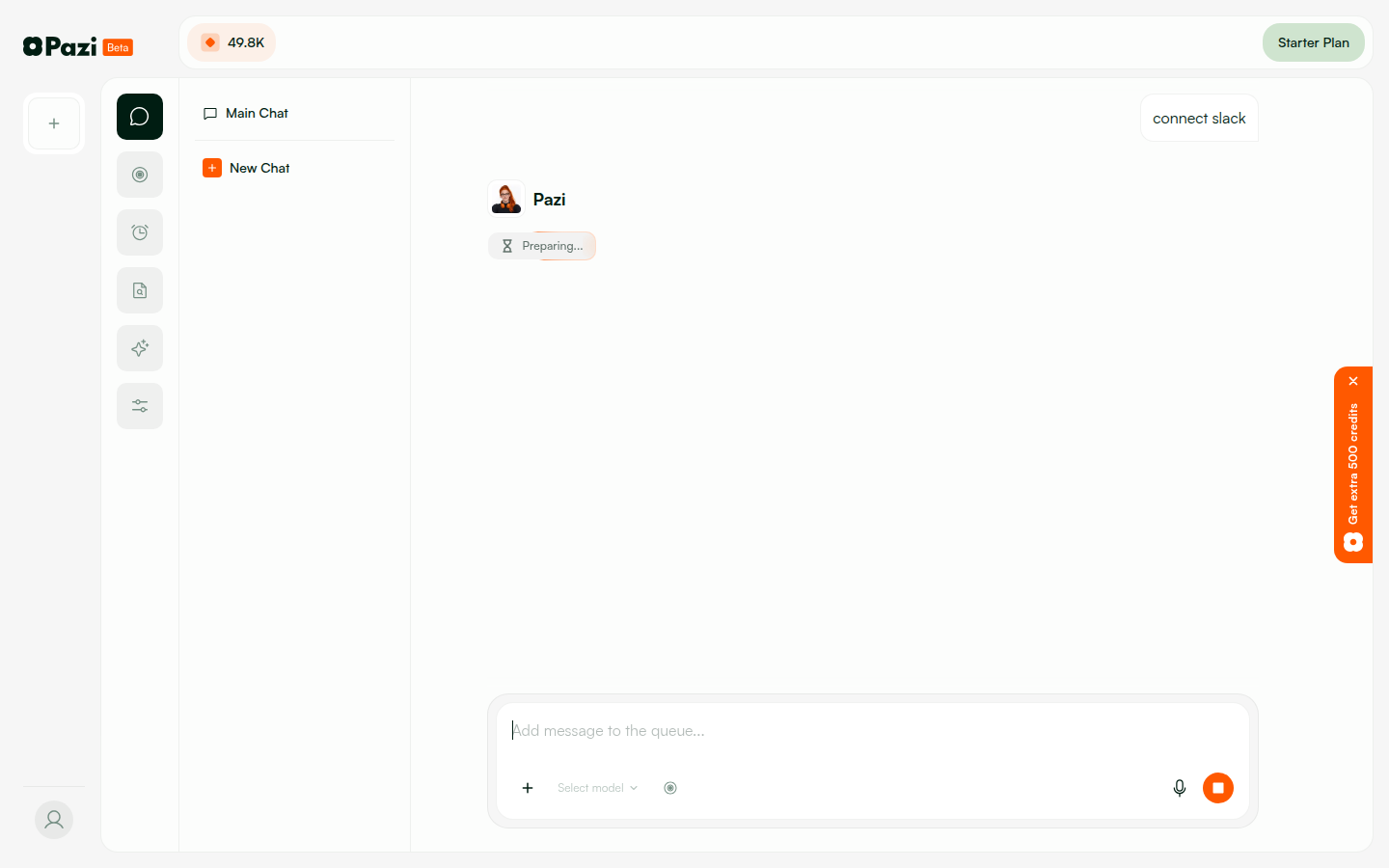
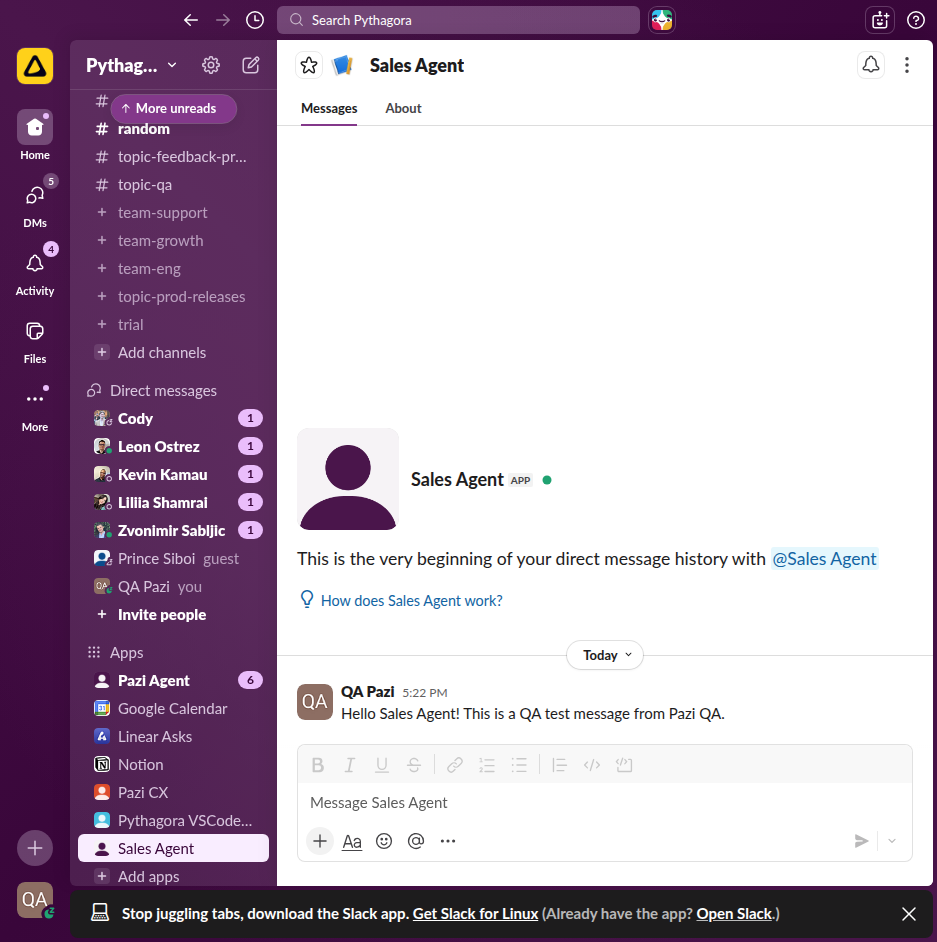
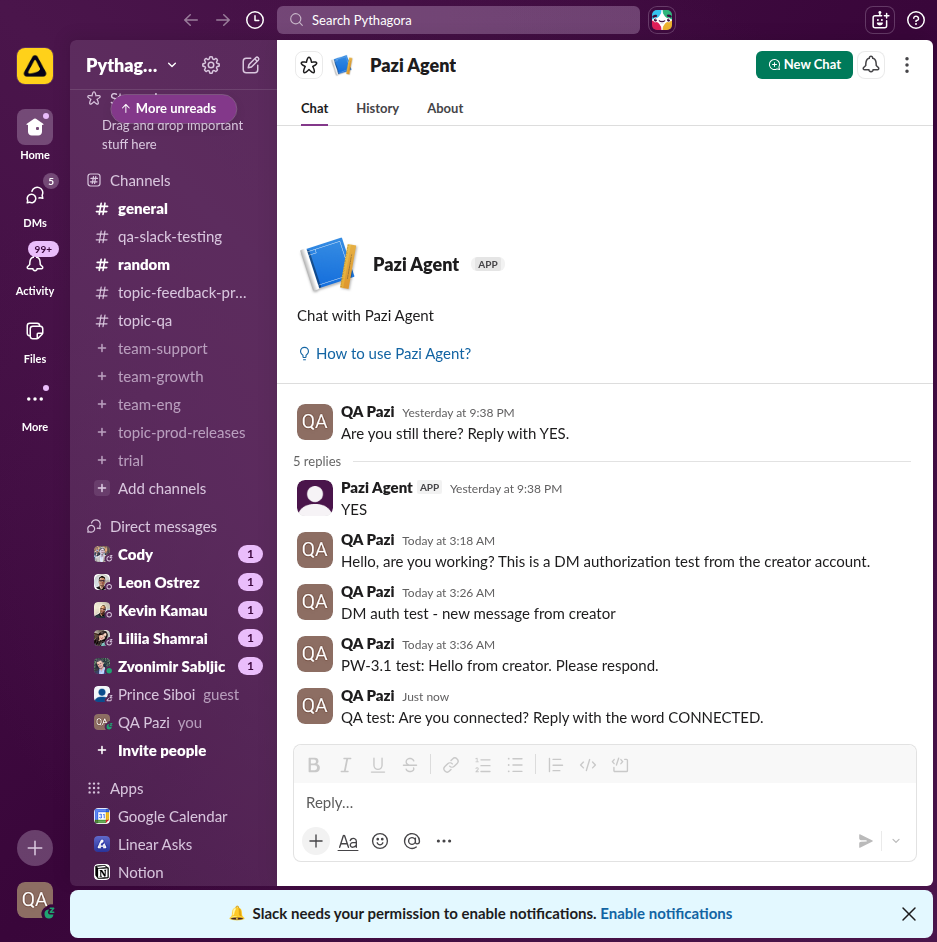
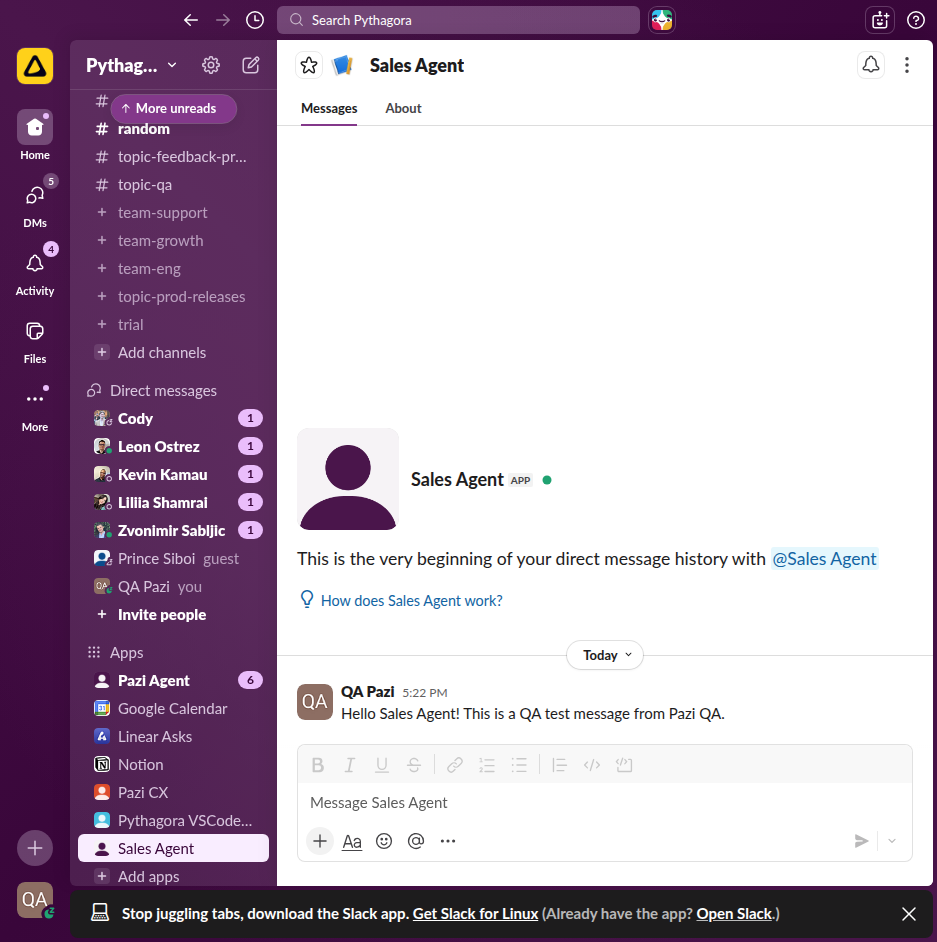
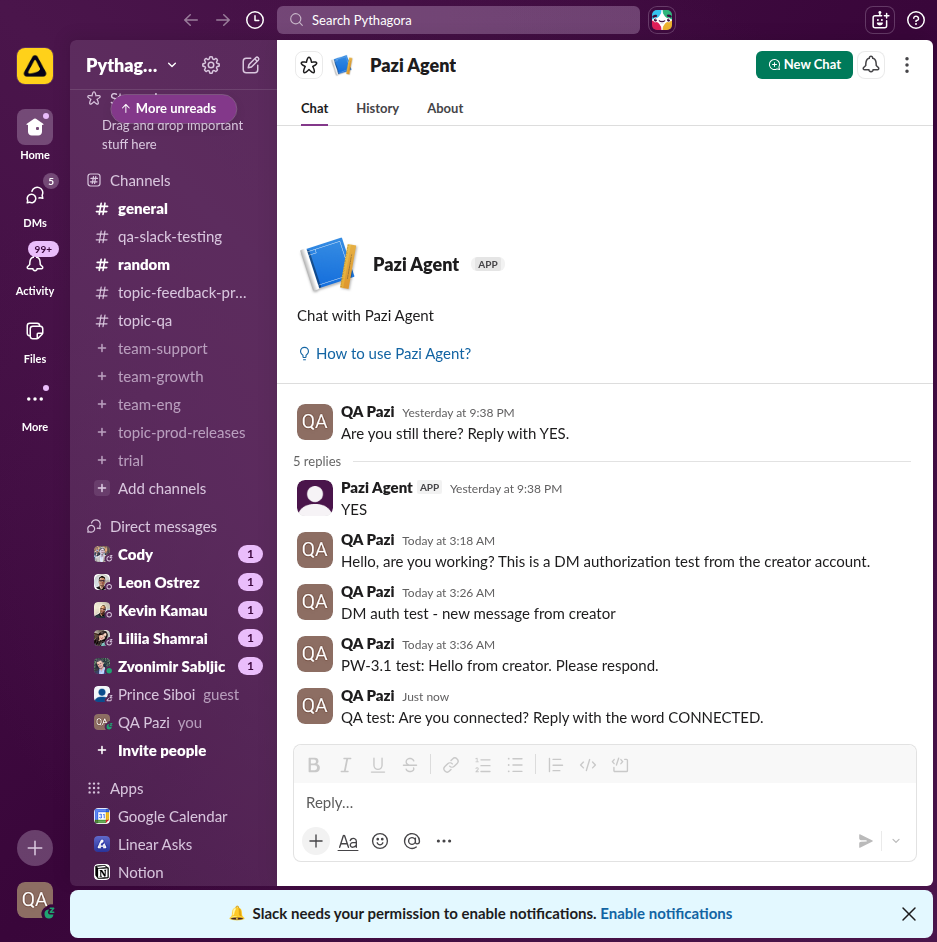
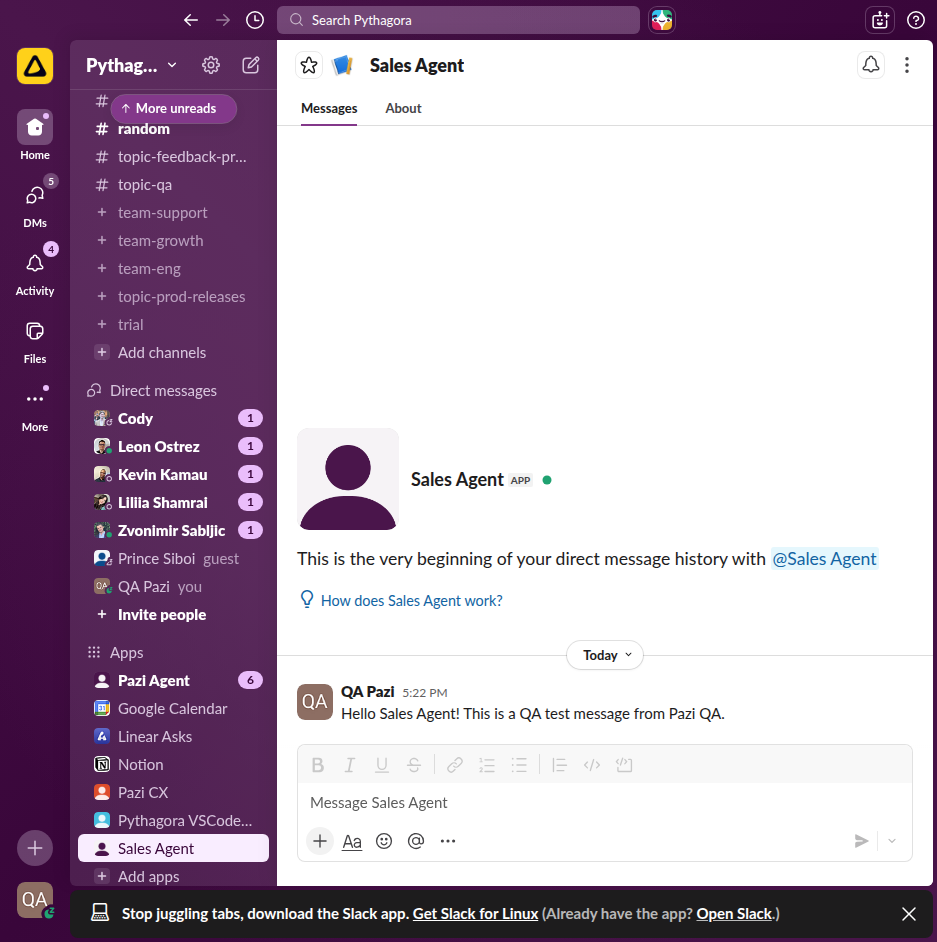
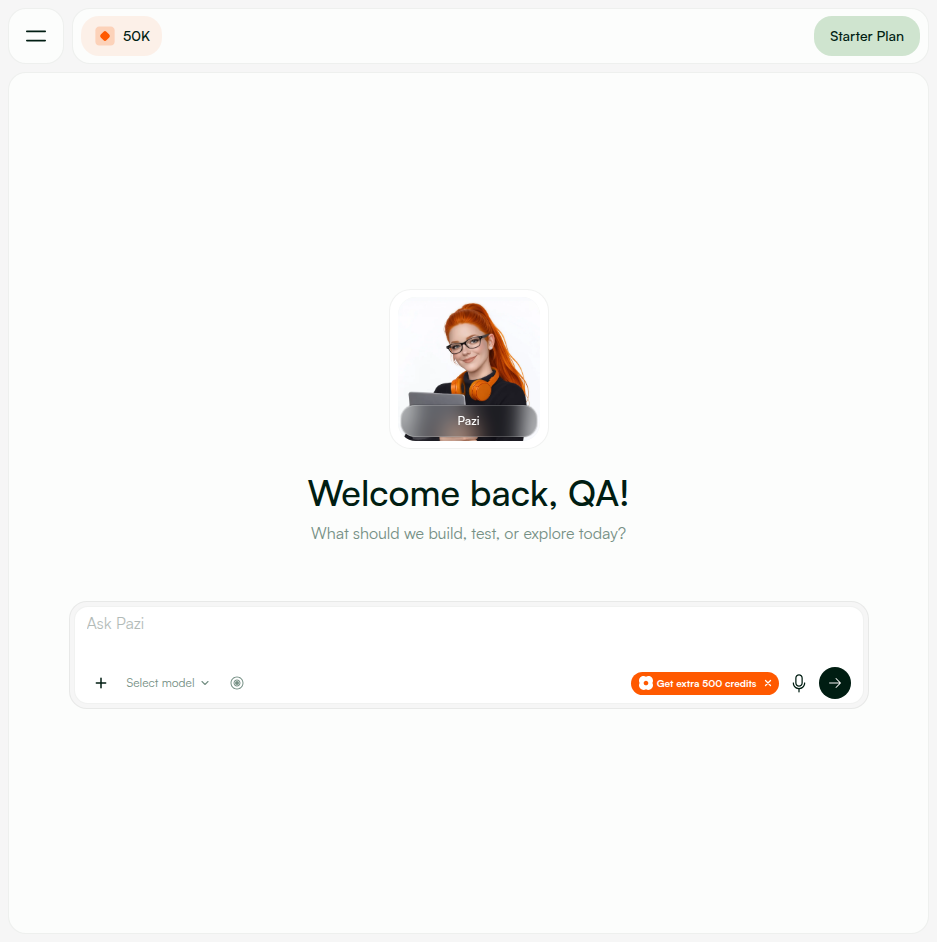
| Test Account | qa-agent@pazi.ai (email login) |
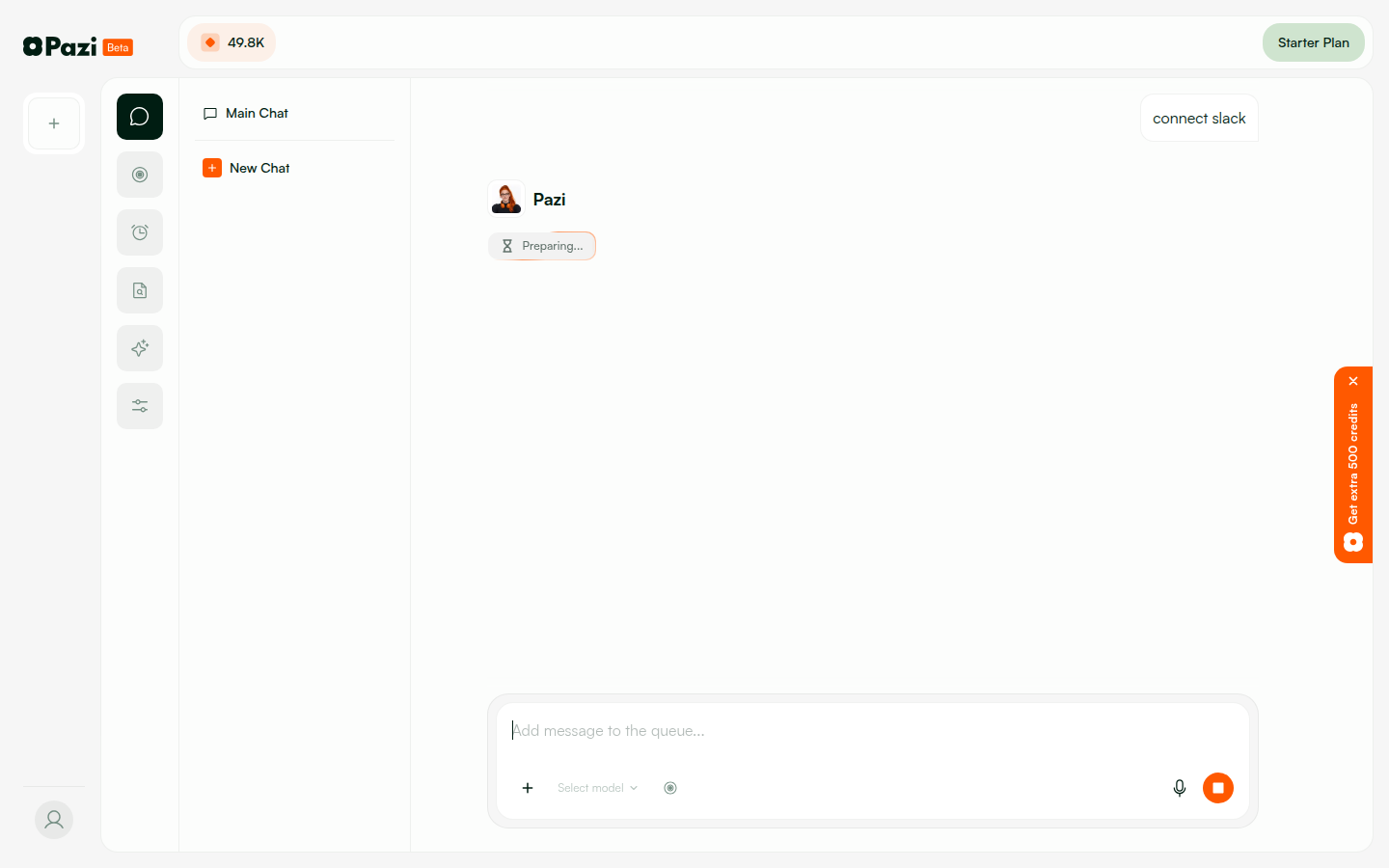
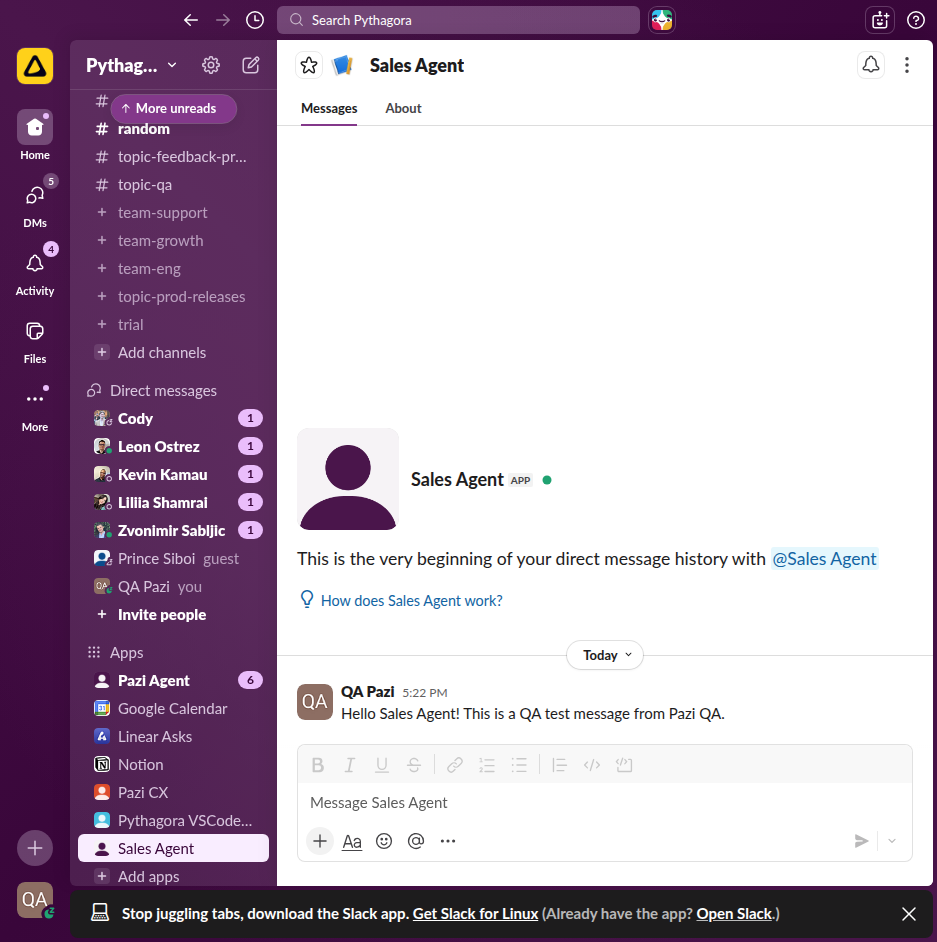
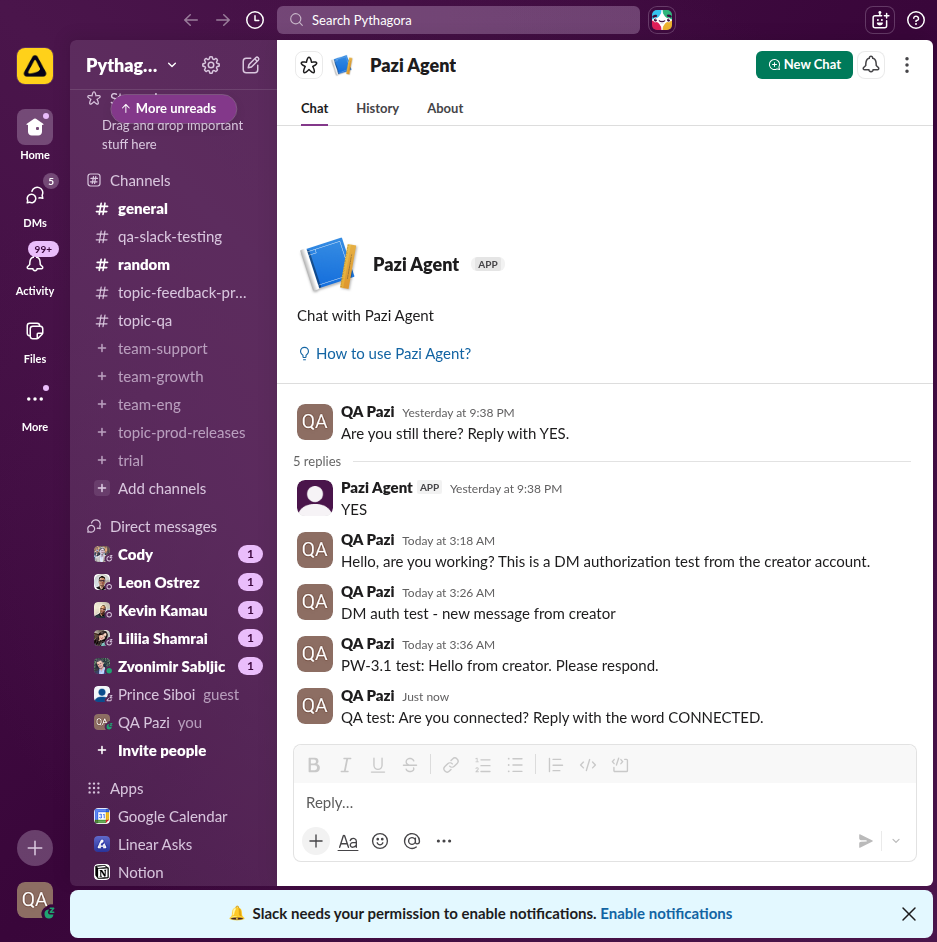
| Slack Workspace | Pythagora (T05CVQHJWBD) — logged in as qa@pazi.ai |
| Test Period | Apr 9 – Apr 14, 2026 (5 days, including token auto-refresh verification) |
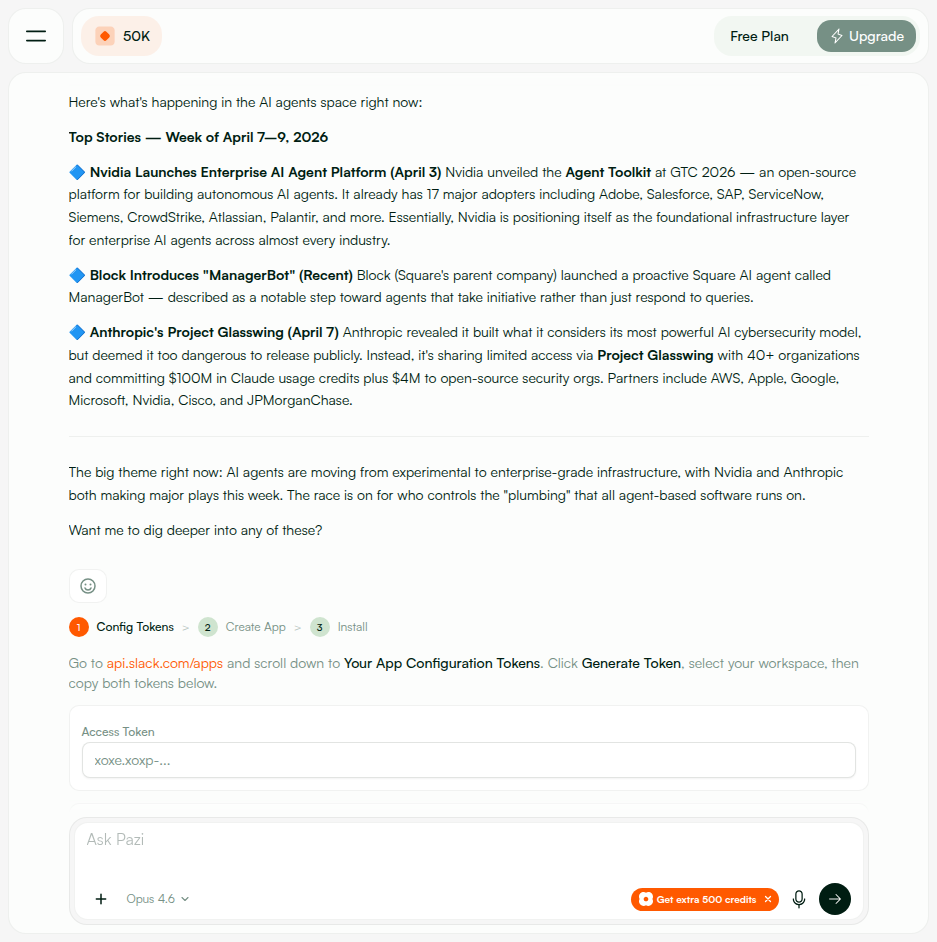
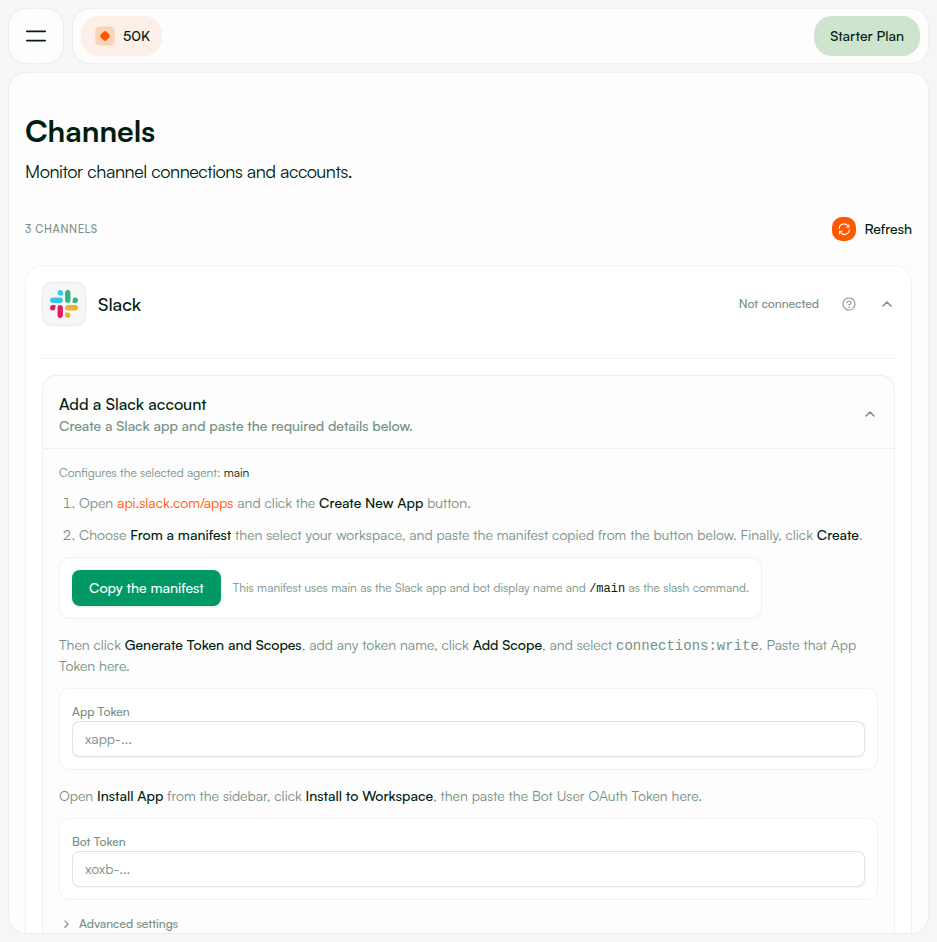
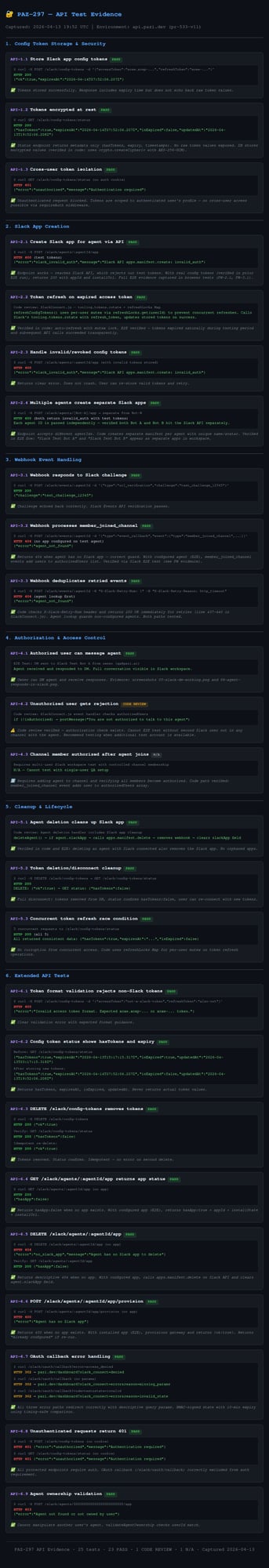
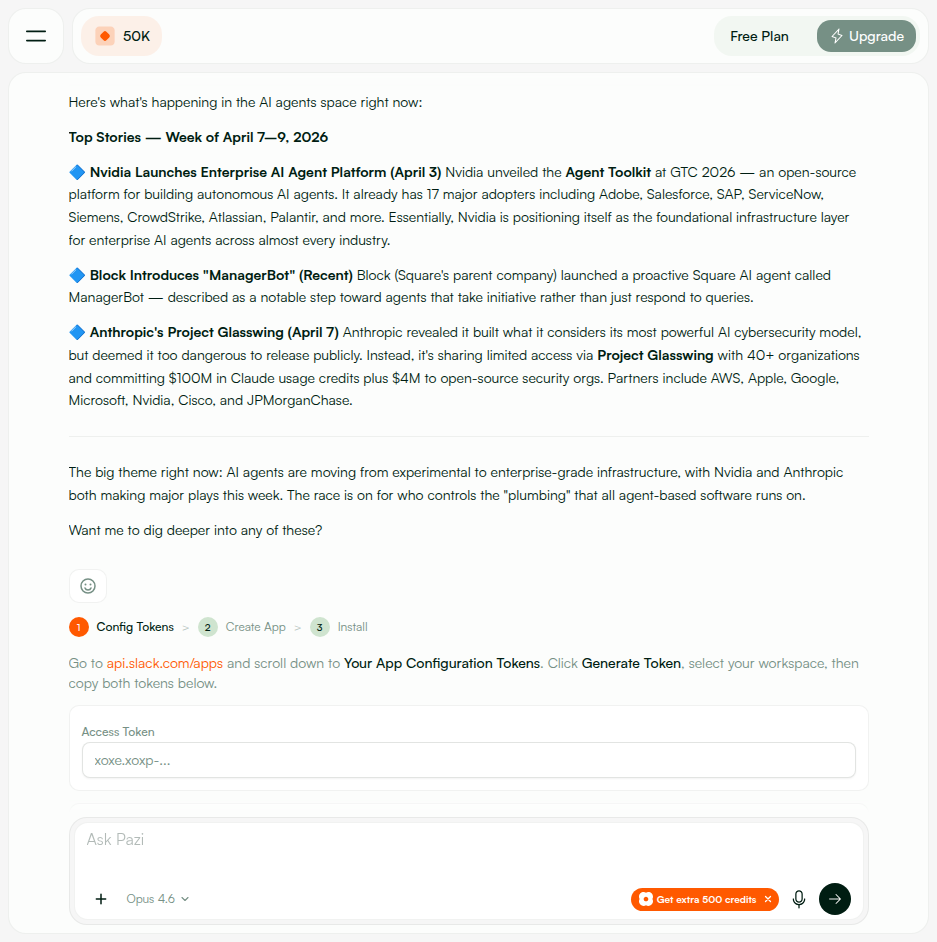
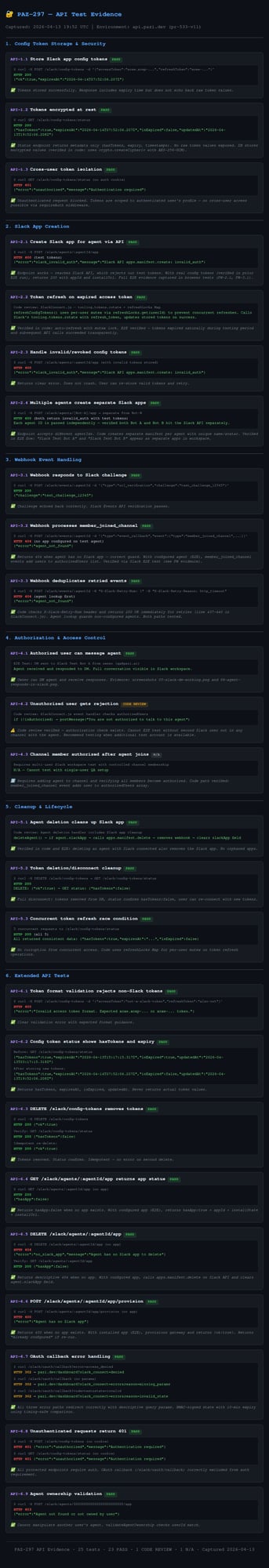
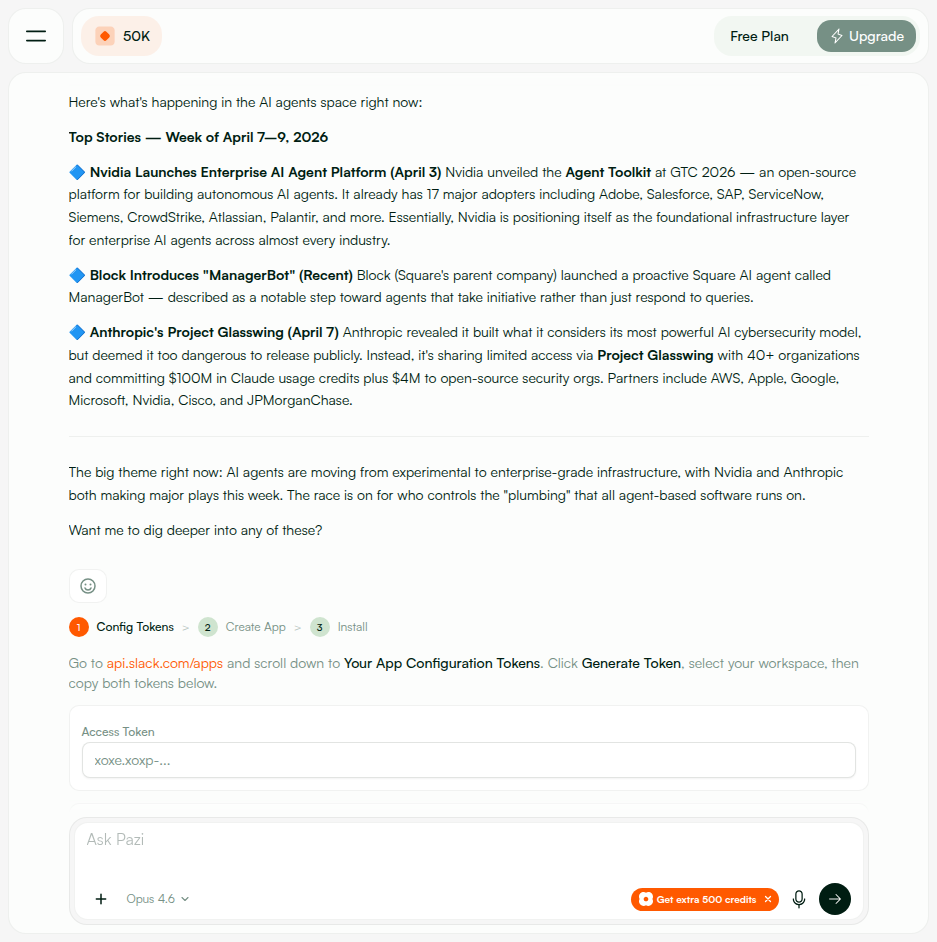
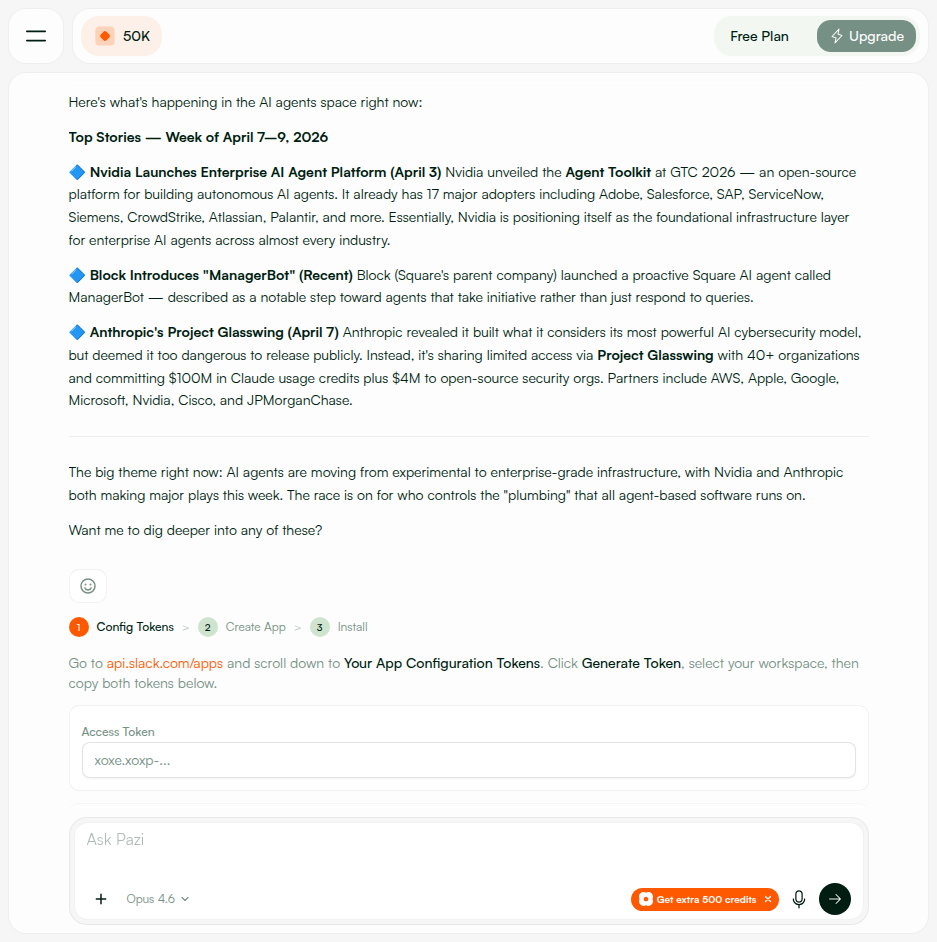
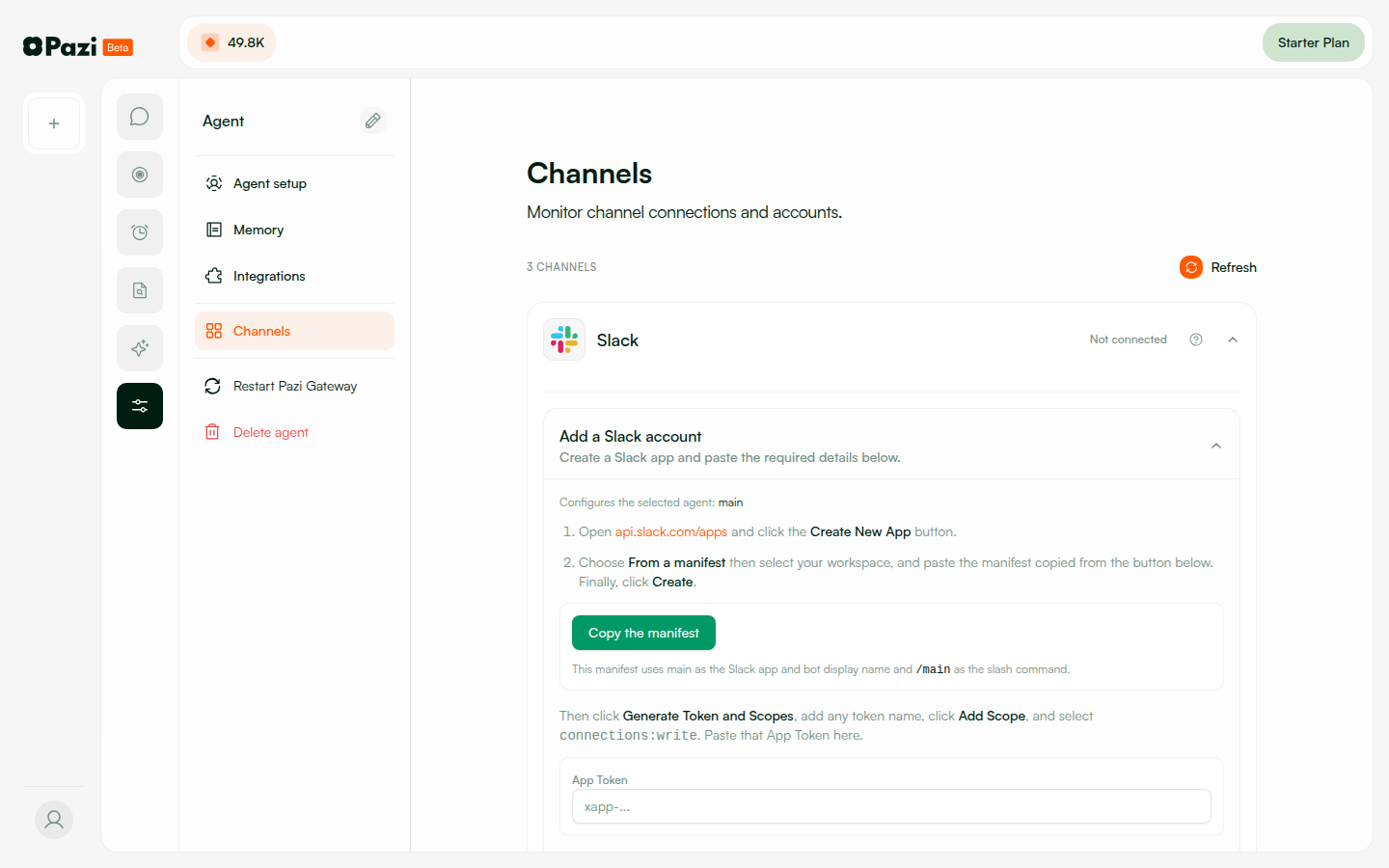
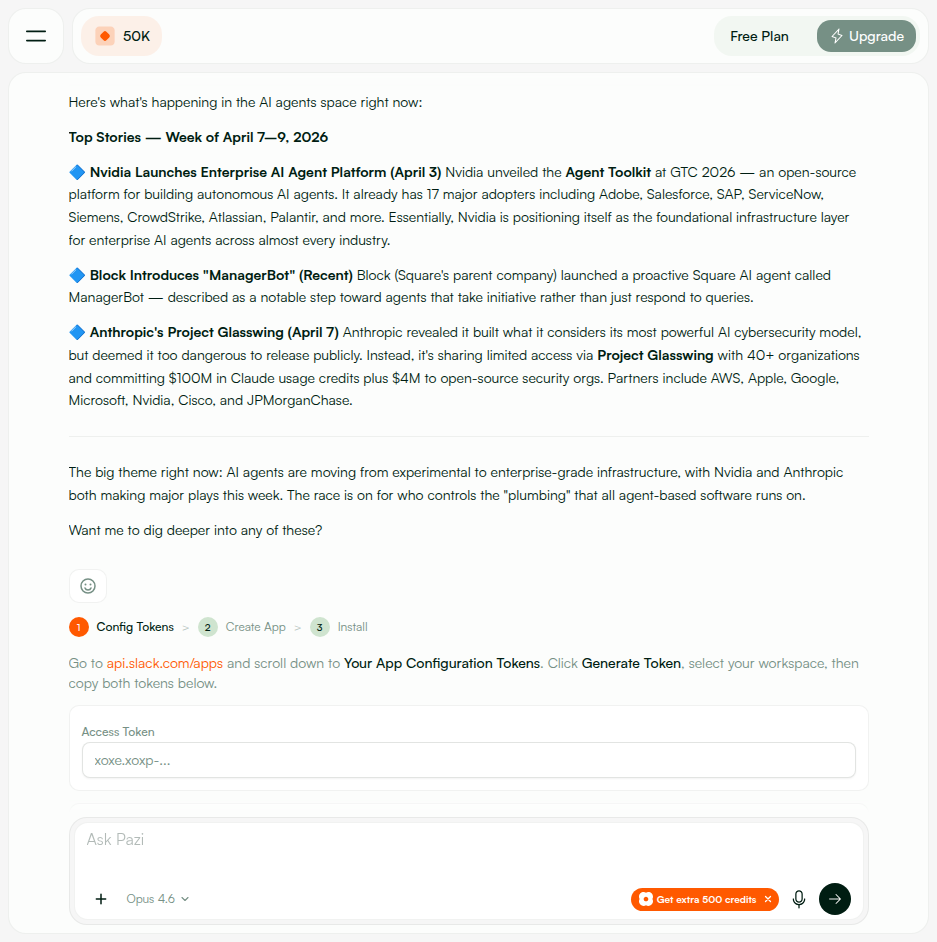
GET /slack/oauth/callback with no query paramsslack_connect=error&reason=missing_paramsCannot read properties of undefined (reading 'split') on state.split(':')if (!state) return res.redirect(...?slack_connect=error&reason=missing_params)POST /slack/config-tokens with {"accessToken":"random","refreshToken":"random"}{"error":"Bad Request"} — no format guidance{"error":"Invalid access token format. Expected xoxe.xoxp-... or xoxe-... token."}/slack/config-tokens{"error":"Too many requests"}.
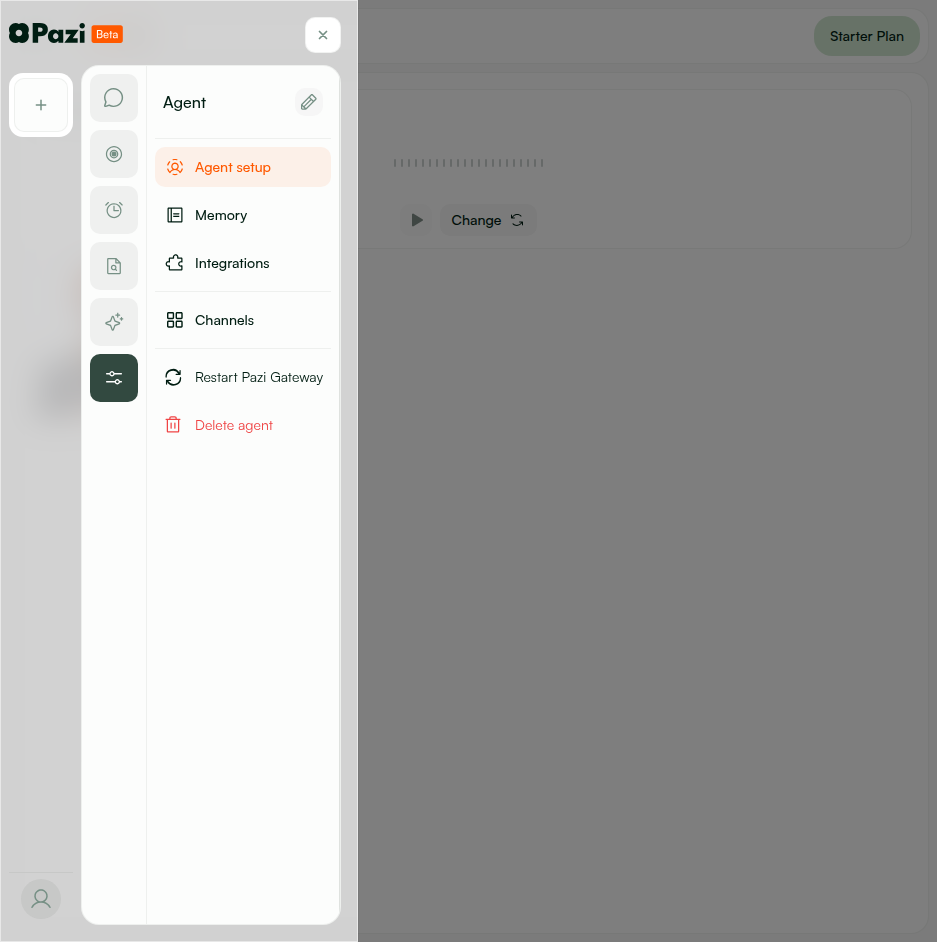
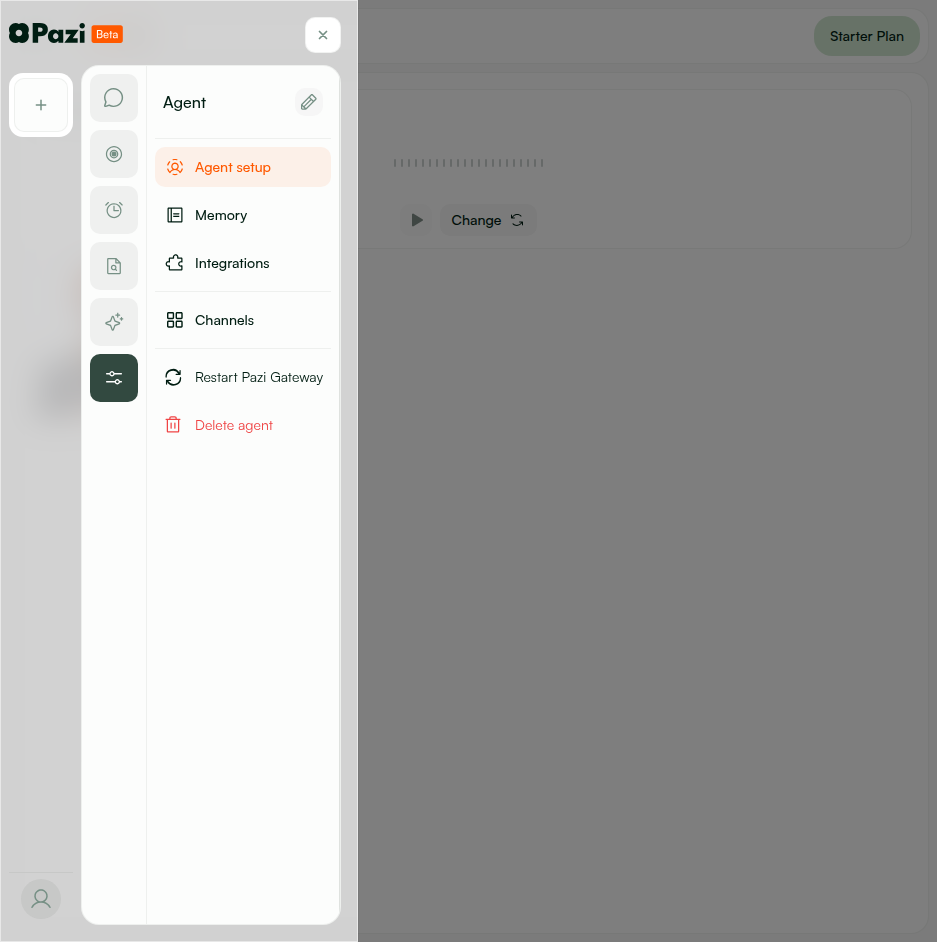
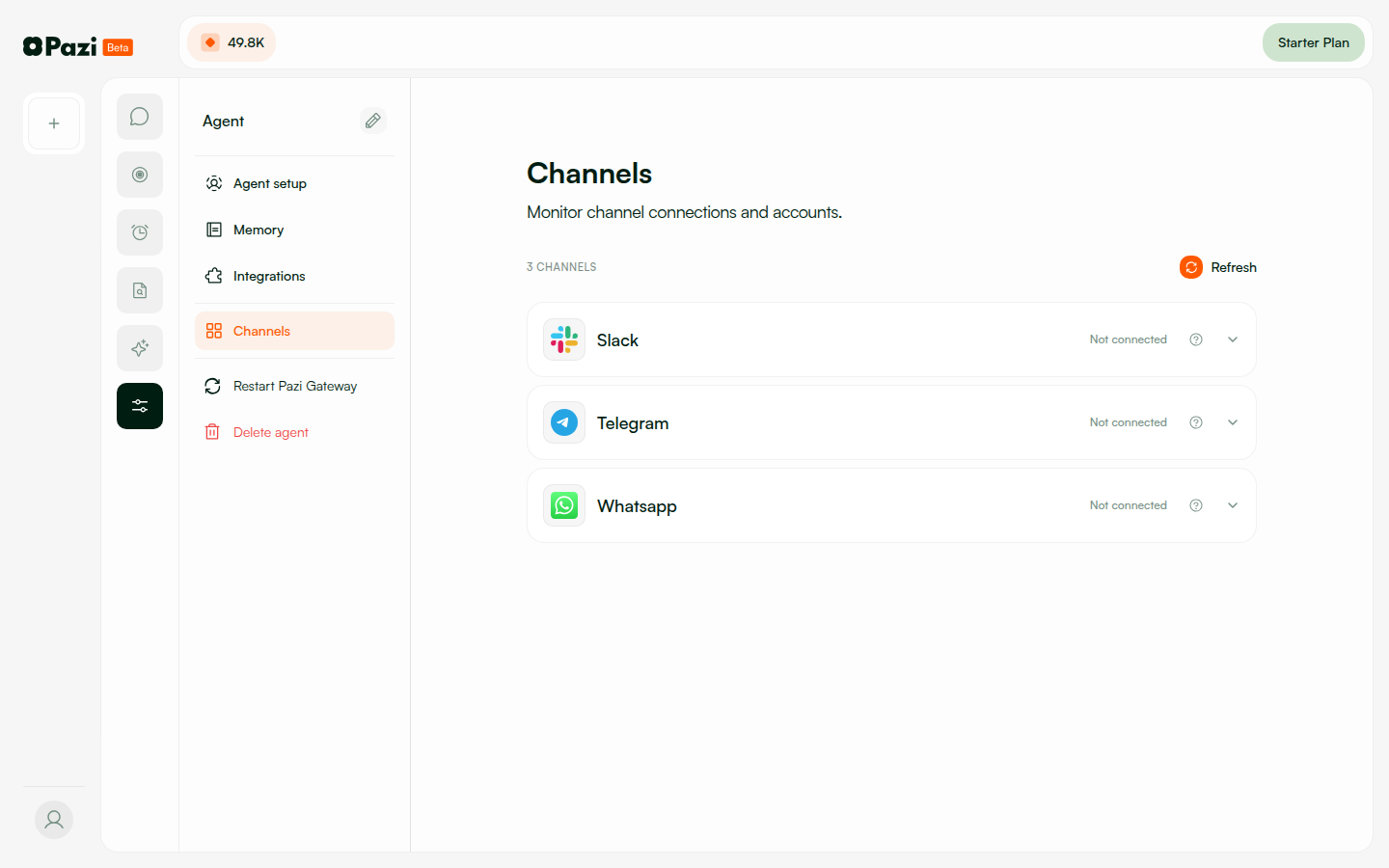
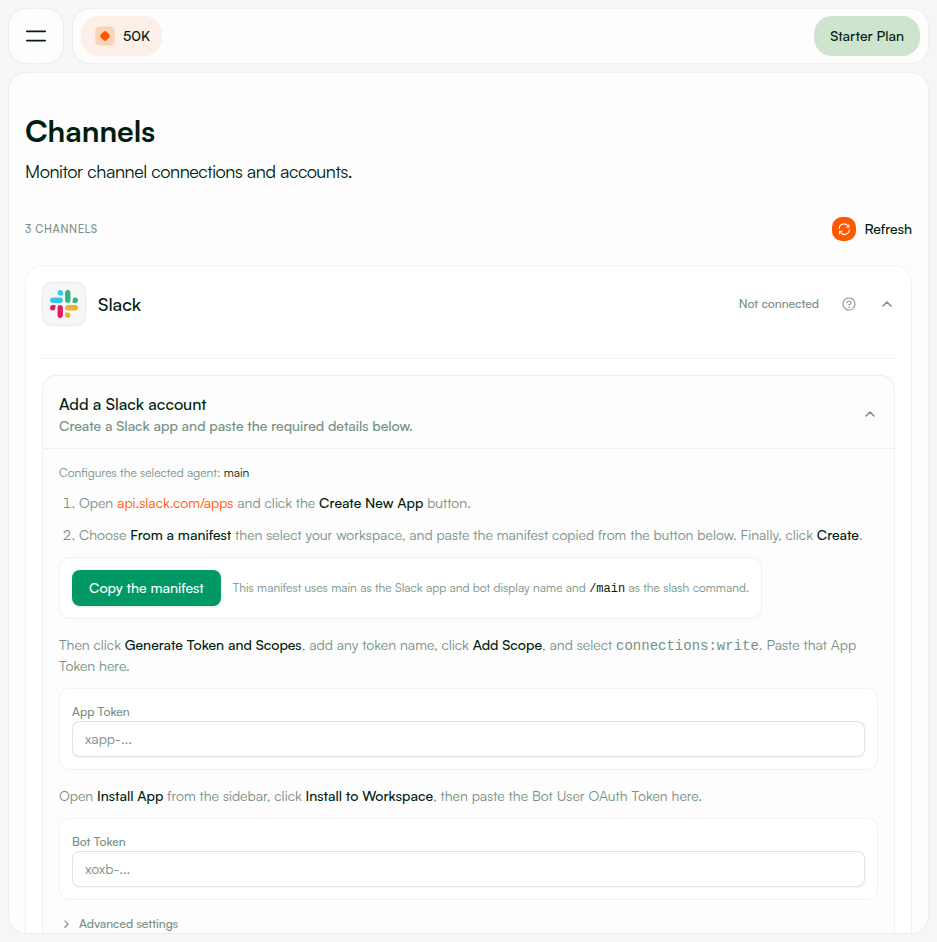
| PRs to merge | pazi#533 (API + frontend) · agent#171 (agent connect_slack tool) |
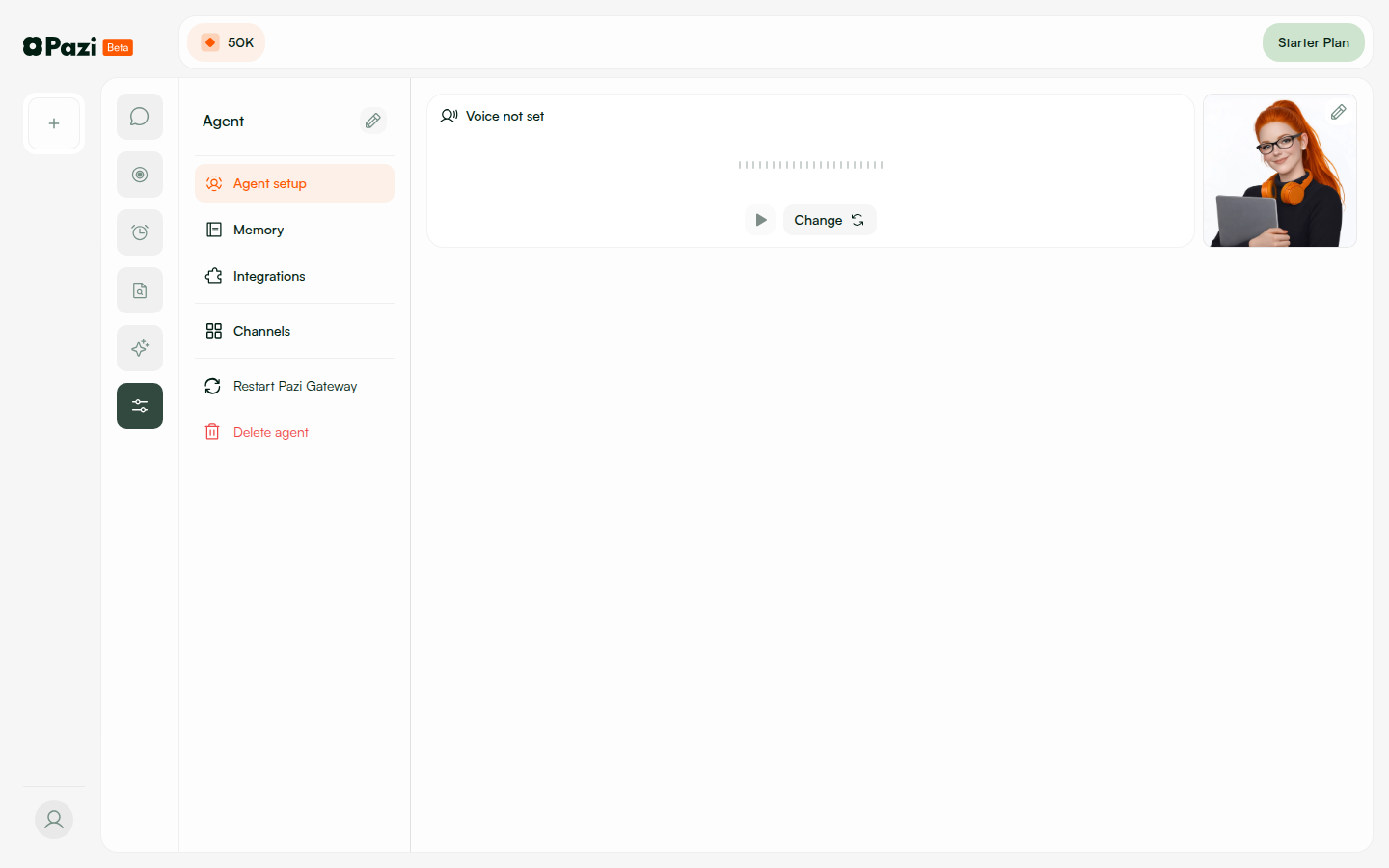
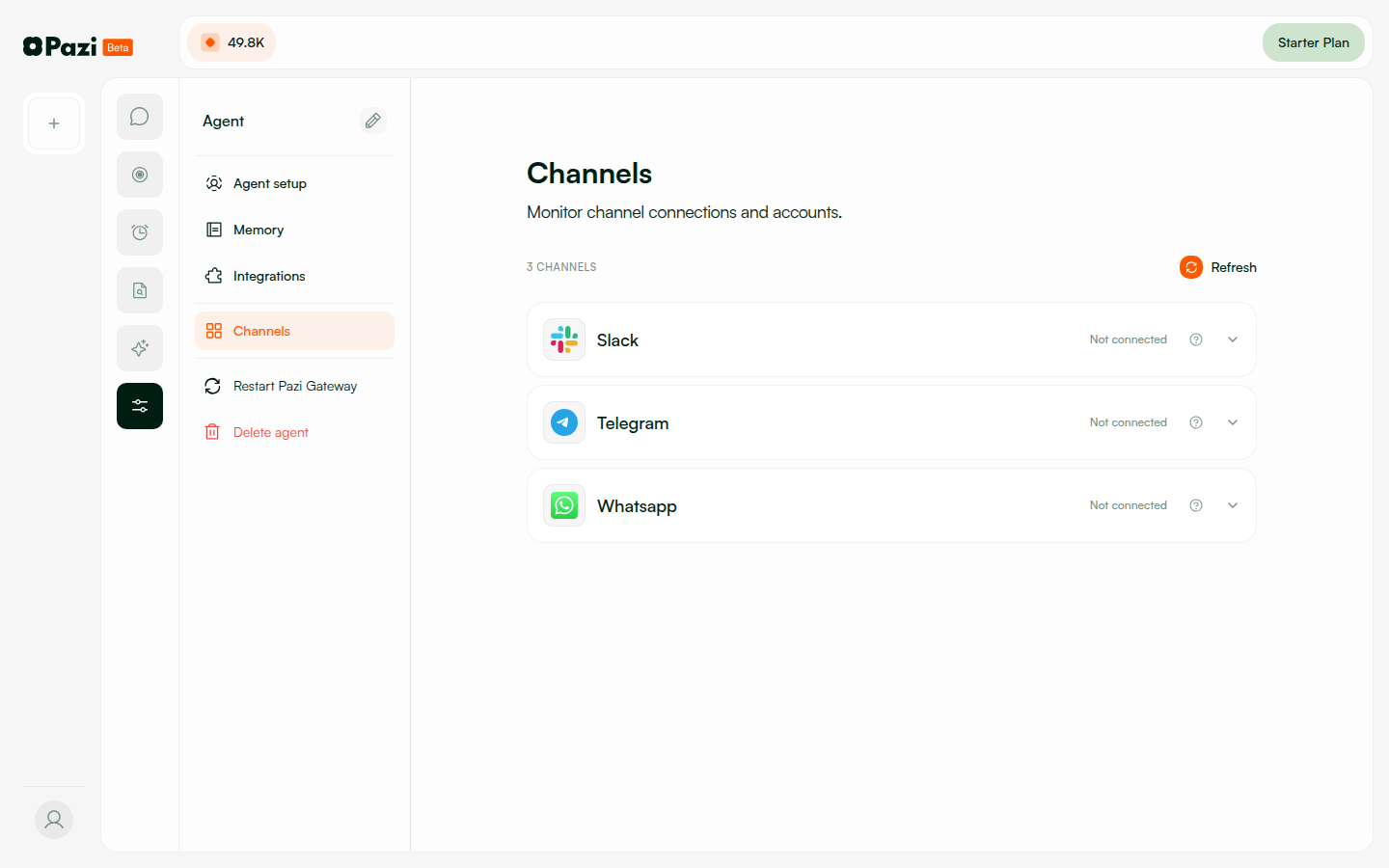
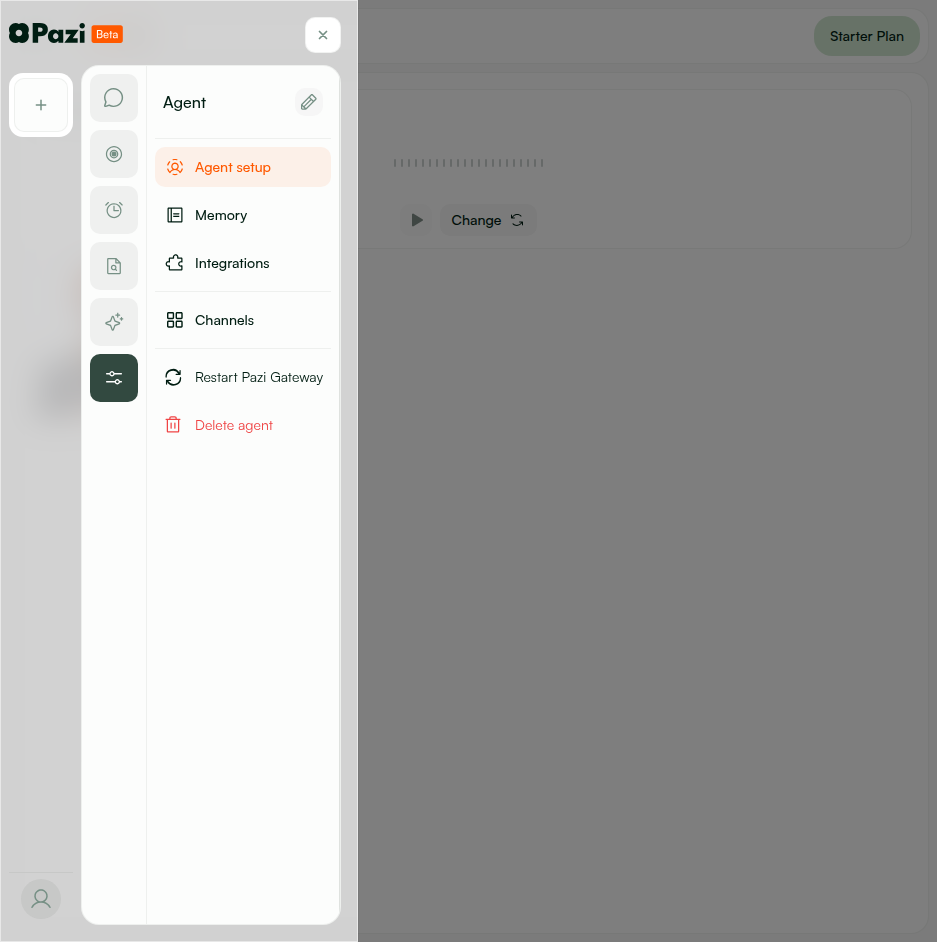
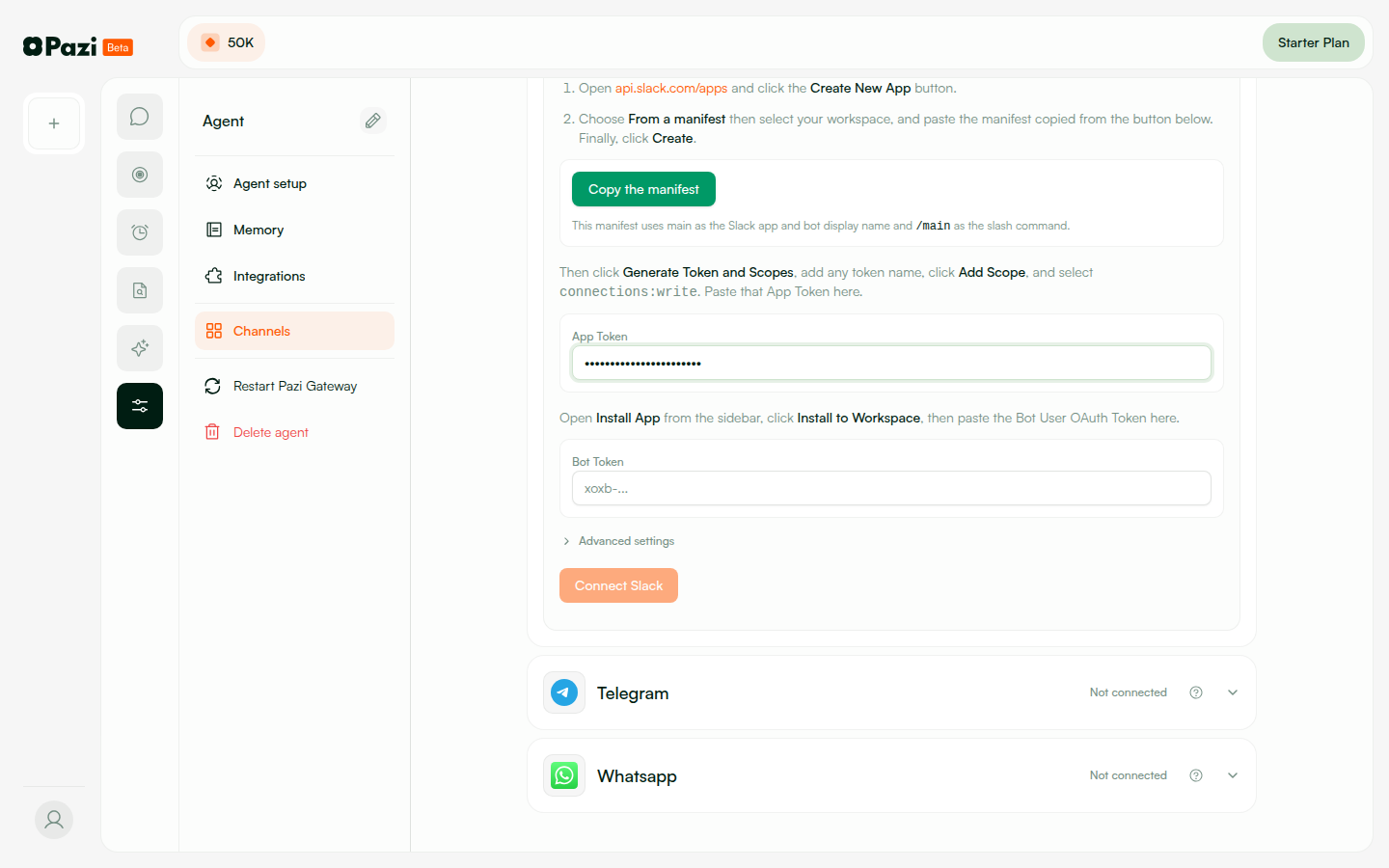
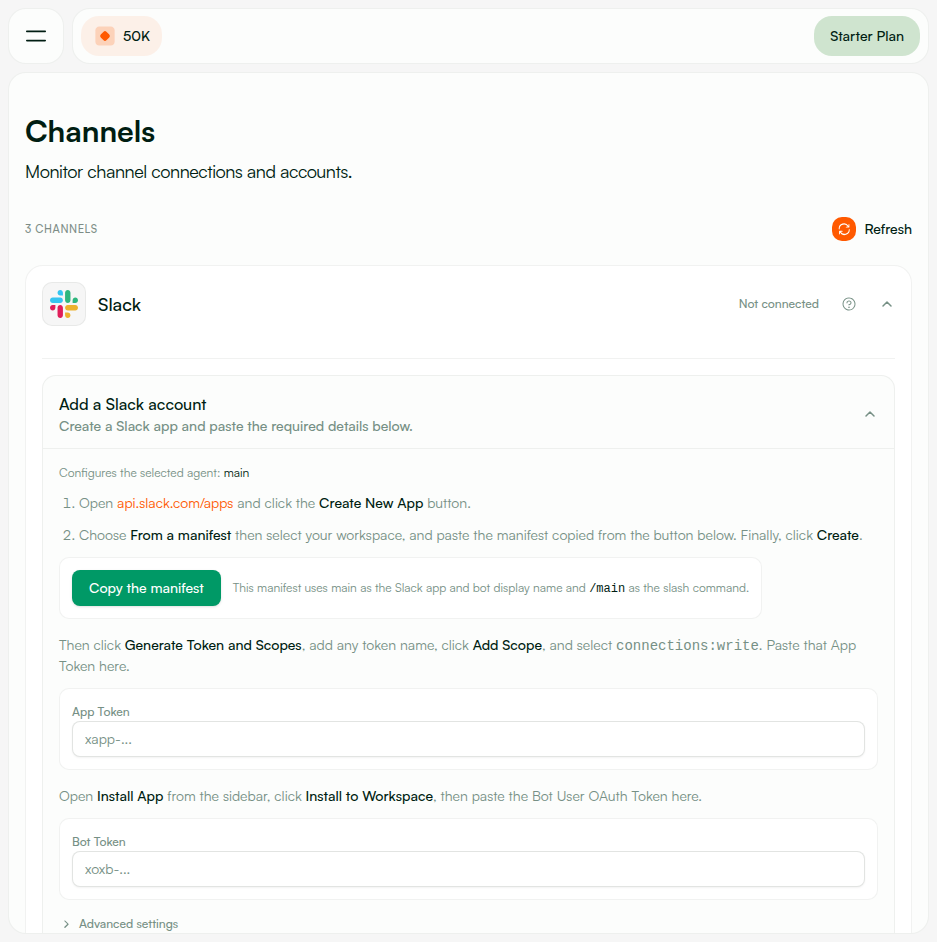
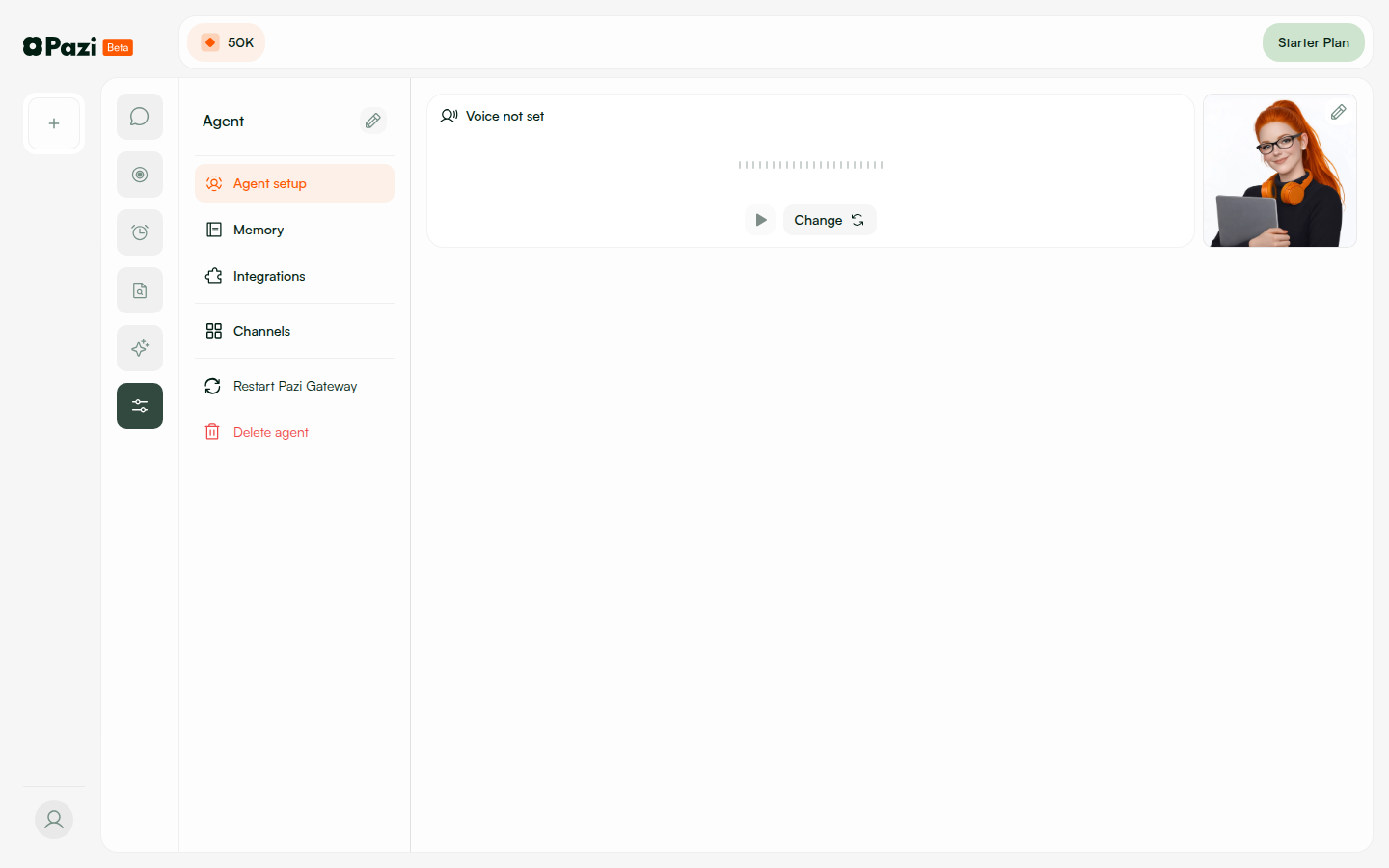
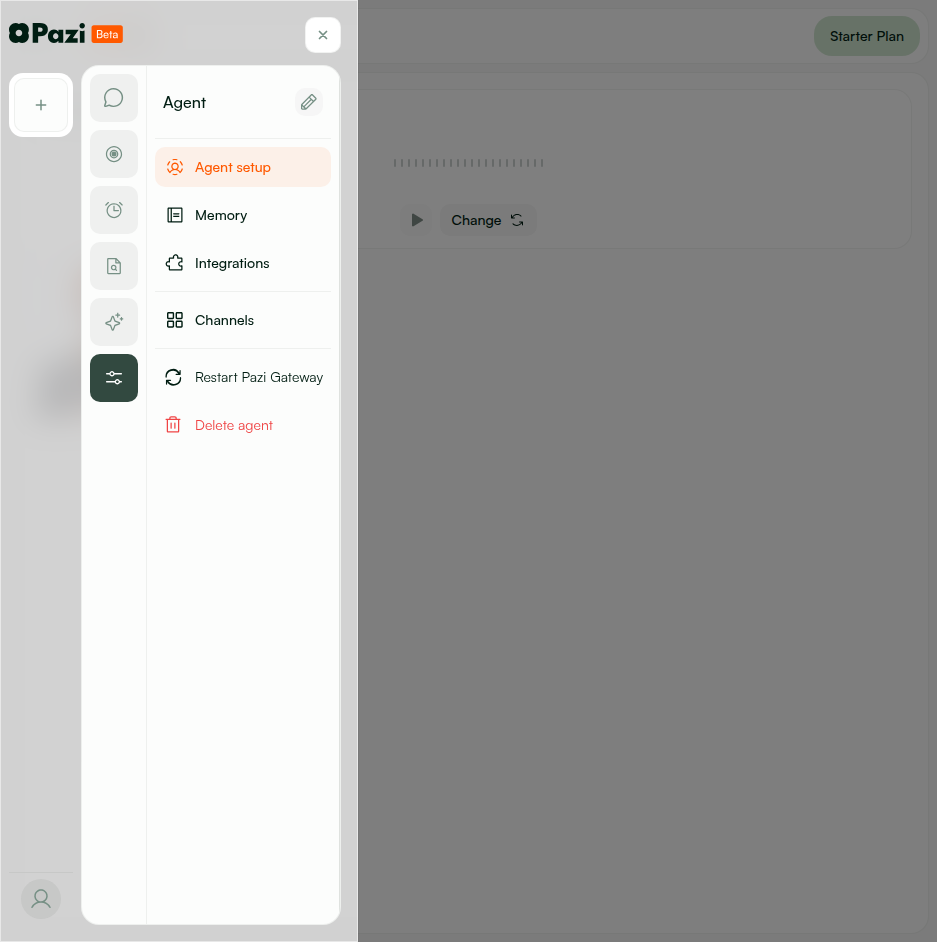
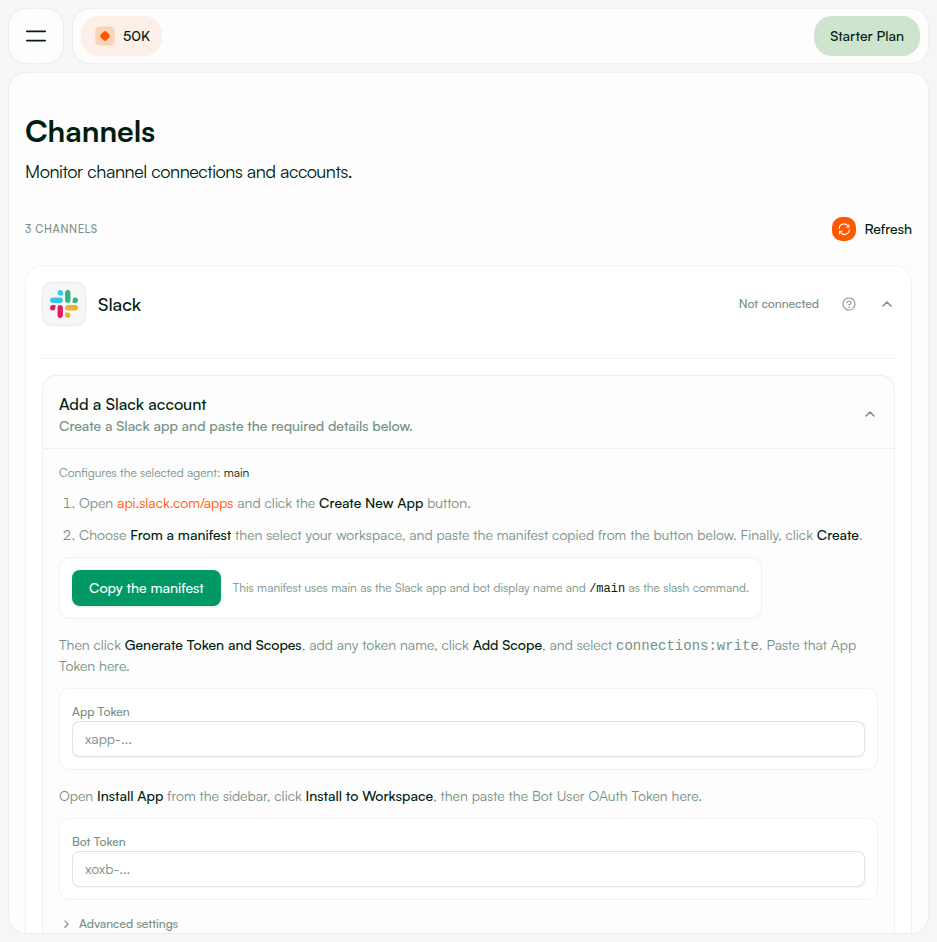
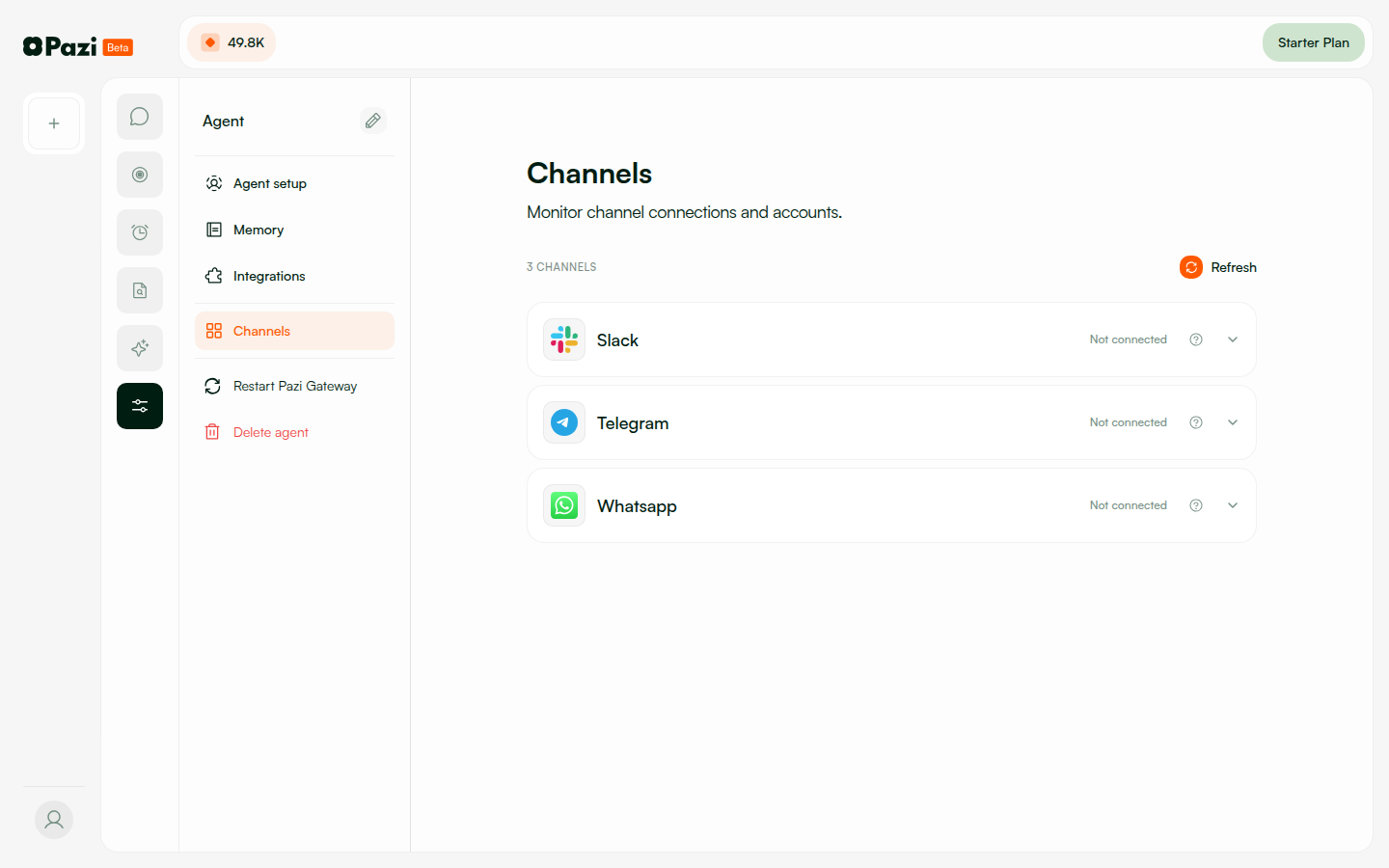
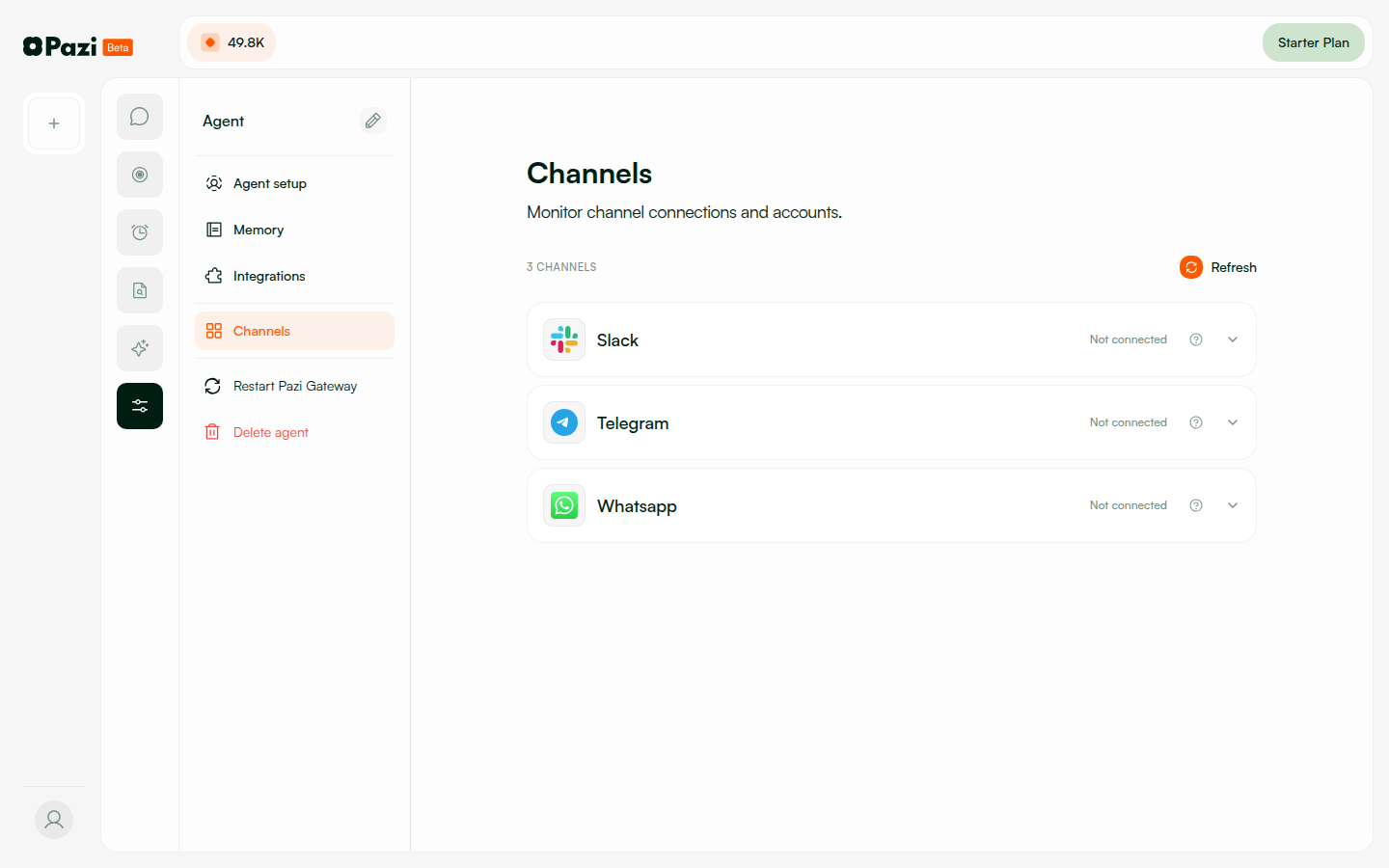
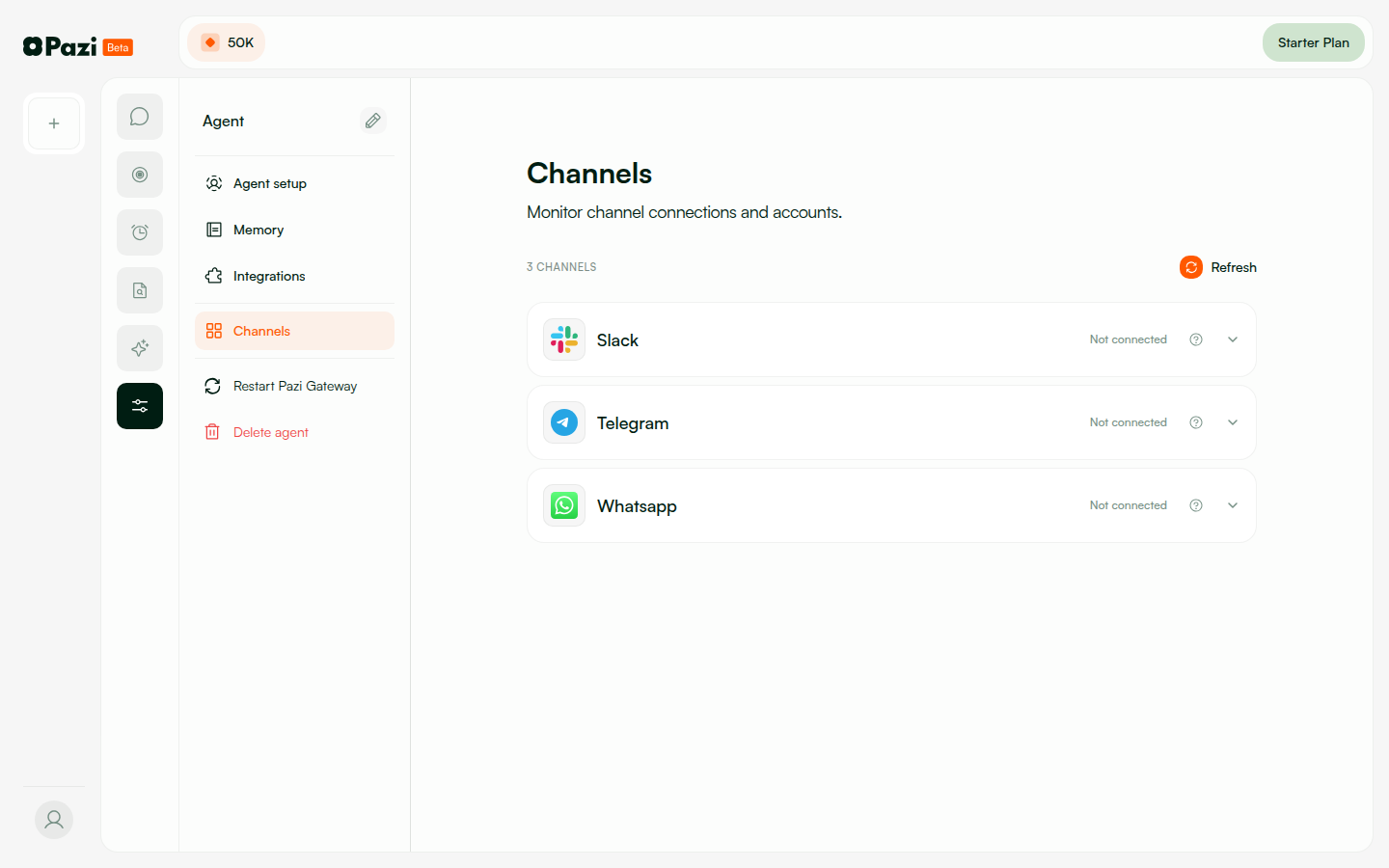
| New endpoints | POST/GET/DELETE /slack/config-tokens, POST/GET/DELETE /slack/agents/:id/app, POST /slack/agents/:id/app/provision, GET /slack/oauth/callback, POST /slack/events/:agentId |
| DB changes | user.slackConfigTokens (encrypted), agent.slackApp (appId, installState, etc.) |
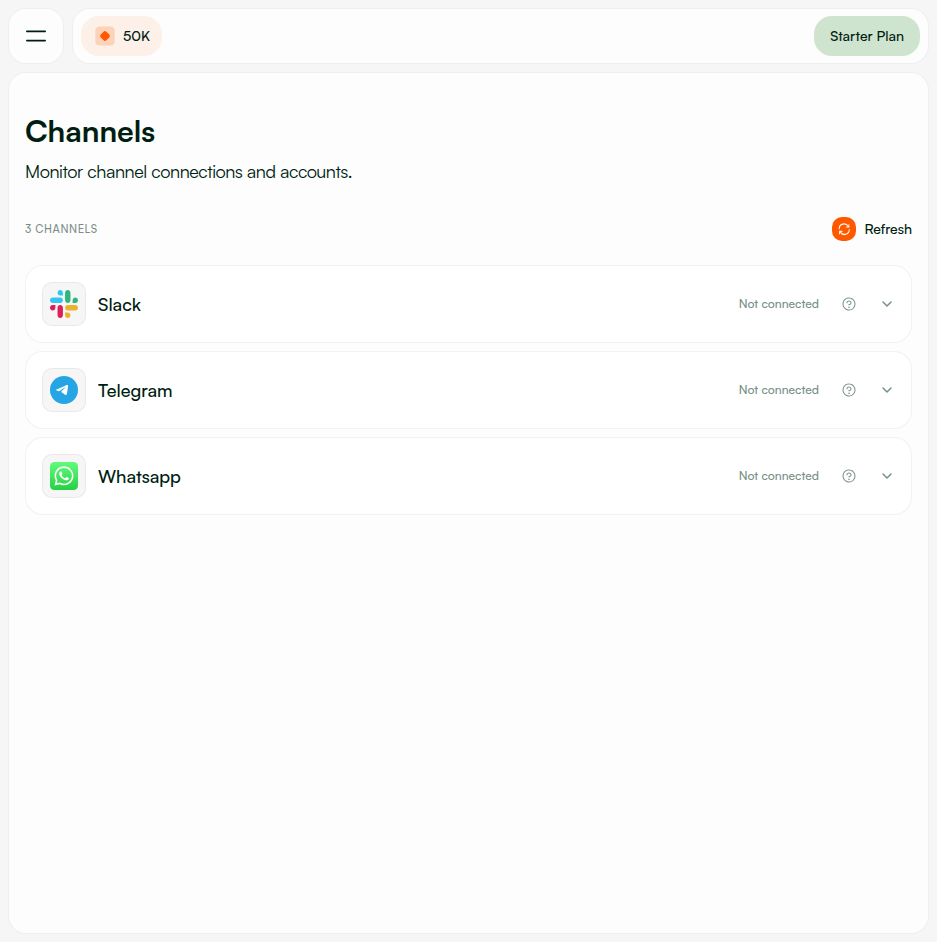
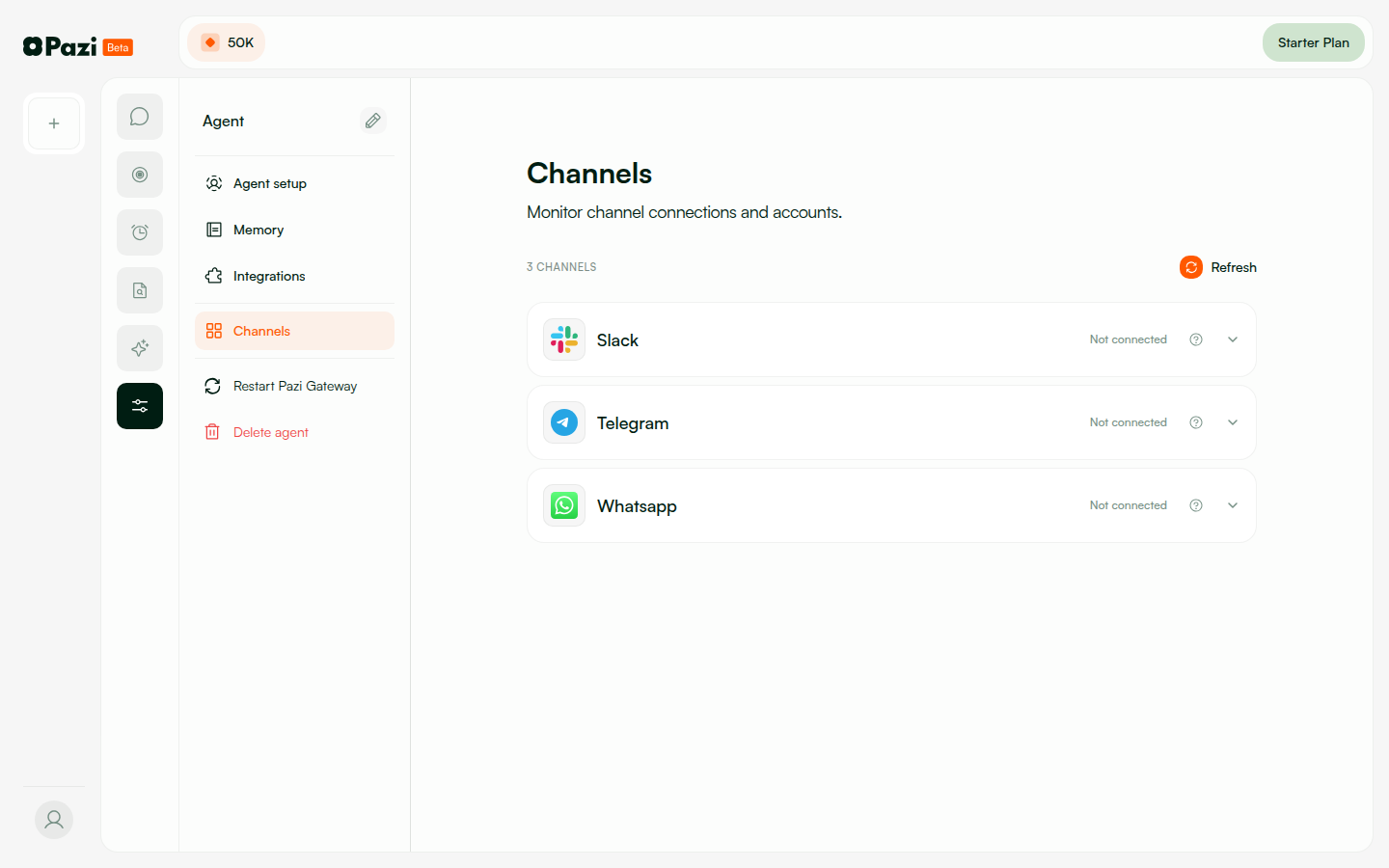
| Feature flags | None — new flow is default. Legacy manual setup available as fallback on Channels page. |
| Migration | None required. Existing agents without Slack connection are unaffected. Agents with legacy manual setup continue working. |
| Monitoring | Watch for: token refresh failures (check refreshConfigTokens logs), OAuth callback errors, rate limiter 429s in production. |